Cybersecurity researchers on Wednesday disclosed a few extreme security vulnerabilities impacting SolarWinds solutions, the most severe of which could have been exploited to attain remote code execution with elevated privileges.
Two of the flaws (CVE-2021-25274 and CVE-2021-25275) were identified in the SolarWinds Orion Platform, when a 3rd separate weak point (CVE-2021-25276) was found in the company’s Serv-U FTP server for Windows, explained cybersecurity firm Trustwave in technological investigation.
None of the three security issues have been exploited in the unparalleled source chain attack targeting the Orion Platform that came to mild previous December.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The two sets of vulnerabilities in Orion and Serv-U FTP had been disclosed to SolarWinds on December 30, 2020, and January 4, 2021, respectively, subsequent which the organization solved the issues on January 22 and January 25.
It is very proposed that consumers put in the most recent versions of Orion System and Serv-U FTP (15.2.2 Hotfix 1) to mitigate the pitfalls connected with the flaws. Trustwave explained it intends to release a evidence-of-notion (PoC) code following 7 days on February 9.
Total Manage About Orion
Main amongst the vulnerabilities uncovered by Trustwave incorporates inappropriate use of Microsoft Messaging Queue (MSMQ), which is made use of intensely by the SolarWinds Orion Collector Support, thereby permitting unauthenticated people to send out messages to this sort of queues more than TCP port 1801 and ultimately achieve RCE by chaining it with an additional unsafe deserialization issue in the code that handles incoming messages.
“Presented that the message processing code operates as a Windows service configured to use LocalSystem account, we have comprehensive command of the underlying running technique,” Rely on researcher Martin Rakhmanov explained.
The patch unveiled by SolarWinds (Orion System 2020.2.4) addresses the bug with a digital signature validation action that is performed on arrived messages to guarantee that unsigned messages are not processed even further, but Rakhmanov cautioned that the MSMQ is still unauthenticated and will allow anyone to send out messages to it.
The second vulnerability, also found in the Orion Platform, problems the insecure fashion in which qualifications of the backend database (named “SOLARWINDS_ORION”) is stored in a configuration file, resulting in a community, unprivileged consumer choose full command about the database, steal data, or even increase a new admin-amount person to be employed within SolarWinds Orion products.
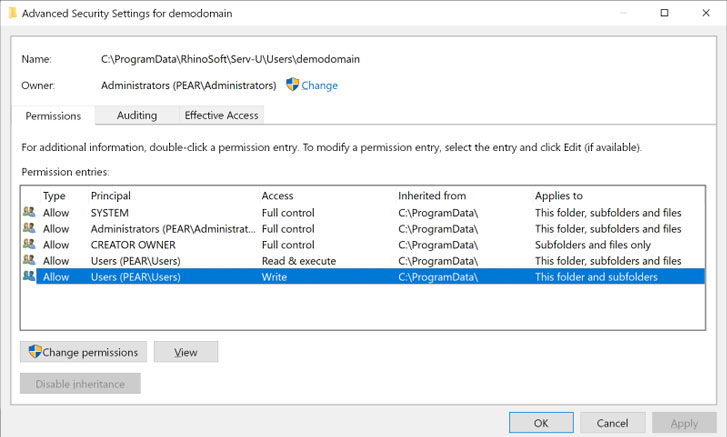
And finally, a flaw in SolarWinds Serv-U FTP Server 15.2.1 for Windows could make it possible for any attacker that can log in to the technique regionally or by way of Remote Desktop to fall a file that defines a new admin person with total entry to the C: push, which can then be leveraged by logging in as that consumer through FTP and go through or change any file on the drive.
U.S. Office of Agriculture Qualified Using New SolarWinds Flaw
Information of the three vulnerabilities in SolarWinds solutions arrives on the heels of experiences that alleged Chinese threat actors exploited a earlier undocumented flaw in the firm’s computer software to split into the Countrywide Finance Heart, a federal payroll agency inside of the U.S. Section of Agriculture.
This flaw is said to be diverse from those people that were abused by suspected Russian danger operatives to compromise SolarWinds Orion software package that was then dispersed to as numerous as 18,000 of its buyers, in accordance to Reuters.
In late December, Microsoft claimed a second hacker collective might have been abusing the IT infrastructure provider’s Orion software package to fall a persistent backdoor called Supernova on concentrate on techniques by taking edge of an authentication bypass vulnerability in the Orion API to execute arbitrary instructions.
SolarWinds issued a patch to handle the vulnerability on December 26, 2020.
Previous week, Brandon Wales, acting director of the U.S. Cybersecurity and Infrastructure Company (CISA), reported almost 30% of the non-public-sector and government agencies joined to the intrusion campaign experienced no direct relationship to SolarWinds, implying that the attackers utilized a variety of techniques to breach goal environments.
The overlap in the twin espionage efforts notwithstanding, the campaigns are yet an additional signal that advanced persistent danger (APT) groups are significantly concentrating on the program supply chain as a conduit to strike higher-worth targets this sort of as organizations and federal government agencies.
The rely on and ubiquity of application these as all those from SolarWinds or Microsoft make them a rewarding concentrate on for attackers, hence underscoring the require for businesses to be on the lookout for likely potential risks stemming from relying on third-party tools to control their platforms and services.
Identified this write-up interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read through a lot more unique written content we put up.
Some elements of this report are sourced from:
thehackernews.com


 Guide: How Security Consolidation Helps Small Cybersecurity Teams
Guide: How Security Consolidation Helps Small Cybersecurity Teams