Google has patched a bug in its feedback tool integrated across its providers that could be exploited by an attacker to possibly steal screenshots of delicate Google Docs paperwork basically by embedding them in a destructive web-site.
The flaw was found on July 9 by security researcher Sreeram KL, for which he was awarded $3133.70 as component of Google’s Vulnerability Reward Software.
Several of Google’s solutions, like Google Docs, arrive with a “Send suggestions” or “Enable Docs boost” choice that makes it possible for customers to send out comments alongside with an solution to include a screenshot — some thing which is quickly loaded to spotlight specific issues.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
But rather of having to duplicate the identical operation throughout its products and services, the feedback feature is deployed in Google’s main website (“www.google.com”) and integrated to other domains by using an iframe ingredient that loads the pop-up’s content material from “suggestions.googleusercontent.com.”
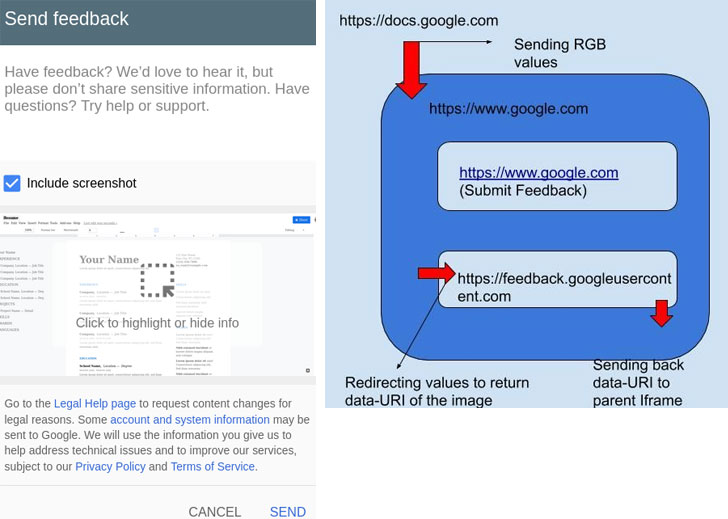
This also usually means that every time a screenshot of the Google Docs window is included, rendering the image necessitates the transmission of RGB values of each and every pixel to the parent domain (www.google.com), which then redirects all those RGB values to the feedback’s area, which in the long run constructs the image and sends it back in Base64 encoded structure.
Sreeram, on the other hand, discovered a bug in the method these messages have been passed to “feedback.googleusercontent.com,” as a result enabling an attacker to modify the frame to an arbitrary, external internet site, and in convert, steal and hijack Google Docs screenshots which were intended to be uploaded to Google’s servers.
Notably, the flaw stems from a deficiency of X-Frame-Possibilities header in the Google Docs domain, which designed it probable to modify the goal origin of the message and exploit the cross-origin conversation amongst the webpage and the body contained in it.
Whilst the attack needs some form of user conversation — i.e. clicking the “Send out responses” button — an exploit could very easily leverage this weakness to capture the URL of the uploaded screenshot and exfiltrate it to a destructive internet site.
This can be achieved by embedding a Google Docs file in an iFrame on a rogue website and hijacking the feedback pop-up body to redirect the contents to a area of the attacker’s preference.
Failing to offer a concentrate on origin through cross-origin communication raises security worries in that it discloses the details that is sent to any web page.
“Generally specify an actual goal origin, not *, when you use postMessage to ship data to other windows,” Mozilla documentation states. “A destructive web-site can modify the locale of the window with out your information, and consequently it can intercept the details sent applying postMessage.”
Located this post intriguing? Observe THN on Fb, Twitter and LinkedIn to browse a lot more special material we publish.
Some parts of this report are sourced from:
thehackernews.com


 AutoHotkey-Based Password Stealer Targeting US, Canadian Banking Users
AutoHotkey-Based Password Stealer Targeting US, Canadian Banking Users