An unpatched security weak spot in Google Drive could be exploited by malware attackers to distribute malicious information disguised as genuine documents or illustrations or photos, enabling undesirable actors to carry out spear-phishing attacks comparatively with a large achievement fee.
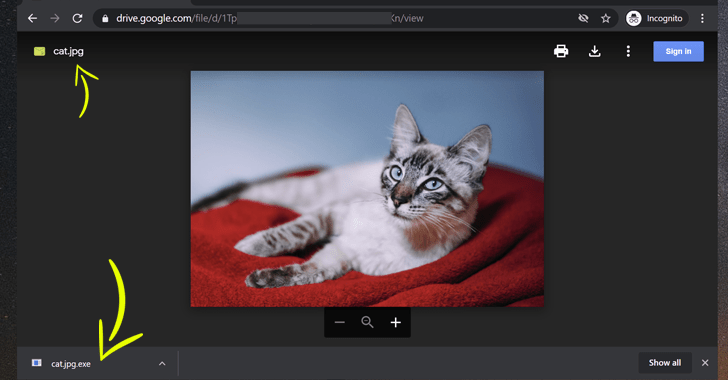
The most recent security issue—of which Google is conscious but, unfortunately, still left unpatched—resides in the “regulate variations” features supplied by Google Push that makes it possible for buyers to upload and handle different variations of a file, as nicely as in the way its interface supplies a new variation of the documents to the customers.
Logically, the regulate versions functionally should really make it possible for Google Drive users to update an older edition of a file with a new variation possessing the similar file extension, but it turns out that it truly is not the scenario.
According to A. Nikoci, a system administrator by profession who documented the flaw to Google and later disclosed it to The Hacker Information, the impacted functionally will allow people to upload a new version with any file extension for any present file on the cloud storage, even with a malicious executable.
As shown in the demo videos—which Nikoci shared solely with The Hacker News—in carrying out so, a authentic version of the file which is previously been shared amid a group of buyers can be replaced by a destructive file, which when previewed on-line does not show newly built modifications or increase any alarm, but when downloaded can be employed to infect targeted units.
“Google lets you transform the file model without examining if it’s the identical form,” Nikoci mentioned. “They did not even drive the similar extension.”
Unnecessary to say, the issue leaves the door open up for really productive spear-phishing campaigns that get gain of the prevalent prevalence of cloud services this sort of as Google Drive to distribute malware.
The advancement arrives as Google recently preset a security flaw in Gmail that could have authorized a risk actor to ship spoofed e-mails mimicking any Gmail or G Suite buyer, even when demanding DMARC/SPF security guidelines are enabled.
Malware Hackers Love Google Generate
Spear-phishing frauds commonly attempt to trick recipients into opening malicious attachments or clicking seemingly innocuous one-way links, thus supplying private data, like account credentials, to the attacker in the course of action.
The hyperlinks and attachments can also be employed to get the receiver to unknowingly download malware that can give the attacker accessibility to the user’s personal computer program and other delicate information and facts.
This new security issue is no distinctive. Google Drive’s file update feature is intended to be an simple way to update shared files, which includes the capacity to exchange the doc with a totally new edition from the system. This way, the shared file can be up-to-date without having altering its hyperlink.
However, without any validation for file extensions, this can have likely severe penalties when customers of the shared file, who, upon notification of the transform by way of an email, conclusion up downloading the document and unwittingly infecting their programs with malware.
Such a state of affairs could be leveraged to mount whaling attacks, a phishing tactic frequently applied by cyber-legal gangs to masquerade as senior administration personnel in an corporation and concentrate on unique persons, hoping to steal sensitive data or gain entry to their pc methods for prison applications.
Even worse, Google Chrome appears to implicitly rely on the information downloaded from Google Push even when they are detected by other antivirus computer software as malicious.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Cloud Solutions Turn into An Attack Vector
Although there’s no proof that this flaw has been exploited in the wild, it wouldn’t be complicated for attackers to repurpose it for their reward provided how cloud services have been a motor vehicle for malware delivery in a number of spear-phishing attacks in latest months.
Previously this year, Zscaler identified a phishing marketing campaign that employed Google Generate to down load a password stealer publish first compromise.
Very last thirty day period, Check Issue Study and Cofense highlighted a series of new strategies whereby risk actors were discovered not only employing spam emails to embed malware hosted on services like Dropbox and Google Generate but also exploiting cloud storage products and services to host phishing webpages.
ESET, in an assessment of the Evilnum APT team, observed a similar craze in which fintech companies in Europe and the British isles have been specific with spear-phishing email messages that comprise a link to a ZIP file hosted on Google Travel to steal computer software licenses, shopper credit history card data, and investments and buying and selling files.
Similarly, Fortinet, in a marketing campaign noticed previously this thirty day period, uncovered proof of a COVID-19-themed phishing entice that purportedly warned users of delayed payments because of to the pandemic, only to obtain the NetWire remote obtain Trojan hosted on a Google Travel URL.
With scammers and criminals pulling out all the stops to conceal their destructive intentions, it is essential that users continue to keep a near eye on suspicious e-mail, which includes Google Generate notifications, to mitigate any possible risk.
Uncovered this article intriguing? Follow THN on Facebook, Twitter and LinkedIn to read through much more distinctive content material we put up.

 Carnival ought to appropriate the ship immediately after breaches threaten travelers’ have confidence in
Carnival ought to appropriate the ship immediately after breaches threaten travelers’ have confidence in