A researcher combed as a result of the Twitch leak and observed what they claimed was evidence of PayPal chargebacks with names and e-mails employees’ emails and more.
Twitch people, if you haven’t improved your password nevertheless, go. Now. Do it.
Your email and password may well by now have been leaked – unhashed, unencrypted, in cleartext.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Scientists have been squeezing the reside-streaming service’s innards after 135 gigabytes of its internal knowledge were being smeared all more than 4chan by an anonymous poster on Tuesday.

It is a horrific leak that incorporated the Amazon-owned service’s source code, opinions courting back to the dawn of Twitch time, security equipment, an unreleased Amazon Match Studios competitor to Steam (codenamed Vapor), a record of of the optimum-paid channels in addition how much they ended up paid (FYI: A channel operated by voice actors took the leading spot, producing about $10 million in two several years), and much more.
E-mail, Passwords in Plaintext
Given that Tuesday, the “and more” has been unpacked to expose what a lot of gurus predicted: Specifically, this was not just a direct attack on Twitch, in spite of the attacker calling the services a “disgusting poisonous cesspool.”
Relatively, it was also an attack on Twitch customers, whose personalized data was breached.
An independent security researcher who asked for anonymity uncovered streamers’ email addresses and passwords in basic textual content in one exposed datastore. The researcher shared the adhering to Twitch screenshot with PrivacySharks, which subsequently shared it with Threatpost.

Emails and passwords in obvious textual content. Supply: PrivacySharks.
When Threatpost contacted Twitch, a representative sent this assertion: “At this time, we have no sign that login credentials have been exposed. We are continuing to look into. Additionally, full credit score-card quantities are not stored by Twitch, so total credit rating-card quantities have been not exposed.”
It Was a Misconfigured Swap
On Wednesday, Twitch disclosed that “some data” was exposed to the internet due to “an mistake in a Twitch server configuration adjust that was subsequently accessed by a destructive 3rd party.” It mentioned that its groups ended up urgently investigating, but that it hadn’t discovered any proof that login qualifications experienced been exposed.
“We are continuing to investigate,” Twitch explained.
On Thursday, the company reset all keys “out of an abundance of caution” and directed streamers to get new keys in this article.
PayPal Chargebacks, Scraping Competitors’ Web-sites, Employee Details
In spite of Twitch’s failure to find any proof of uncovered user data, the impartial researcher shared with PrivacySharks other datastores made up of particular details, like a PayPal file made up of information on much more than 1,000 chargebacks made from Twitch to numerous platforms.
The information involve full names, email addresses, buyer opinions and quantities. The redacted screenshot down below is an illustration of what the file contained:
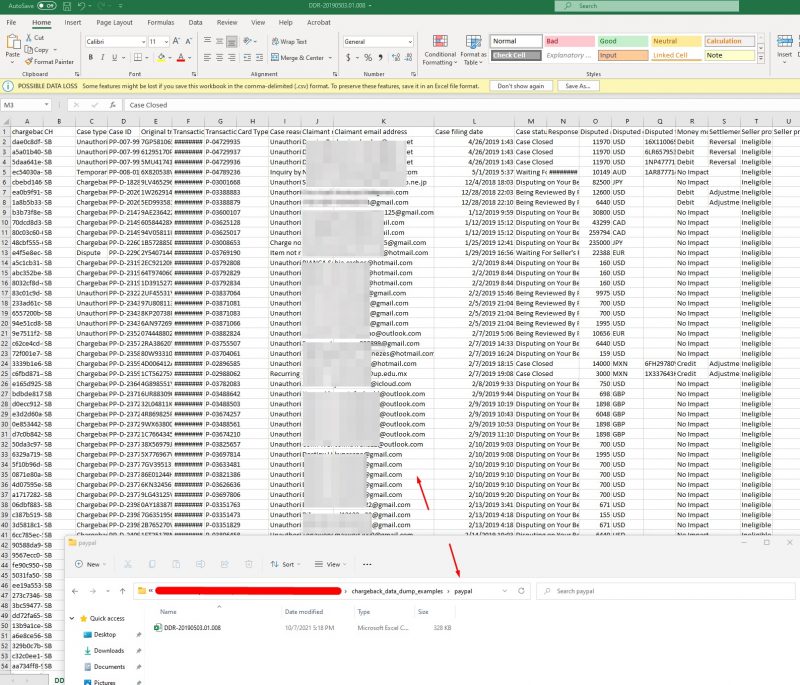
PayPal chargebacks built from Twitch to numerous platforms, which includes identify, email, consumer feedback and amount of money. Supply: PrivacySharks.
The anonymous leaker identified as Tuesday’s 135 gigabytes knowledge dump “part one” of the leak, but they didn’t say what else may well be coming or when.
But so far, as the researcher instructed PrivacySharks, the leak has also involved again-stop employees’ names, email addresses and positions.
The researcher also identified evidence that Twitch has allegedly been scraping competitors’ products and services for dwell channels and view counts. They shared this display screen capture:

Twitch Allegedly Has Anti-Look at-Botting Tech Up Its Sleeve
Lastly, the researcher also identified screenshots that reveal that Twitch is allegedly ramping up its technology to detect and avoid view-botting on the platform. Look at-botting is when streamers artificially inflate their concurrent-watch depend by working with “illegitimate scripts or applications,” in accordance to Twitch.
Bots aren’t all negative. Fantastic bots help hold climate, sporting activities and other information up to date in serious-time, and they can assistance obtain the very best rate on a solution or track down stolen information. Poor bots, however, can dish out malware and can be employed for hacking, spamming, spying, spreading phony news and compromising websites of all measurements, as Kaspersky has explained.
When it arrives to a services like Twitch, streamers use check out-fraud bots “to improve their streams and get on the digital leaderboard where they hope to draw in legitimate followers and sights,” according to Fraud Blocker. That is comparable to how other platforms operate, by advertising and marketing common channels more than new and unpopular channels.
Twitch is evidently, allegedly working on technology to destroy those people check out-bots. The researcher who was seeking above Twitch’s doxxed knowledge claimed that Twitch uses what PrivacySharks described as “detection tactics involving broadcast statistics to see whether or not streamers are employing perspective-bots.”
In a Thursday web site put up, PrivacySharks shared a screenshot, replicated below, that shared what allegedly appear like Twitch’s botting-fight plans:
“This will compute partnerships-applicable info for just about every broadcast for which edge playlist requests have been produced (in other terms, a broadcast that somebody, somewhere cared about), like fundamental broadcast summary data, no matter if the broadcast was botted, about how several of the views were being real, how concurrents quantities change if we factor out the botted sights, and some info on chat activity. ”
Why Does Look at-Botting Make a difference?
Twitch’s embrace of anti-watch-bot technology should not surprise any individual: In April, Twitch declared that it was cracking down on the bots, foremost several Twitch streamers to hemorrhage followers.
🛡️ We have been checking the rise of faux engagement on Twitch and have recognized 7.5MM+ accounts that break our TOS by observe-botting and perspective-botting. We are getting motion on these accounts and enjoy all of the reports about this issue.
— Twitch Help (@TwitchSupport) April 14, 2021
As PrivacySharks’s Madeleine Hodson described in Thursday’s weblog publish, amassing a substantial subsequent is important to having popular on Twitch, and when she suggests “crucial,” she’s chatting dollar signals.
“Not only does this boost earnings on the platform from subscriptions and donations, but it can consequence in profitable partnerships with 3rd-party businesses,” she wrote. “However, if providers are promotion merchandise with Twitch creators that are streaming to a generally faux audience, a good deal of cash is becoming invested to no avail.”
A Pound of Resource-Code Flesh
But while see-bots subject to streamers and advertisers in the Twitch ecosystem, the resource-code leak is what tends to make cybersecurity pros perk up their ears.
Jon Murchinson, CEO of Blackpoint Cyber, advised Threatpost that from an information security standpoint, “Source code and application growth kits are the crown jewels that you want to shield at all price tag.”
He and others predicted that the leak could end result in adversaries uncovering critical vulnerabilities that could be weaponized for foreseeable future use. “While details are however scarce, this highlights the problem with securing distributed cloud and on-prem infrastructure,” Murchinson commented.
June Werner, cyber-assortment engineer at Infosec Institute, agreed that the resource-code leak “may make it less difficult for destructive actors to find exploits on Twitch’s platform in the long run.”
To reiterate, Twitch hasn’t acknowledged the leak of personal info. But supplied the findings of PrivacySharks’ researcher speak to, and just to continue to be on the safe and sound side, Werner proposed that to safeguard them selves, Twitch end users should empower two-factor authentication (2FA) and ensure that they’re not using their aged Twitch password for any other accounts.
Verify out our cost-free forthcoming dwell and on-demand from customers on line town halls – distinctive, dynamic discussions with cybersecurity specialists and the Threatpost local community.
Some parts of this write-up are sourced from:
threatpost.com


 Swimlane unveils its low-code security automation platform
Swimlane unveils its low-code security automation platform