Clubhouse denies it was ‘breached’ and states the facts is out there for any person to seize.
Clubhouse, the startup invitation-only chat application, is the most up-to-date social-media system to see mammoth troves of user details collected and posted in underground boards. An SQL file made up of the individual info of 1.3 million Clubhouse users has been posted in a hacker discussion board for free of charge.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Names, person IDs, image URL, amount of followers, Twitter and Instagram handles, dates that accounts ended up established and even the profile info of who invited them to the app are among the the details contained in the database, in accordance to CyberNews, providing threat actors critical information and facts which can be utilized from victims in phishing and other socially engineered scams.
For its portion, Clubhouse said that its users’ data remaining general public is not a bug, it’s just how the platform is developed:
This is deceptive and false. Clubhouse has not been breached or hacked. The info referred to is all public profile information and facts from our application, which anyone can accessibility by way of the application or our API. https://t.co/I1OfPyc0Bo
— Clubhouse (@joinClubhouse) April 11, 2021
The organization is not giving any other specifics and Clubhouse didn’t react to Threatpost’s ask for for added remark.
Clubhouse followers on Twitter were rapid to be aware the statement factors out a distinction without having any distinction to its exposed consumers.
“I fail to see what is phony … ” consumer Benjamin Maynard responded to the Clubhouse statement.
Leaky APIs Plague Social Media
Clubhouse’s phrases of provider prohibit facts scraping, nevertheless its API, by its have admission, is sitting down online with no protection in opposition to it.
“Clubhouse has conflicting consumer guidelines – becoming an invite-only platform and at the same time totally free-for-all consumer info,” Setu Kulkarni, vice president with WhiteHat Security stated. “All it takes is just one consumer to determine out the API for this kind of significant info egress of the tens of millions of buyers on the platform.”
Kulkani added that these platforms require to change to an API-1st security strategy.
“Testing APIs in generation is as if not additional significant than ever for not just vulnerabilities but also for business enterprise logic flaws that can result in unfettered obtain to consumer knowledge,” he explained.
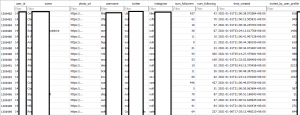
The Clubhouse databases. Click on to enlarge. Source: CyberNews.
CyberNews researcher Mantas Sasnauskas analyzed the Clubhouse information and claimed the privacy bug is built into the platform itself.
“The way the Clubhouse app is crafted allows any individual with a token, or via an API, to question the whole system of community Clubhouse consumer profile details, and it appears to be that token does not expire,” Sasnauskas claimed.
The CyberNews group added that the SQL file posted in the hacker discussion board only has Clubhouse-related information and facts and doesn’t include things like “sensitive information like credit history-card specifics or legal paperwork.”
Denying the Challenge
In the past two weeks, 533 million Facebook users’ details was leaked, LinkedIn saw scraping of 500 million people’s knowledge and now Clubhouse has specified up the information on a further 1.3 million men and women.
And as Politico Europe’s Nicholas Vinocur pointed out, they’ve all followed an eerily similar disclosure playbook: deny it at any time occurred.
In earlier 10 days:
533 million people’s details leaked at Facebook.
500 million people’s data leaked at LinkedIn.
1.3 million people’s details leaked at Clubhouse.
All deny the details was leaked or there was a problem of any type.
— Nicholas Vinocur (@NicholasVinocur) April 12, 2021
Facebook was in the same way vulnerable via their API, which Michael Isbitski from Salt Security instructed Threatpost is starting to be more frequent.
“Content scraping is a common attack sample,” Isbitski claimed in the wake of the Fb leak. “Organizations generally construct or integrate APIs, devoid of completely contemplating the abuse situations of the APIs.”
LinkedIn also out a statement in the wake of its incident, detailing the platform wasn’t technically “breached,” but that the details was public and scraped from the LinkedIn site.
To watch the LinkedIn consumer information file in the hacker discussion board, it expenses $2 worthy of of forum credits. The full database was up for auction in the four-figures vary.
“We have investigated an alleged established of LinkedIn data that has been posted for sale and have identified that it is truly an aggregation of information from a variety of internet websites and companies” that contains “publicly viewable member-profile facts that seems to have been scraped from LinkedIn,” the firm explained in a statement. “This was not a LinkedIn data breach, and no personal member account info from LinkedIn was incorporated in what we’ve been ready to evaluate.”
Information Scraping Fallout
“I do not anticipate that this will be the very last of these type of scraping incidents,” Isbitski predicted. “APIs are often the vehicle for performance and data. Social media businesses inherently design and style their platforms to be consumable, powering much of it with APIs. Attackers know this, and they go on to concentrate on APIs in scraping attacks, repurposing publicly available info for destructive purposes”
End users of all three of these social media platforms ought to be conscious they could be specific by email phishing strategies, so solid passwords and multi-factor authentication are essential. CyberNews features a individual info leak checker to aid users determine out if their information was compromised.
Ever speculate what goes on in underground cybercrime boards? Obtain out on April 21 at 2 p.m. ET all through a FREE Threatpost celebration, “Underground Markets: A Tour of the Dark Overall economy.” Professionals will take you on a guided tour of the Dark Web, including what is for sale, how considerably it fees, how hackers function collectively and the most current equipment accessible for hackers. Register here for the Wed., April 21 Are living function.

Some areas of this write-up are sourced from:
threatpost.com
Some parts of this article is sourced from CyberNews.com


 UK Sports Teams Boycott Social Media
UK Sports Teams Boycott Social Media