A study from GSMA and Trend Micro shows a about lack of security capabilities for non-public 5G networks (assume factories, good metropolitan areas, industrial IoT, utilities and a lot more).
As 5G non-public networks roll out in the coming decades, security may perhaps be a important issue for enterprises. A study introduced at Mobile Earth Congress on Monday demonstrates that big gaps persist in security capabilities among cell operators.
Some 68 p.c of operators currently offer private wi-fi networks to company consumers, with the rest planning to do so by 2025, according to the review, from the GSMA and Trend Micro. However, from a security point of view, these may possibly not be all set for primary time: 41 per cent of surveyed operators said they facial area troubles when it arrives to resolving vulnerabilities associated to 5G’s network virtualization, for occasion.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Also, 48 per cent of them mentioned they never have plenty of inner information or instruments to uncover and remedy security vulnerabilities at all. A contributing factor to the dilemma is a minimal pool of mobile-network security gurus for 39 per cent of surveyed operators.
5G Networks: Unique Architecture, Distinctive Risks
5G networks signify a sea improve from prior wireless networks in that they are mainly computer software-defined and virtualized. Network capabilities, historically defined in hardware, develop into virtual program abilities in 5G, all orchestrated by way of a versatile software program regulate aircraft. Even the air interfaces in the radio accessibility network (RAN) are software program-described in 5G.
The issue is that this raises the likelihood for rafts of exploitable vulnerabilities to arise all over the architecture in spots that were in no way exposed prior to.
“Because so much of the surroundings is virtualized, there will be a lot of software program producing photographs and tearing them down – the volume of virtualization is contrary to something we have expert so considerably,” William Malik, vice president of infrastructure procedures at Pattern Micro, informed Threatpost. “The risk there is that we do not know how properly the application will carry out under such huge hundreds. Every single encounter with dispersed program under load indicates that things will are unsuccessful, companies will fall and any vulnerability will be wide open for exploitation.”
The stakes are greater, as well. When it arrives to 5G, it is speedier and has decreased latency than earlier generations of wi-fi networks and will support a array of up coming-gen applications, together with good-manufacturing facility installations, good towns, autonomous automobiles, tele-medical procedures, sophisticated details analytics and artificial intelligence, among the many others. As such, 5G private networks will roll out in a wide range of settings, like factories, in which they’ll link sensors and a array of industrial internet of things (IoT) gadgets hospital and academic campuses stadiums industrial destinations this kind of as mines, ports and oil rigs and to help community-safety programs.
“These networks will manage sophisticated factories, distribution centers and logistics functions,” said Malik. “Think about the traffic at a big port – a lot of the operate is not carried out by men and women but by application software coordinated by scheduling and orchestration program. If you can get this in excess of, you can dump containers into Very long Seaside Harbor, or ship 2,000 pounds of Cream O’ Wheat to your neighbor. In the port of Amsterdam, the undesirable men took above the scheduling software program and essentially experienced containers whole of guns, prescription drugs, and in some conditions criminals, sent with out inspection into the port then smuggled onwards in the course of Europe.”
And, in its place of sending all info to a cloud for processing, 5G works by using multi-accessibility edge computing (MEC), which suggests that the network edge analyzes, processes and outlets the information created from endpoints. Collecting and processing data closer to the shopper reduces latency and delivers authentic-time functionality to high-bandwidth apps, but it also offers a new footprint to safe, with new info pools scattered about the network.
“We’re focusing on corporate 5G implementations, normally known as NPN – non-general public networks. In these environments the 5G sign is restricted to a precise area – a port, a distribution middle, a production facility – so we really don’t have random devices connecting, and each software and gadget can be authenticated (observe that this is not an architectural prerequisite but it is a seriously superior notion),” Malik stated. “Even with that, the 5G network will be a really effective way to transfer data close to the internet site, so if malware will get into a little something, it will unfold quick.”
The study located that half (51 per cent) of the operators reported that MEC is a key component of their method for addressing enterprises’ private network desires inside of the up coming two many years. Nevertheless only 18 per cent of surveyed operators offer security for both equally the edge and endpoints.
“Operators are fully commited to security, mindful that the combination of cloud, facts and IoT threats usually means that cyber-pitfalls are far higher in the 5G era,” explained Sylwia Kechiche, principal IoT analyst for GSMA intelligence, in a media statement. “Yet our new analysis with GSMA reveals a regarding deficiency of applications and information inside of these companies.”
Greatest Procedures for 5G Private Network Security
“The negative guys will attempt to acquire above the 5G network by possibly sneaking some rogue software package into the blend, making use of a source-chain attack like SolarWinds or sneaking previous authentication to launch their very own processes that can cryptomine (thieving methods), exfiltrate facts or established off a ransomware attack,” Malik explained.
Even however security capabilities are lagging for now, just about fifty percent (45 p.c) of operators in the survey explained they think about it really vital to commit in security to reach their very long-phrase business earnings objectives – as opposed with just 22 per cent in 2020.
A comprehensive 44 % of operators explained they have seen elevated expansion in demand from customers for security products and services from their company customers thanks to COVID-19, when 77 % of operators search to security as a major opportunity for earnings technology, forecasting that 20 percent of 5G profits will arrive from security add-on providers.
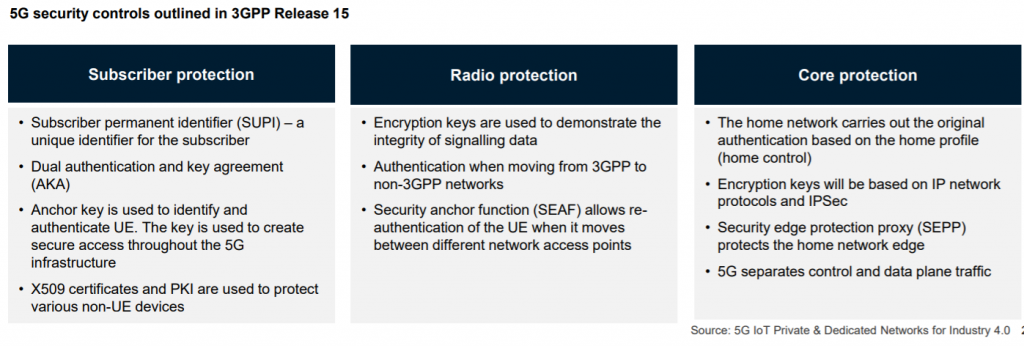
The 3GPP, the specifications human body in cost of wi-fi network specs, has designed some security controls into the 5G spec:
There is far more that carriers can do, on the other hand, to aid differentiate their offerings, according to Malik.
“Best techniques for securing these NPN environments would consist of authenticating everything and everyone – which is the notion behind zero rely on,” Malik informed Threatpost. “You have to show you are who you say you are in advance of you can do anything at all on the network.”
It’s also a great thought to log and audit message visitors and to use instruments to notice when loads of details would seem to be flowing exactly where it shouldn’t, he extra.
“Also, use instruments to detect processes that are misbehaving – like a procedure that commences encrypting everything it can touch,” in accordance to Malik. “To enable get well from an attack, get regular backups and make certain they are valid. Also, acquire technology from reliable distributors and use reputable integrators to hook factors up.”
Sign up for Threatpost for “Tips and Methods for Much better Risk Hunting” — a Are living celebration on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Discover from Palo Alto’s Device 42 industry experts the greatest way to hunt down threats and how to use automation to aid. Register HERE for no cost!

Some elements of this short article are sourced from:
threatpost.com


 NVIDIA Patches High-Severity GeForce Spoof-Attack Bug
NVIDIA Patches High-Severity GeForce Spoof-Attack Bug