A seller uncovered the records, which have been accessible with no password or other authentication, most likely because of a cloud-storage misconfiguration.
Much more than 1 billion data for CVS Health customers were being left in the databases of a third-party, unnamed vendor – exposed, unprotected, online. Scientists explained the facts points exposed could be strung alongside one another to build an extremely individual snapshot of someones’s health care condition.
The glitch is most likely owing to human error, security researcher Jeremiah Fowler said in a publish on WebsitePlanet on Thursday: In other words, it’s in all probability nonetheless an additional incidence of rampant misconfiguration which is plaguing cloud-dependent storage, major to exposure of delicate information on an interior network.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In accordance to Fowler’s write-up, researchers at WebsitePlanet – a portal for web builders and internet entrepreneurs – identified the non-password-guarded database, which experienced no variety of authentication in location to protect against unauthorized entry, on March 21. They coordinated with Fowler in documenting their discovery and on that exact working day, following they contacted CVS Wellbeing, the naked database was closed off from community perspective.
CVS Wellbeing is the mother or father company guiding various residence models, together with the CVS Pharmacy retail pharmacy chain CVS Caremark, a pharmacy positive aspects supervisor and Aetna, a wellbeing insurance provider.
A CVS spokesperson verified the researchers’ conclusions, expressing that CVS Overall health experienced been notified of the publicity of a publicly accessible databases that contained non-identifiable CVS Health and fitness metadata. On investigation, they established that the database was hosted by a third-party vendor, whose name the company didn’t disclose. The databases did not consist of any individually identifiable information and facts (PII) of prospects, associates or people, the firm stated in a statement, and the databases was speedily taken down.
As the researcher’s report signifies, there was no risk to clients, members or individuals, and we labored with the seller to quickly just take the database down. We have dealt with the issue with the vendor to avert a recurrence and we thank the researcher who notified us about this make any difference. —CVS Health and fitness statement.
What Was in That CVS Cache of Knowledge?
Fowler stated in his submit that there was in point more than enough information to derive customers’ PII, together with their email addresses. The total dimension of the database was 204 GB, according to the scientists. It held 1.1 billion documents, or, to be precise, 1,148,327,940 information. They were labeled “production” and provided information and facts typed into research bars, these kinds of as the facts forms increase to cart, configuration, dashboard, index-sample, extra refinements, buy, get rid of from cart, look for, server.
The data also uncovered fields named Visitor ID, Session ID and device data, this sort of as no matter whether buyers ended up making use of an iPhone, an Android, an iPad or a desktop Pc. The workforce famous that by stringing with each other the info, they could expose email messages that could be qualified in a phishing attack, in social engineering, or “potentially used to cross-reference other steps.”
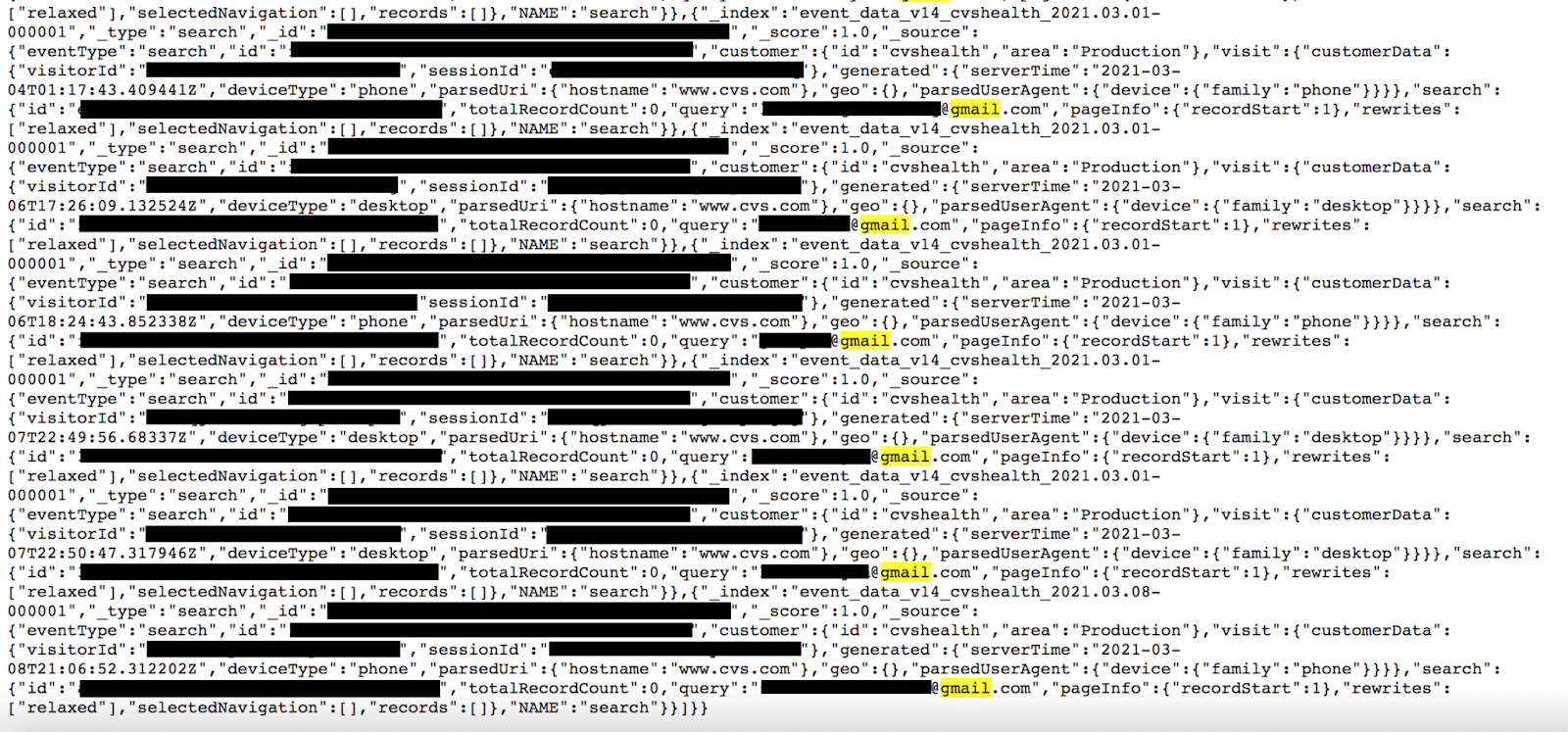
Redacted CVS Wellbeing consumer documents. Supply: WebsitePlanet
As nicely, the information gave a “clear being familiar with of configuration settings, exactly where data is saved and a blueprint of how the logging services operates from the backend,” according to the advisory.
In hunting for PII, the scientists executed numerous research queries for prevalent email extensions, such as Gmail, Hotmail and Yahoo, they explained. They ended up rewarded with effects for every single query inside the dataset, indicating that the records did in fact comprise email addresses. Fowler mentioned that, provided how a lot of individual email addresses are formatted making use of parts or all of the user’s title, he was ready to identify “a tiny sampling of men and women by simply exploring Google for the publicly uncovered email tackle.”
The records also contained the knowledge sorts Visitor ID and Session ID, indicating the things that site visitors searched for, such as medicines, COVID-19 vaccines and other CVS solutions. All of this knowledge, strung together, could have developed a snapshot of non-public information about individuals’ well being, Fowler said.
“Hypothetically, it could have been possible to match the Session ID with what they searched for or extra to the purchasing cart in the course of that session and then attempt to discover the purchaser making use of the uncovered e-mails,” he stated in the advisory.

Source: WebsitePlanet.
The CVS representative who dealt with the researchers reported that no matter what e-mail were being uncovered in the databases didn’t occur from CVS customer accounts. Instead, they were being entered into the lookup bar by visitors by themselves – presumably, by blunder.
“The look for bar captures and logs all the things that is entered into the website’s research perform and these information ended up saved as log data files,” the advisory discussed. “When examining the cellular version of the CVS web site it is a feasible principle that visitors may perhaps have thought they ended up logging into their account, but ended up definitely entering their email tackle into the lookup bar.”
The queries ended up formatted as celebration form parameters and had been established to search. The email addresses are values for a parameter named question, Fowler ongoing, which “could describe how so several email addresses finished up in a databases of product lookups that was not intended to discover the customer.”
In addition, the information show what device customers utilized, with a bulk of the queries coming from telephones and cell devices these kinds of as iPhones or Androids, as effectively as some searches coming from desktop desktops.
Database Publicity: A Bonanza for Cyberattackers
Sad to say, the action logging that exposed all this info is a “necessary evil,” the crew noticed – a person that can lead to the exposure of sensitive information.
“Tracking all exercise from a web site or ecommerce system will help develop precious insights about visitors and buyers,” the advisory defined. “This logging and monitoring can generally include metadata or mistake logs that inadvertently expose far more sensitive information.”
The uncovered search logs were from lookups completed on both equally CVS Health and CVS.com, and offered “valuable analytical data to see what consumers are wanting for and if they are locating the solutions they want,” the workforce stated. That contains the likelihood that facts about configuration, applications, program, running programs and establish facts were uncovered: knowledge that could discover opportunity vulnerabilities if they had been unpatched or out-of-date.
That is information that cybercriminals or adversarial country-states can exploit, the workforce explained. “Often they use the very same methods as authentic security researchers to establish publicly uncovered knowledge,” in accordance to the advisory. “Each file of information serves as a puzzle piece to present a larger image of an organization’s network or data-storage techniques.”
Cloud Misconfigurations Galore
Thanks to the explosive growth of cloud-primarily based facts storage, misconfigurations like these are turning out to be all as well frequent, explained PJ Norris, senior devices engineer at cybersecurity business Tripwire. “Exposing delicate info doesn’t require a refined vulnerability, and the immediate development of cloud-primarily based data storage has uncovered weaknesses in processes that leave knowledge available to any individual,” he claimed by way of email to Threatpost on Thursday.
In September, a survey of 2,064 Google Cloud buckets from Comparitech found that 6 per cent of all Google Cloud buckets are misconfigured, left open to the public internet for anybody and everyone to see – which includes passports, beginning certificates and personal profiles from children in India, and a Russian web developer’s email server qualifications and chat logs.
In March, arts-and-crafts retailer Passion Foyer remaining 138GB of sensitive information open to the general public internet – such as a slew of buyer information and facts – owing to a cloud-bucket misconfiguration.
“A misconfigured database on an inner network may not be discovered, and if seen, could possibly not go public, but the stakes are larger when your knowledge storage is specifically linked to the Internet,” Norris pointed out. “Organizations must identify procedures for securely configuring all programs, which includes cloud-based storage, like Elasticsearch and Amazon S3. At the time a procedure is in position, the devices will have to be monitored for alterations to their configurations. These are solvable complications, and equipment exist these days to aid.”
Frequent Misconfigurations
Ray Canzanese, danger exploration director at Netskope, claimed that the CVS Wellness publicity is frequent in infrastructure-as-a-services (IaaS) vendors this sort of as Amazon Web Solutions (AWS), Azure and Google Cloud. Common misconfigurations crop up in security teams, network ACLs (NACLs) and firewall procedures, he said through email to Threatpost on Thursday. In fact, Netskope lately analyzed public exposure of compute infrastructure in IaaS environments across the a few big IaaS vendors, and found that about 35 % of compute circumstances expose at minimum just one service to the Internet.
Netskope proposed that, to prevent this sort of exposures, companies must scan their have cloud environments instantly to find and lock down uncovered assets. Canzanese also suggested zero-have confidence in network architecture as a suggests to give workforce safe access to cloud means, no matter whether they are hosted on-prem or in the cloud, without exposing them to the internet.
Be a part of Threatpost for “Tips and Tactics for Improved Risk Hunting” — a Reside occasion on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Study from Palo Alto’s Device 42 professionals the best way to hunt down threats and how to use automation to enable. Sign-up Right here for totally free.

Some areas of this article are sourced from:
threatpost.com


 Hackers Can Spy on Peloton Workouts
Hackers Can Spy on Peloton Workouts