A new advanced persistent menace (APT) has been powering a string of attacks against motels across the environment, alongside with governments, worldwide companies, engineering organizations, and legislation companies.
Slovak cybersecurity company ESET codenamed the cyber espionage team FamousSparrow, which it mentioned has been active given that at the very least August 2019, with victims located across Africa, Asia, Europe, the Middle East, and the Americas, spanning numerous international locations this kind of as Burkina Faso, Taiwan, France, Lithuania, the U.K., Israel, Saudi Arabia, Brazil, Canada, and Guatemala.
Attacks mounted by the team entail exploiting regarded vulnerabilities in server apps these as SharePoint and Oracle Opera, in addition to the ProxyLogon remote code execution vulnerability in Microsoft Exchange Server that came to light-weight in March 2021, making it the latest danger actor to have experienced accessibility to the exploit before details of the flaw became general public.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
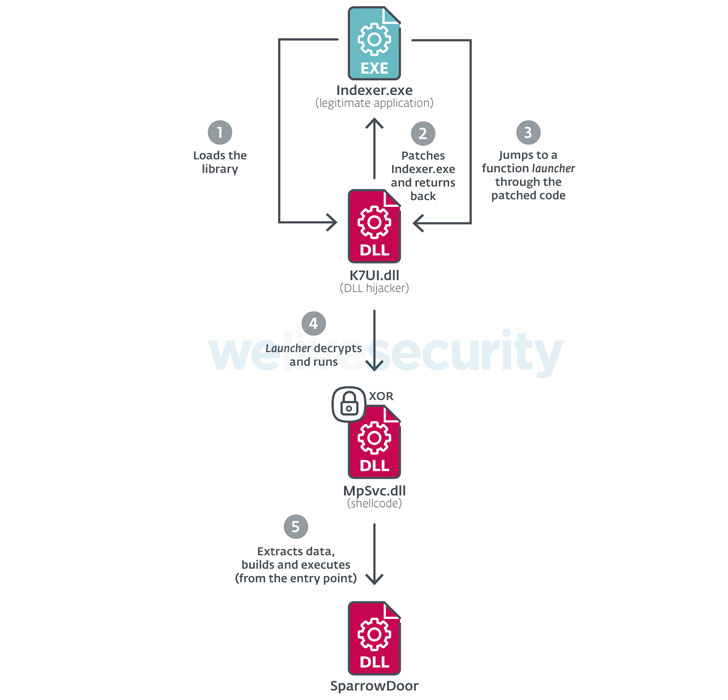
According to ESET, intrusion exploiting the flaws commenced on March 3, ensuing in the deployment of a number of malicious artifacts, which include two bespoke variations of Mimikatz credential stealer, a NetBIOS scanner named Nbtscan, and a loader for a tailor made implant dubbed SparrowDoor.
Installed by leveraging a strategy called DLL research purchase hijacking, SparrowDoor functions as a utility to burrow into new corners of the target’s internal network that hackers also gained access to execute arbitrary commands as well as amass and exfiltrate sensitive information and facts to a distant command-and-management (C2) server less than their management.

When ESET didn’t attribute the FamousSparrow team to a specific country, it did locate similarities in between its methods and individuals of SparklingGoblin, an offshoot of the China-linked Winnti Group, and DRBControl, which also overlaps with malware earlier determined with Winnti and Emissary Panda campaigns.
“This is yet another reminder that it is critical to patch internet-dealing with apps rapidly, or, if speedy patching is not possible, to not expose them to the internet at all,” ESET researchers Tahseen Bin Taj and Matthieu Faou mentioned.
Observed this report exciting? Follow THN on Fb, Twitter and LinkedIn to read a lot more exceptional content material we write-up.
Some pieces of this posting are sourced from:
thehackernews.com

 Exchange/Outlook Autodiscover Bug Spills $100K+ Email Passwords
Exchange/Outlook Autodiscover Bug Spills $100K+ Email Passwords