4 diverse Android banking trojans ended up spread by using the official Google Perform Shop involving August and November 2021, ensuing in additional than 300,000 bacterial infections by different dropper apps that posed as seemingly harmless utility applications to acquire entire regulate of the infected devices.
Intended to produce Anatsa (aka TeaBot), Alien, ERMAC, and Hydra, cybersecurity company ThreatFabric reported the malware campaigns are not only more refined, but also engineered to have a little malicious footprint, effectively making certain that the payloads are put in only on smartphones equipment from specific areas and blocking the malware from being downloaded through the publishing process.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The checklist of destructive dropper apps is beneath –
- Two Factor Authenticator (com.flowdivison)
- Safety Guard (com.protectionguard.application)
- QR CreatorScanner (com.ready.qrscanner.mix)
- Grasp Scanner Dwell (com.multifuction.merge.qr)
- QR Scanner 2021 (com.qr.code.deliver)
- QR Scanner (com.qr.barqr.scangen)
- PDF Document (com.xaviermuches.docscannerpro2)
- Scanner – Scan to PDF
- PDF Document Scanner (com.docscanverifier.mobile)
- PDF Doc Scanner Cost-free (com.doscanner.cellular)
- CryptoTracker (cryptolistapp.app.com.cryptotracker)
- Health and fitness center and Physical fitness Trainer (com.gym.coach.jeux)
Although Google earlier this month instituted restrictions to restrict the use of accessibility permissions that enable destructive applications to seize delicate information from Android devices, operators of these applications are increasingly refining their ways by other signifies even when compelled to pick the much more standard way of putting in applications through the application market.
Chief among the tactics is a approach referred to as versioning, whereby thoroughly clean versions of the applications are initial uploaded, and malicious functionalities are incrementally introduced in the sort of subsequent application updates. An additional tactic will involve developing glance-alike command-and-manage (C2) websites that match the theme of the dropper app so as to slip earlier standard detection methods.
ThreatFabric found out six Anatsa droppers on the Engage in Retail store given that June 2021, with the apps programmed to download an “update” adopted by prompting people to grant it permissions to set up apps and Accessibility Service privileges.

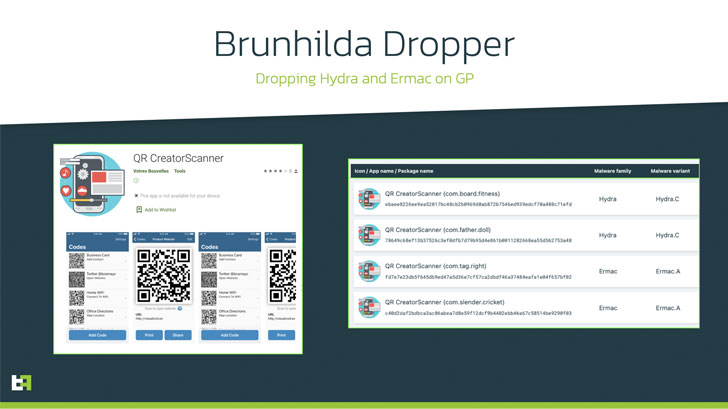
Brunhilda, a risk actor which was found distributing a distant entry trojan named Vultur in July 2021, leveraged trojanized applications masquerading as QR code creator apps to fall Hydra and ERMAC malware aimed at customers in the U.S., a marketplace previously not qualified by the two malware households.
Finally, a health and fitness education dropper application with around 10,000 installations — dubbed GymDrop — was uncovered delivering the Alien banking trojan payload by masking it as a “new package deal of work out exercise routines,” even as its purportedly legitimate developer web page doubles up as the C2 server to fetch the configuration expected to down load the malware.
“To make themselves even far more difficult to detect, the actors powering these dropper applications only manually activate the installation of the banking trojan on an infected product in scenario they drive a lot more victims in a distinct location of the planet,” the researchers stated. “This would make automatic detection a a lot more durable approach to undertake by any business.”
Uncovered this article attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to read through extra distinctive articles we put up.
Some sections of this article are sourced from:
thehackernews.com



 New Chinotto Spyware Targets North Korean Defectors, Human Rights Activists
New Chinotto Spyware Targets North Korean Defectors, Human Rights Activists