An APT team has started seriously relying on cloud services like Azure Active Directory and OneDrive, as well as open-source instruments, to obfuscate its attacks.
Microsoft has suspended 18 Azure Lively Directory purposes that ended up currently being leveraged for command-and-management (C2) infrastructure by what it claims is a Chinese country-state actor.
When Microsoft expert services like Azure Energetic Directory (Ad) – its cloud-centered id and entry management provider – are well-liked amongst enterprises, cybercriminals are also swooping in on these expert services to boost the weaponization of their malware payload, attempt to gain command and management all the way to the server, and obfuscate detection. One these types of threat team a short while ago noticed leveraging these cloud providers and open up supply tools is what Microsoft phone calls Gadolinium, a Chinese nation-point out activity group that has been compromising targets for nearly a 10 years.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Immediately after compromising victim units, Gadolinium was location up AD accounts to obtain commands from and send out stolen information to its C2 server. But further than that, the danger team has also saved stolen data in Microsoft’s file hosting services and synchronization support, OneDrive launched attacks using the open source PowershellEmpire toolkit and employed GitHub to host commands.
“Gadolinium has been experimenting with making use of cloud expert services to provide their assaults to raise both operation speed and scale for yrs,” reported Ben Koehl and Joe Hannon, with Microsoft’s Threat Intelligence Center, in a report posted Thursday.
Developed Assaults
Gadolinium is also recognized as APT40, which scientists like FireEye have assessed with “moderate confidence” is a condition sponsored espionage actor attributed to China. While previously Gadolinium has targeted worldwide maritime and wellness industries, Microsoft claimed a short while ago it has observed recently expanded targeting for the danger team to incorporate the Asia Pacific area and other targets in increased instruction and regional govt corporations.
In mid-April 2020 the risk actors ended up detected sending spear-phishing e-mails with destructive attachments, with lures relating to the COVID-19 pandemic. When opened, the connected PowerPoint file (20200423-sitrep-92-covid-19.ppt), would fall a file, doc1.dotm, which then has two payloads that operate in succession.
These involve a payload that turns off a type verify (DisableActivitySurrogateSelectorTypeCheck), when the 2nd loads an embedded .Web binary that downloads a .Png impression file.
“The .png is actually PowerShell which downloads and uploads faux png files using the Microsoft Graph API to https://graph.microsoft.com/v1./push/root:/onlinework/get hold of/$($ID)_1.png:/content where by $ID is the ID of the malware,” explained scientists.
At the rear of the scenes, these attacks relied on a bundle of Microsoft companies and open up source tooling – which Microsoft stated has been a regular pattern in the latest decades for many nation-point out activity groups migrating to open up resource tooling.
Gadolinium Leveraging Cloud Expert services
Scientists mentioned that historically Gadolinium has leveraged custom made-crafted malware households – but analysts have been capable to recognize these and protect against them.
In reaction, the danger actor has begun experimenting with cloud applications to enable it sidestep detection of its assaults, setting up in 2018, when the risk group selected to use GitHub to host instructions. Many cloud services routinely supply a absolutely free trial or just one-time payment account featuring (by means of PayGo), and malicious actors have found methods to consider edge of these legit organization choices, mentioned scientists.
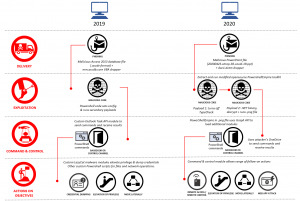
Gadolinium’s attack vectors. Credit score: Microsoft
“By developing no cost or PayGo accounts, they can use cloud-based technology to build a malicious infrastructure that can be established rapidly then taken down before detection or supplied up at minimal price,” reported scientists.
This past calendar year, Gadolinium has also began modifying portions of its attack vector, as an alternative making use of open-source toolkits to obfuscate its action and make it additional difficult for analysts to keep track of.
Microsoft stated that the 18 Azure Lively Directory applications that were being suspended have been aspect of Gadolinium’s PowerShell Empire infrastructure, which is a modified model of the open source PowershellEmpire toolkit. This is a toolkit that permits attackers to load added modules to infected personal computers through Microsoft Graph API phone calls. It delivers a command and management module that utilizes the attacker’s Microsoft OneDrive account to execute instructions and retrieve effects amongst attacker and victim programs.
“The attacker uses an Azure Lively Listing software to configure a victim endpoint with the permissions required to exfiltrate info to the attacker’s very own Microsoft OneDrive storage,” said scientists. “From an endpoint or network checking standpoint the activity at first appears to be relevant to dependable applications making use of trustworthy cloud services APIs and, in this state of affairs, no OAuth permissions consent prompts manifest.”
Some parts of this article is sourced from:
threatpost.com


 FinSpy Spyware for Mac and Linux OS Targets Egyptian Organisations
FinSpy Spyware for Mac and Linux OS Targets Egyptian Organisations