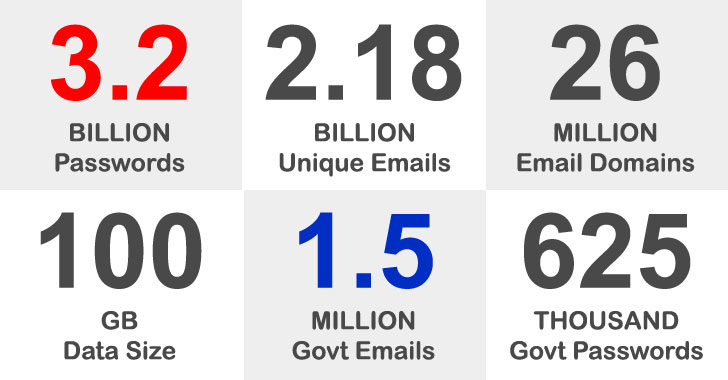
A staggering amount of 3.28 billion passwords linked to 2.18 billion exceptional email addresses were exposed in what is one of the premier info dumps of breached usernames and passwords.
In addition, the leak features 1,502,909 passwords linked with email addresses from governing administration domains across the entire world, with the U.S. authorities by yourself taking up 625,505 of the exposed passwords, followed by the U.K (205,099), Australia (136,025), Brazil (68,535), and Canada (50,726).
The results appear from an evaluation of a huge 100GB knowledge set named “COMB21” — aka Compilation of Quite a few Breaches — that was released for free in an online cybercrime discussion board earlier this February by placing with each other info from a number of leaks in distinctive businesses and corporations that happened about the many years.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

It is truly worth noting that a leak would not suggest a breach of community administration programs. The passwords are explained to have been acquired through tactics these as password hash cracking after currently being stolen or through phishing attacks and eavesdropping on insecure, plaintext connections.
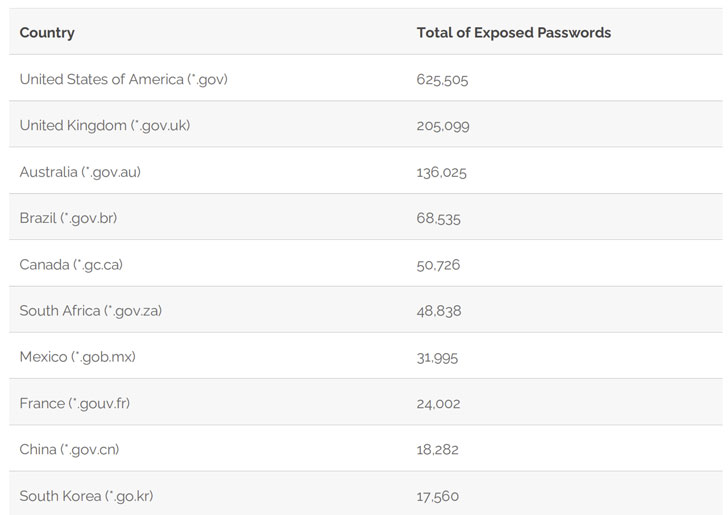
The prime 10 U.S. government domains influenced by the leak are as follows:
- State Office – point out.gov (29,144)
- Veterans Affairs Department – va.gov (28,937)
- Department of Homeland Security – dhs.gov (21,575)
- Countrywide Aeronautics and House Administration – nasa.gov (15,665)
- Inner Profits Company – irs.gov (10,480)
- Middle for Illness Command and Prevention – cdc.gov (8,904)
- Department of Justice – usdoj.gov (8,857)
- Social Security Administration – ssa.gov (8,747)
- U.S. Postal Support – usps.gov (8,205), and
- Environmental Security Agency – epa.gov (7,986)
Apparently, this leak also features 13 qualifications joined to e-mails of the Oldsmar water plant in Florida, as formerly claimed by CyberNews. Nonetheless, you will find no evidence that the breached passwords had been to carry out the cyberattack in February. In distinction, only 18,282 passwords linked to Chinese governing administration domains and 1,964 passwords from these connected to Russia have been laid bare.

“It is an indication that the passwords in these countries, made up of regional alphabets, are less qualified by hackers. It is an unanticipated layer of security in relation to the Roman alphabet,” stated Syhunt Founder and Chief Visionary Officer (CVO) Felipe Daragon.

On a related be aware, a infamous menace actor named ShinyHunters has posted an alleged databases consisting of 20 million BigBasket people for free, just about five months just after the Indian on line grocery delivery startup verified a facts breach. In accordance to Less than the Breach’s Alon Gal, the databases includes users’ email addresses, phone quantities, residential addresses, hashed passwords, dates of beginning, and get histories.
In the past, ShinyHunters has been related to the sale of individual facts from quite a few corporations, which includes Zoosk, SocialShare, Tokopedia, TeeSpring, Mindful, Minted, Chatbooks, Dave, Promo, Mathway, Wattpad, MeetMindful.com, and StarTribune.
Buyers who have experienced their data uncovered are strongly advised to transform their current passwords.
Found this article intriguing? Follow THN on Facebook, Twitter and LinkedIn to go through far more exceptional written content we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com

 Critical RCE Bug Found in Homebrew Package Manager for macOS and Linux
Critical RCE Bug Found in Homebrew Package Manager for macOS and Linux