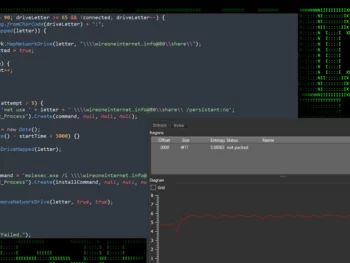
Network Threats: A Step-by-Step Attack Demonstration
Stick to this actual-everyday living network attack simulation, covering 6 measures from Initial Obtain to Facts Exfiltration. See how attackers continue being undetected with the simplest resources and why you need to have numerous choke details…
Network Threats: A Step-by-Step Attack DemonstrationRead More

DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions
The U.S. Division of Justice (DoJ) on Wednesday introduced the arrest of two co-founders of a cryptocurrency mixer identified as Samourai and seized the support for allegedly facilitating in excess of $2 billion in illegal transactions…
DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal TransactionsRead More

Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutiny
Google has when once again pushed its plans to deprecate 3rd-party monitoring cookies in its Chrome web browser as it is effective to handle exceptional competitiveness issues from U.K. regulators over its Privacy Sandbox initiative. The…
Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory ScrutinyRead More

State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
A new malware marketing campaign leveraged two zero-day flaws in Cisco networking equipment to supply tailor made malware and facilitate covert information selection on focus on environments. Cisco Talos, which dubbed the activity ArcaneDoor, attributing it…
State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for EspionageRead More

U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
The U.S. Treasury Department’s Business of Overseas Property Regulate (OFAC) on Monday sanctioned two corporations and 4 individuals for their involvement in destructive cyber routines on behalf of the Iranian Islamic Revolutionary Guard Corps Cyber Electronic…
U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber AttacksRead More
Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
Cybersecurity researchers have identified an ongoing attack marketing campaign which is leveraging phishing emails to supply malware known as SSLoad. The campaign, codenamed FROZEN#SHADOW by Securonix, also involves the deployment of Cobalt Strike and the ConnectWise…
Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt StrikeRead More
Get the latest news
Subscribe now and get the latest cyber security news in your email.









