As ransomware attacks against critical infrastructure keep on to spike in modern months, cybersecurity scientists have uncovered a new entrant that has been actively seeking to carry out multistage attacks on substantial company networks of medical labs, financial institutions, brands, and software package builders in Russia.
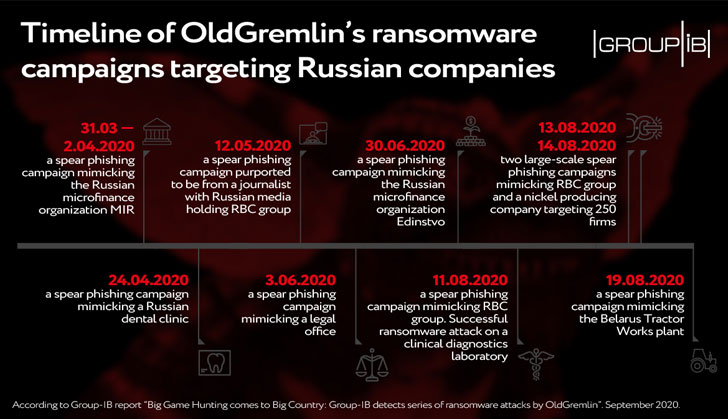
The ransomware gang, codenamed “OldGremlin” and believed to be a Russian-talking risk actor, has been joined to a sequence of strategies at least because March, including a thriving attack against a medical diagnostics laboratory that happened very last month on August 11.
“The team has focused only Russian companies so far, which was standard for numerous Russian-speaking adversaries, these kinds of as Silence and Cobalt, at the commencing of their prison route,” Singaporean cybersecurity business Group-IB explained in a report posted right now and shared with The Hacker News.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Making use of Russia as a screening floor, these groups then switched to other geographies to distance on their own from vicious actions of the target country’s law enforcement and lower the likelihood of ending at the rear of the bars.”
OldGremlin’s modus operandi includes making use of personalized backdoors — these types of as TinyNode and TinyPosh to obtain additional payloads — with the greatest goal of encrypting data files in the infected program employing TinyCryptor ransomware (aka decr1pt) and keeping it hostage for about $50,000.
In addition, the operators obtained an first foothold on the network working with a phishing email sent on behalf of Russia’s RBC Group, a Moscow-based important media team, with “Bill” in the subject matter line.
The message knowledgeable the receiver of their incapacity to make contact with the victim’s colleague with regards to an urgent bill payment alongside with a destructive backlink to fork out the invoice that, when clicked, downloaded the TinyNode malware.
On finding their way in, the terrible actor employed remote accessibility to the infected laptop or computer, leveraging it to laterally move across the network by means of Cobalt Strike and assemble authentication data of the area administrator.
In a different variant of the attack observed in March and April, the cybercriminals were being discovered using COVID-themed phishing lures to fiscal enterprises that masqueraded as a Russian microfinance business to produce the TinyPosh Trojan.
Subsequently, a different wave of the marketing campaign was detected on August 19, when the cybercriminals sent out spear-phishing messages exploiting the ongoing protests in Belarus decrying the federal government, proving after once again that danger actors are adept at capitalizing environment functions to their edge.
In all, OldGremlin has been behind 9 campaigns between Could and August, according to Group-IB.
“What distinguishes OldGremlin from other Russian-talking danger actors is their fearlessness to function in Russia,” Oleg Skulkin, a senior digital forensics analyst at Group-IB, said.
“This indicates that the attackers are either fine-tuning their techniques benefiting from house gain ahead of likely worldwide, as it was the circumstance with Silence and Cobalt, or they are representatives of some of Russia’s neighbors who have a strong command of Russian.”
Discovered this posting attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read far more exceptional content we write-up.
Some parts of this article is sourced from:
thehackernews.com


 Lessons from the ransomware death: Prioritize cyber emergency preparedness
Lessons from the ransomware death: Prioritize cyber emergency preparedness