Attackers sent 52M destructive messages leveraging the likes of Place of work 365, Azure, OneDrive, SharePoint, G-Suite and Firebase storage in Q1 2021.
Menace actors are cashing in on the swift change to cloud-centered company services in the course of the pandemic, by hiding guiding ubiquitous, dependable services from Microsoft and Google to make their email phishing frauds look legit. And it is performing.
In point, in the first a few months of 2021 alone, scientists found 7 million destructive email messages sent from Microsoft 365 and a staggering 45 million despatched from Google’s infrastructure, Proofpoint described, including that cybercriminals have used Business 365, Azure, OneDrive, SharePoint, G-Suite and Firebase storage to ship phishing e-mail and host attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The malicious concept quantity from these trustworthy cloud companies exceeded that of any botnet in 2020, and the trustworthy name of these domains, including outlook.com and sharepoint.com, increases the problem of detection for defenders,” the report, issued Wednesday, spelled out. “This authenticity notion is critical, as email recently regained its status as the top rated vector for ransomware and, menace actors significantly leverage the source chain and associate ecosystem to compromise accounts, steal credentials and siphon funds.”
Simply because breaching a single account could potentially present sprawling accessibility, ProofPoint reported that 95 p.c of companies ended up qualified for cloud account compromise, and of individuals, much more than 50 % had been prosperous. Moreover, extra than 30 per cent of those companies that have been compromised “experienced submit-access action together with file manipulation, email forwarding and OAuth action.”
When attackers have qualifications, they can very easily transfer in and out of a range of expert services and use people to mail extra, convincing phishing emails.
Proofpoint presented numerous examples of strategies hiding at the rear of Microsoft and Google that tried to fraud users into offering up their facts or providing malware.
A person message utilized a Microsoft SharePoint URL, which purported to backlink to a doc outlining COVID-19 suggestions. Proofpoint’s staff described that this information was despatched to 5,000 users in the transportation, producing and business expert services sectors.
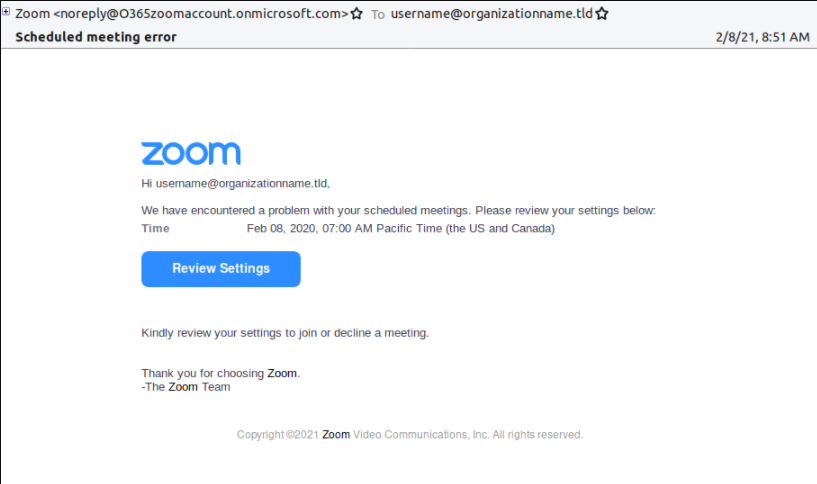
Another illustration delivered by Proofpoint attempted to use the domain identify “onmicrosoft.com” to produce a faux online video-conferencing credential harvesting email, which researchers observed was delivered to about 10,000 customers.
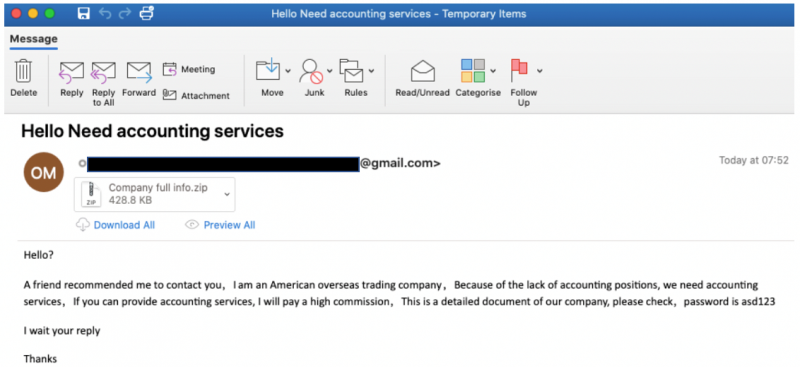
Attackers utilised Gmail to host an additional marketing campaign starting in March, which sent a fraudulent rewards concept alongside with a Microsoft Excel attachment, which when macros were enabled, sent The Trick banking trojan to steal qualifications.
An additional Gmail-hosted attack in February tries to induce end users to access zipped MS Word paperwork by coming into their passwords. After opened, macros were being enabled it sent Xorist ransomware.
Attackers’ use of Gmail and Microsoft to lend a patina of legitimacy to their e-mail is section of a wider craze: Danger actors are making ever more convincing lures.
And at the tail close of May, Cofense flagged a phishing marketing campaign using an Office environment SharePoint topic to bypass security gateways.
“Our investigate clearly demonstrates that attackers are employing equally Microsoft and Google infrastructure to disseminate destructive messages and target persons, as they leverage well known cloud-collaboration instruments,” The Proofpoint report additional. “When coupled with heightened ransomware, offer chain, and cloud account compromise, sophisticated men and women-centric email protection must continue to be a best precedence for security leaders.”
Down load our exclusive Free of charge Threatpost Insider E-book, “2021: The Evolution of Ransomware,” to enable hone your cyber-defense tactics towards this developing scourge. We go past the position quo to uncover what is following for ransomware and the relevant emerging hazards. Get the full tale and Down load the E book now – on us!

Some sections of this article are sourced from:
threatpost.com


 As digital innovation accelerates, what is the next cyber investment unicorn?
As digital innovation accelerates, what is the next cyber investment unicorn?