Misconfigured dashboards are yet yet again at the coronary heart of a popular, ongoing cryptocurrency marketing campaign squeezing Monero and Ethereum from Kubernetes clusters.
Microsoft has noticed a new, popular, ongoing attack targeting Kubernetes clusters jogging Kubeflow scenarios, in purchase to plant destructive TensorFlow pods that are utilized to mine for cryptocurrency.
The Kubeflow open-supply project is a popular framework for running machine mastering (ML) jobs in Kubernetes, although TensorFlow is an end-to-conclusion, open up-source ML system.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Specified that the attack is nevertheless energetic, any new Kubernetes clusters that operate Kubeflow could be compromised, according to Microsoft.
On Tuesday, Microsoft security researchers warned that towards the conclusion of May well, they noticed a spike in deployments of TensorFlow pods on Kubernetes clusters – pods that are functioning legit TensorFlow photographs from the official Docker Hub account. But a nearer search at the entry place of the pods unveiled that their purpose is to mine cryptocurrency.
Yossi Weizman, senior security exploration software program engineer at Microsoft’s Azure Security Center, said in a write-up on Tuesday that the “burst” of these destructive TensorFlow deployments was “simultaneous,” indicating that the attackers initially scanned the clusters, stored a listing of opportunity targets, and then pulled the trigger on all of them at after.
Weizman discussed that the attackers utilised two different illustrations or photos: The initial is the most current edition of TensorFlow (tensorflow/tensorflow:most up-to-date) and the 2nd is the newest version with GPU assist (tensorflow/tensorflow:most recent-gpu). The use of TensorFlow illustrations or photos in the cluster “makes a large amount of sense,” Weizman stated, offered that “if the photographs in the cluster are monitored, usage of [a] authentic graphic can prevent attackers from remaining discovered.”
Another cause why the attackers’ option is easy to understand is that the TensorFlow picture they chose is a easy way to run GPU responsibilities employing CUDA, which “allows the attacker to optimize the mining gains from the host,” he reported. CUDA is a toolkit created by NVIDIA, employed to establish, optimize and deploy GPU-accelerated applications.
Equivalent to Past Year’s Cryptomining Attack
The freshly found out attack is related to a cryptocurrency mining attack that Microsoft documented previous June. That before campaign also specific Kubeflow workloads, exploiting misconfigured dashboards to launch a prevalent XMRIG Monero-mining marketing campaign. Speedy-forward a year, and this recently found out cryptomining pulls a similar move, utilizing uncovered Kubeflow interfaces for working cryptocurrency mining containers.
The most recent campaign provides some tweaks: As Weizman explained it, this time around, the attackers abused the entry to the Kubeflow centralized dashboard in order to make a new pipeline.
As Weizman thorough in the publish, Kubeflow Pipelines is a platform for deploying ML pipelines, primarily based on Argo Workflow, which an open up-supply, container-indigenous workflow engine for orchestrating parallel employment on Kubernetes. Pipeline involves a collection of steps, each individual just one of them as an impartial container, that alongside one another sort a ML workflow. The graphic of the container that operates in every single action is determined in the pipeline configuration, he stated.
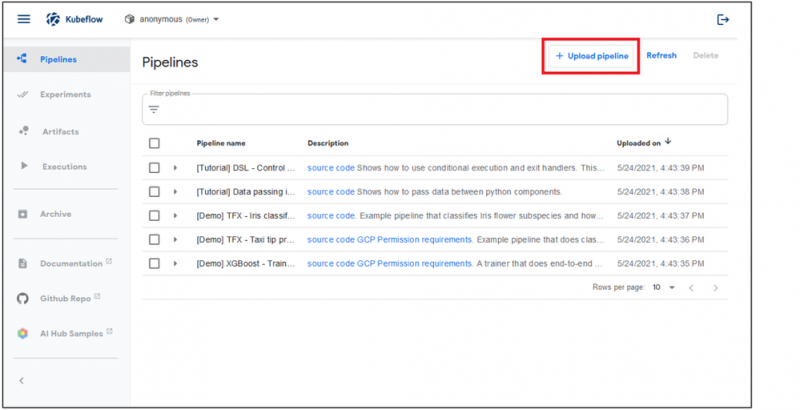
Kubeflow pipelines. Supply: Microsoft
Accessibility to the pipeline’s person interface is essential in this attack: When attackers acquire entry to that dashboard, they can develop a new cluster in the pipeline. In this scenario, that suggests containers that operate TensorFlow photos that established up cryptocurrentcy mining.
All of the destructive pods had been set up with the exact pattern: “sequential-pipeline-random sample”. That title is originated in the “generateName” field of the Argo Workflow object which is employed for creating the pipeline, Weizman mentioned.
At the very least two pods ended up deployed on every cluster: 1 for CPU mining, and the other for GPU mining. The GPU container applied the open up-source Ethminer to mine Ethereum, although the CPU miner applied the aforementioned open up-source XMRIG Monero miner.
As element of the ongoing attack flow, the attackers are applying a reconnaissance container – also run from a TensorFlow pod – to scoop up data about the setting, this kind of as GPU and CPU particulars, in preparing for mining.
What to Do to Avoid a Cyberattack
Microsoft advised that people who operate Kubeflow must make sure they’ve locked down the centralized dashboard so it is not insecurely exposed to the internet. If Kubeflow has to be uncovered to the internet, make guaranteed it needs authentication.
Microsoft gave the example of Kubeflow getting utilised to help OpenID Connect (OIDC) using Azure Lively Directory for Azure deployments. In order to get all the pods jogging in the cluster in JSON structure, operate: kubectl get pods –all-namespaces -o json …
… and research for containers that run TensorFlow photographs. If they exist, inspect the entry stage of people containers, Microsoft encouraged.
Cryptomining: Direct Weights That Bog Down the Cloud
Yaniv Bar-Dayan, CEO and co-founder at Vulcan Cyber, stated that cryptomining is nothing at all to shrug off, supplied the strike it places on cloud means.
“While cryptomining campaigns can look innocuous, they set excess strain on cloud resources, inflict supplemental cloud and utility fees on attacked get-togethers, shorten the lifespan of IT gadgets and cause needless company disruption,” he informed Threatpost via email on Thursday.
These strategies also spotlight organizations’ risk of publicity, he observed – in other phrases, if an attacker can pull off a cryptomining attack, they can pull off even even worse. “If an attacker can start a cryptomining marketing campaign on an organization’s infrastructure, it is probably that they can launch ransomware as nicely or attain access to facts, mental property, staff files and other at-risk belongings that can problems a business enterprise if breached,” he continued.
Bar-Dayan stated that Vulcan Cyber suggests taking the appropriate techniques for protection. For illustration, make certain correct configurations, and, echoing Microsoft, make guaranteed that devices aren’t exposed to the open internet. Also, make absolutely sure the appropriate identity and access controls are in spot.
Obtain our exclusive Absolutely free Threatpost Insider Ebook, “2021: The Evolution of Ransomware,” to aid hone your cyber-defense procedures versus this increasing scourge. We go past the status quo to uncover what’s upcoming for ransomware and the connected emerging pitfalls. Get the total tale and Down load the E-book now – on us!

Some pieces of this post are sourced from:
threatpost.com


 #Infosec21: Lack of Vision Explains Cyber Skills Shortage
#Infosec21: Lack of Vision Explains Cyber Skills Shortage