Cybersecurity researchers have found out a new malware dropper contained in as numerous as 9 Android applications distributed through Google Engage in Retailer that deploys a next stage malware able of gaining intrusive access to the economic accounts of victims as very well as whole regulate of their gadgets.
“This dropper, dubbed Clast82, utilizes a series of approaches to keep away from detection by Google Enjoy Guard detection, completes the analysis time period productively, and improvements the payload dropped from a non-malicious payload to the AlienBot Banker and MRAT,” Check out Position researchers Aviran Hazum, Bohdan Melnykov, and Israel Wernik reported in a create-up revealed right now.
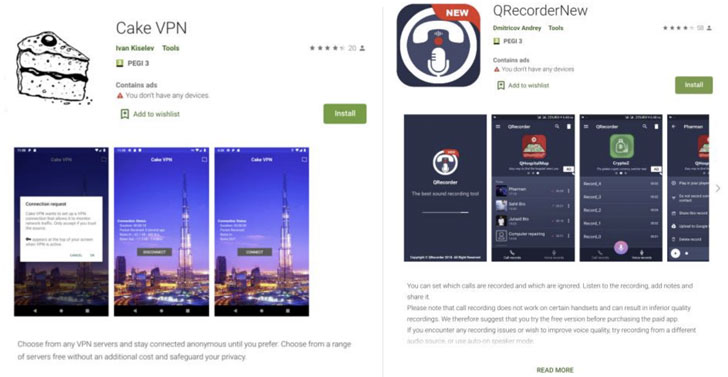
The applications that were utilised for the marketing campaign include things like Cake VPN, Pacific VPN, eVPN, BeatPlayer, QR/Barcode Scanner MAX, New music Participant, tooltipnatorlibrary, and QRecorder. Immediately after the results ended up described to Google on January 28, the rogue apps were being eradicated from the Engage in Retail store on February 9.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Malware authors have resorted to a variety of solutions to bypass app store vetting mechanisms. No matter whether be it utilizing encryption to conceal strings from investigation engines, making rogue versions of legitimate applications, or crafting bogus opinions to entice end users into downloading the apps, fraudsters have hit back again at Google’s attempts to secure the platform by regularly developing new methods to slip by the net.
Equally well-known are other solutions like versioning, which refers to uploading a clear version of the app to the Play Retail outlet to establish have confidence in between users and then sneakily incorporating undesirable code at a afterwards phase by way of app updates, and incorporating time-dependent delays to bring about the malicious features in an attempt to evade detection by Google.
Clast82 is no various in that it utilizes Firebase as a platform for command-and-regulate (C2) communication and helps make use of GitHub to down load the malicious payloads, in addition to leveraging legit and acknowledged open up-source Android apps to insert the Dropper performance.
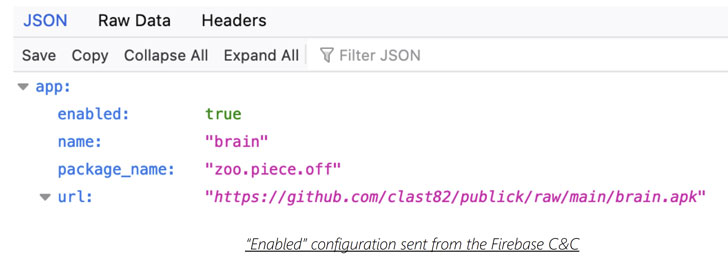
“For each software, the actor established a new developer consumer for the Google Enjoy store, together with a repository on the actor’s GitHub account, so enabling the actor to distribute unique payloads to units that ended up contaminated by every destructive software,” the scientists observed.
For occasion, the malicious Cake VPN application was observed to be primarily based on an open-sourced variation of its namesake made by a Dhaka-based mostly developer by the title of Syed Ashraf Ullah. But once the application is released, it takes gain of the Firebase real-time database to retrieve the payload path from GitHub, which is then put in on the target device.
In the function the alternative to set up applications from mysterious resources has been turned off, Clast82 frequently urges the consumer each five seconds with a bogus “Google Play Companies” prompt to help the authorization, in the long run employing it to put in AlienBot, an Android banking MaaS (malware-as-a-company) able of stealing credentials and two-factor authentication codes from money applications.

Final month, a common barcode scanner app with about 10 million installations turned rogue with a solitary update soon after its possession changed hands. In a similar development, a Chrome extension by the name of The Terrific Suspender was deactivated following studies that the insert-on stealthily included attributes that could be exploited to execute arbitrary code from a remote server.
“The hacker behind Clast82 was capable to bypass Google Play’s protections applying a resourceful, but about, methodology,” Hazum stated. “With a very simple manipulation of conveniently out there 3rd party sources — like a GitHub account, or a FireBase account — the hacker was in a position to leverage readily accessible sources to bypass Google Play Store’s protections. The victims considered they have been downloading an innocuous utility application from the official Android marketplace, but what they had been really finding was a risky trojan coming straight for their financial accounts.”
Uncovered this article exciting? Adhere to THN on Fb, Twitter and LinkedIn to go through extra distinctive content material we publish.
Some sections of this write-up are sourced from:
thehackernews.com


 Intel joins forces with DARPA to help build encryption ‘holy grail’
Intel joins forces with DARPA to help build encryption ‘holy grail’