Here are 3 of the worst breaches, attacker methods and techniques of 2022, and the security controls that can provide effective, business security protection for them.
#1: 2 RaaS Attacks in 13 Months
Ransomware as a company is a sort of attack in which the ransomware software package and infrastructure are leased out to the attackers. These ransomware companies can be ordered on the dark web from other menace actors and ransomware gangs. Popular paying for plans incorporate purchasing the entire resource, applying the current infrastructure while paying out for every an infection, or allowing other attackers accomplish the service while sharing income with them.
In this attack, the risk actor is made up of one of the most commonplace ransomware teams, specializing in obtain by way of 3rd parties, when the targeted enterprise is a medium-sized retailer with dozens of websites in the United States.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The risk actors utilised ransomware as a assistance to breach the victim’s network. They were being in a position to exploit 3rd-party qualifications to gain original accessibility, progress laterally, and ransom the company, all within mere minutes.
The swiftness of this attack was unusual. In most RaaS situations, attackers ordinarily continue to be in the networks for months and months prior to demanding ransom. What is specifically attention-grabbing about this attack is that the business was ransomed in minutes, with no want for discovery or weeks of lateral motion.
A log investigation exposed that the attackers targeted servers that did not exist in this method. As it turns out, the victim was originally breached and ransomed 13 months ahead of this 2nd ransomware attack. Subsequently, the 1st attacker team monetized the first attack not only by the ransom they attained, but also by marketing the firm’s network facts to the next ransomware team.
In the 13 months involving the two attacks, the sufferer changed its network and removed servers, but the new attackers were not conscious of these architectural modifications. The scripts they formulated ended up built for the preceding network map. This also describes how they were being equipped to attack so quickly – they had lots of information about the network. The principal lesson here is that ransomware attacks can be repeated by unique groups, particularly if the victim pays effectively.
“RaaS attacks these types of as this one particular are a superior illustration of how complete visibility allows for early alerting. A world, converged, cloud-native SASE platform that supports all edges, like Cato Networks provides finish network visibility into network functions that are invisible to other providers or may possibly go beneath the radar as benign gatherings. And, staying ready to totally contextualize the events enables for early detection and remediation.
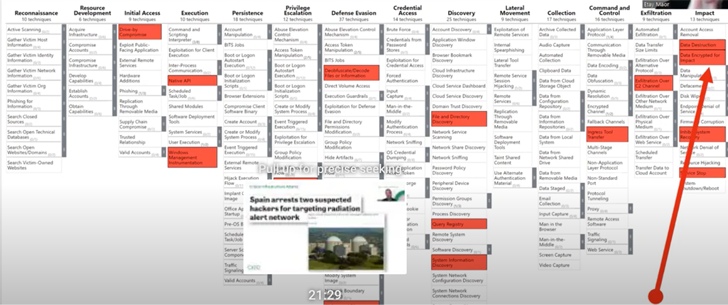
#2: The Critical Infrastructure Attack on Radiation Inform Networks
Attacks on critical infrastructure are getting to be far more frequent and extra hazardous. Breaches of h2o supply crops, sewage programs and other this sort of infrastructures could set millions of inhabitants at risk of a human crisis. These infrastructures are also becoming additional vulnerable, and attack floor management tools for OSINT like Shodan and Censys let security groups to obtain these kinds of vulnerabilities with relieve.
In 2021, two hackers have been suspected of concentrating on radiation alert networks. Their attack relied on two insiders that labored for a 3rd party. These insiders disabled the radiation notify programs, drastically debilitating their potential to monitor radiation attacks. The attackers had been then in a position to delete critical computer software and disable radiation gauges (which is section of the infrastructure itself).

“Sad to say, scanning for vulnerable methods in critical infrastructure is easier than ever. Though a lot of these types of organizations have many layers of security, they are continue to making use of level alternatives to attempt and protect their infrastructure rather than a person technique that can look holistically at the entire attack lifecycle. Breaches are never ever just a phishing problem, or a qualifications challenge, or a vulnerable process challenge – they are constantly a combination of various compromises done by the risk actor,” mentioned Etay Maor, Sr. Director of Security System at Cato Networks.
#3: The Three-Step Ransomware Attack That Begun with Phishing
The 3rd attack is also a ransomware attack. This time, it consisted of a few ways:
1. Infiltration – The attacker was able to acquire entry to the network by way of a phishing attack. The victim clicked on a hyperlink that generated a relationship to an exterior website, which resulted in the download of the payload.
2. Network exercise – In the next section, the attacker progressed laterally in the network for two months. All through this time, it gathered admin passwords and utilised in-memory fileless malware. Then on New Year’s Eve, it executed the encryption. This date was picked considering the fact that it was (rightfully) assumed the security staff would be off on vacation.
3. Exfiltration – At last, the attackers uploaded the facts out of the network.
In addition to these three primary measures, supplemental sub-procedures have been utilized through the attack and the victim’s issue security methods were not ready to block this attack.
“A a number of choke position strategy, a person that looks horizontally (so to converse) at the attack somewhat than as a established of vertical, disjointed issues, is the way to greatly enhance detection, mitigation and avoidance of these threats. Opposed to preferred perception, the attacker requirements to be proper many situations and the defenders only need to have to be proper just as soon as. The fundamental systems to put into practice a multiple choke position strategy are full network visibility by way of a cloud-native spine, and a one go security stack that is primarily based on ZTNA.” stated Etay Maor, Sr. Director of Security Approach at Cato Networks.
How Do Security Stage Alternatives Stack Up?
It is common for security gurus to succumb to the “single level of failure fallacy”. Having said that, cyber-attacks are complex occasions that hardly ever entail just just one tactic or approach which is the bring about of the breach. For that reason, an all-encompassing outlook is essential to productively mitigate cyber-attacks. Security level remedies are a resolution for solitary details of failure. These applications can establish dangers, but they will not connect the dots, which could and has led to a breach.
Here is View Out for in the Coming Months
According to ongoing security study done by Cato Networks Security Staff, they have recognized two more vulnerabilities and exploit attempts that they suggest which includes in your impending security plans:
1. Log4j
Although Log4j made its debut as early as December of 2021, the sound its earning hasn’t died down. Log4j is however remaining utilised by attackers to exploit systems, as not all companies have been able to patch their Log4j vulnerabilities or detect Log4j attacks, in what is recognised as “digital patching”. They recommend prioritizing Log4j mitigation.
2. Misconfigured Firewalls and VPNs
Security alternatives like firewalls and VPNs have become accessibility details for attackers. Patching them has come to be more and more complicated, in particular in the period of architecture cloudification and remote operate. It is proposed to pay out shut awareness to these elements as they are ever more vulnerable.
How to Minimize Your Attack Surface area and Acquire Visibility into the Network
To lessen the attack surface, security professionals need to have visibility into their networks. Visibility depends on three pillars:
- Actionable details – that can be employed to mitigate attacks
- Reputable info – that minimizes the range of wrong positives
- Timely details – to assure mitigation takes place in advance of the attack has an influence
At the time an corporation has entire visibility to the activity on their network they can contextualize the knowledge, choose whether the activity witnessed need to be allowed, denied, monitored, restricted (or any other action) and then have the ability to enforce this choice. All these elements must be utilized to every single entity, be it a consumer, product, cloud application etc. All the time everywhere. That is what SASE is all about.
Uncovered this report exciting? Stick to us on Twitter and LinkedIn to browse far more exclusive articles we write-up.
Some parts of this post are sourced from:
thehackernews.com


 Fifth of ICS Bugs Have No Patch Available
Fifth of ICS Bugs Have No Patch Available