Misconfigurations in various Android applications leaked delicate facts of a lot more than 100 million people, most likely making them a rewarding focus on for destructive actors.
“By not following most effective-procedures when configuring and integrating third-party cloud-solutions into purposes, millions of users’ private data was uncovered,” Look at Point scientists stated in an assessment printed today and shared with The Hacker News.
“In some circumstances, this sort of misuse only impacts the customers, however, the developers ended up also still left vulnerable. The misconfigurations set users’ private data and developer’s inside sources, such as entry to update mechanisms, storage, and more at risk.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
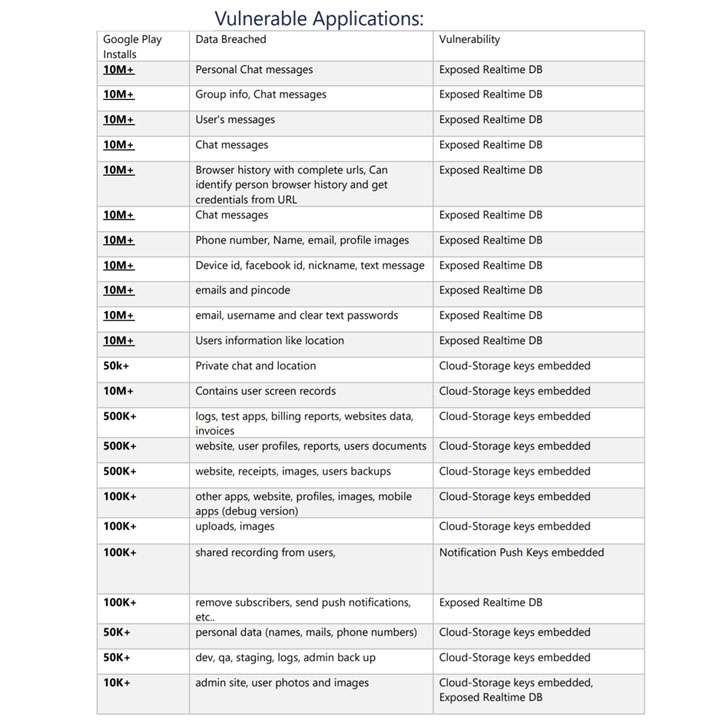
The conclusions occur from a review of 23 Android applications accessible in the formal Google Perform Retailer, some of which have downloads ranging from 10,000 to 10 million, this kind of as Astro Expert, iFax, Logo Maker, Display Recorder, and T’Leva.

In accordance to Verify Place, the issues stem from misconfiguring true-time databases, force notification, and cloud storage keys, ensuing in spillage of email messages, phone quantities, chat messages, locale, passwords, backups, browser histories, and pics.

By not securing the databases powering authentication barriers, the scientists reported they were being able to get facts belonging to consumers of Angolan taxi application T’Leva, like messages exchanged amongst motorists and passengers as perfectly as riders’ comprehensive names, phone figures and desired destination and select-up locations.
What’s additional, the scientists identified that app builders embedded keys necessary for sending press notifications and accessing cloud storage providers straight into the apps. This could not only make it easier for undesirable actors to send a rogue notification to all buyers on behalf of the developer, but could also be exploited even to direct unsuspecting users to a phishing webpage, therefore getting to be an entry level for extra subtle threats.
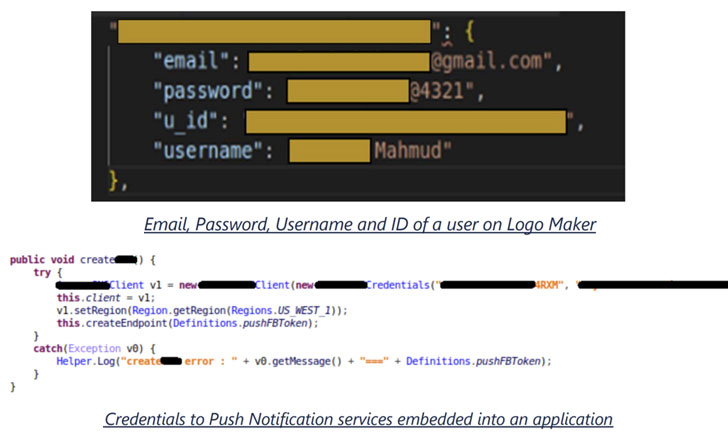
Embedding cloud storage accessibility keys into the applications, likewise, opens the doorway to other attacks whereby an adversary could get hold of all details saved in the cloud — a habits that was noticed in two applications, Display screen Recorder and iFax, therefore giving the scientists the capacity to obtain monitor recordings and faxed paperwork.
Check out Stage notes that only a several of the apps improved their configuration in reaction to liable disclosure, implying buyers of other applications continue on to keep on being susceptible to probable threats like fraud and id theft, not to point out leverage the stolen passwords to obtain obtain to other accounts fraudulently.
“In the long run, victims become susceptible to a lot of different attack vectors, this sort of as impersonations, identify theft, phishing and provider swipes,” mentioned Aviran Hazum, Examine Point’s supervisor of cellular investigation, incorporating the analyze “sheds mild on a disturbing fact exactly where application builders area not only their facts, but their personal users’ knowledge at risk.”
Found this article appealing? Stick to THN on Facebook, Twitter and LinkedIn to read a lot more exclusive articles we publish.
Some sections of this article are sourced from:
thehackernews.com

 Web App Bugs Drove Multiple Breaches Per Firm in 2020
Web App Bugs Drove Multiple Breaches Per Firm in 2020