Vulnerability management carries on to problem corporations, as they experience tens of 1000’s of bugs with just about every scan.
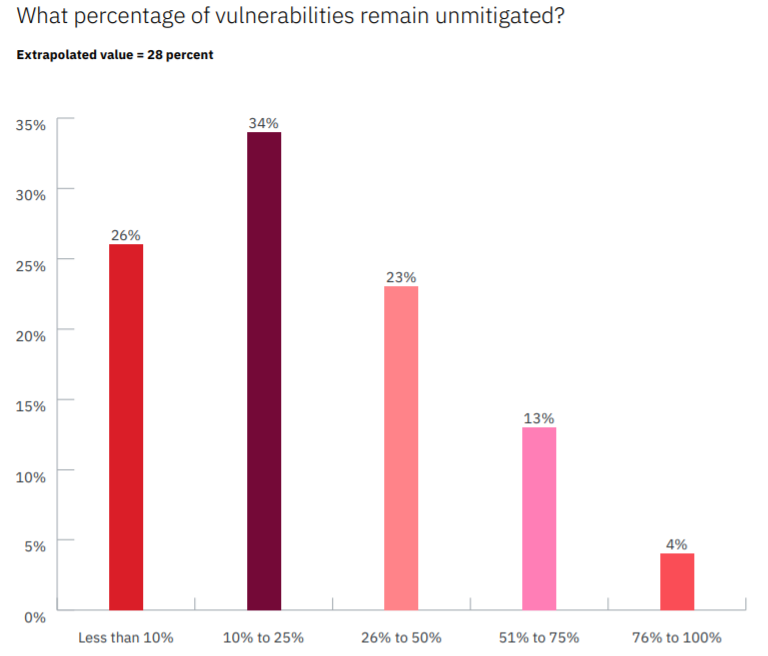
Big providers find an average of 779,935 particular person security bugs when working regimen vulnerability scans and in excess of the study course of 6 months, an common of 28 % of people vulnerabilities will keep on being unmitigated. This leaves numerous of these businesses in a sitting down-duck posture for cybercriminals, rearchers stated.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Which is in accordance a examine from the Ponemon Institute, The Condition of Vulnerability Administration, which surveyed 1,800+ IT pros at businesses with additional than 1,000 workforce. The survey found that the typical backlog of bugs for these businesses totals a whopping 57,555 determined vulnerabilities.
Plainly, prioritization will become critical to vulnerability administration in this scenario having said that, the survey also found that corporations have issue in reaching that. A full 57 p.c of respondents explained their corporations never know which vulnerabilities pose the greatest risk to their enterprises.

And only a quarter (25 %) explained they are able to prioritize patching based mostly on which assets are the most essential to the business enterprise.
About 37 % of respondents said their main method for prioritization is the identification of which vulnerabilities are weaponized. This isn’t a undesirable technique on the surface offered that prison external attacks were being the most common cited root result in of data breaches in the survey (34 %). Exterior assaults ended up adopted by human error (24 percent), and program glitches and destructive insider threats accounted for the relaxation.
“Even if they prioritize vulnerabilities precisely, the system of remediation can come to be a headache as groups try to procedure the information and facts — who owns the vulnerable asset, is there a patch, what if the patch does not operate, when is an acceptable time for patching, etc.,” spelled out scientists from IBM X-Pressure, in the report, produced Monday. They extra, “Every organization has an enormous sum of data, a lot of which is siloed, offering every single staff a various point of view of risk. The fragmented viewpoints avoid observing the entire risk picture, which can also lead to important vulnerabilities staying deprioritized or neglected.”
Only 21 p.c of respondents mentioned their corporations are “highly effective” in patching vulnerabilities in a well timed way. In accordance to the research, it can take pretty much a thirty day period (28 times) to patch after a critical or superior-risk vulnerability is detected on-premises, and 19 days if it is detected in the cloud.
All of this leaves a wide swath of firms at risk for compromise from regarded bugs. And in truth, out of the 53 percent of respondents who explained their corporations have had a data breach in the past two a long time, 42 percent of them mentioned they happened because a patch was not used for a acknowledged vulnerability.
As to the hurdles to having on leading of vulnerability administration, Ponemon identified that the use of guide procedures for patching remains a bugbear. Half of respondents explained their organizations are at a disadvantage in responding to vulnerabilities simply because they use handbook procedures and additional than half (53 per cent) mentioned that IT team spends extra time navigating manual processes than responding to vulnerabilities.
Also, the survey uncovered that most corporations do not have a one view of the entire vulnerability management lifecycle, such as exception managing. Only 27 p.c of respondents say they have visibility into the vulnerability management lifecycle, producing it tough to determine how well their corporations are prioritizing, remediating and patching vulnerabilities.
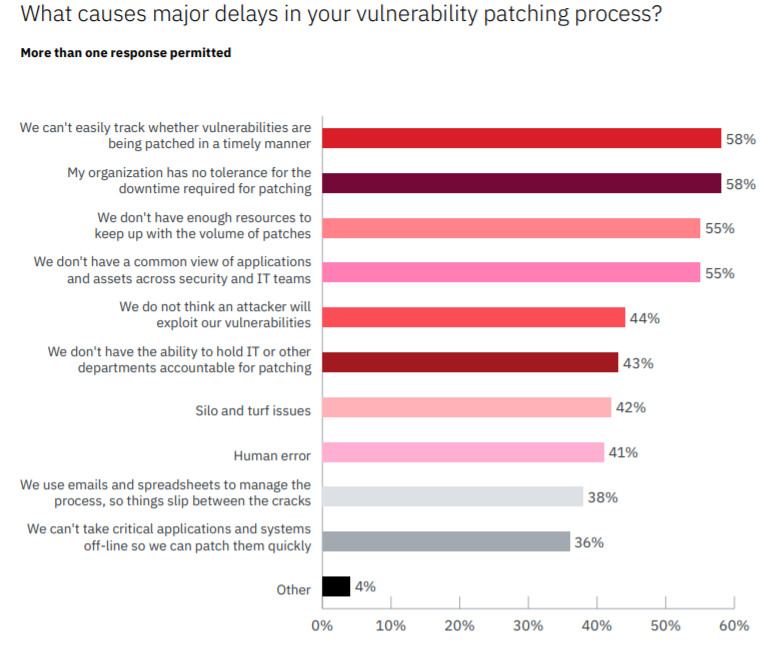
Then there’s the issue of staffing and the ongoing cybersecurity expertise hole: Only about fifty percent (49 per cent) of respondents reported their corporations have sufficient staff to patch in a well timed method, although just 41 p.c claimed the IT security workforce has the essential patching expertise and instruction to deal with vulnerabilities.
“Instead of having a programmatic tactic to vulnerability management, many businesses choose an anecdotal method,” according to X-Drive. “They divvy up and plow by way of an Excel spreadsheet, which might have 1000’s to hundreds of thousands of vulnerabilities. The spreadsheet process may function for one workforce in the business, but when it is rolled out across an entire enterprise, chaos can ensue.”
Cloud Issues
Towards this basic backdrop, the Ponemon survey also observed that corporations face specific worries when storing business-critical apps in containers in the cloud (on average, 38 p.c of mission-critical purposes are in containers).
Of those respondents that have individuals purposes in the cloud, 56 p.c said they’re uncertain as to no matter if the apps in the containers were being analyzed to obtain and fix large-risk vulnerabilities that an attacker may well exploit.
And still, only 38 per cent of respondents mentioned identifying vulnerabilities in cloud environments is extra hard and intricate than pinpointing vulnerabilities on-premises. And 35 per cent of respondents said patching in the cloud is a lot more tough and complicated than on-premises.
“Organizations tend to have diverse groups and policies when it arrives to cloud security vs . on-premises security,” according to X-Drive in the report. “Because the cloud footprint can grow so rapidly and have a various governance structure, the cloud security teams are drowning. Frequently, when apps are moved into the cloud environment, they do not get the similar level of focus — a lot less frequent penetration testing, vulnerability scanning, and so on.”
It’s the age of distant functioning, and businesses are going through new and bigger cyber-pitfalls – regardless of whether it is collaboration platforms in the crosshairs, evolving insider threats or issues with locking down a a great deal broader footprint. Come across out how to handle these new cybersecurity realities with our complimentary Threatpost Book, 2020 in Security: Four Stories from the New Risk Landscape, offered in conjunction with Forcepoint. We redefine “secure” in a get the job done-from-household world and give powerful real-planet finest techniques. Click on in this article to obtain our E-book now.


 61% of Airlines Have No Revealed DMARC Record, Prospects Vulnerable to Email Fraud
61% of Airlines Have No Revealed DMARC Record, Prospects Vulnerable to Email Fraud