Cybersecurity researchers have charted the evolution of Jupyter, a .NET infostealer known for singling out healthcare and training sectors, which make it exceptional at defeating most endpoint security scanning solutions.
The new shipping chain, noticed by Morphisec on September 8, underscores that the malware has not just ongoing to keep on being lively but also showcases “how menace actors carry on to develop their attacks to become far more efficient and evasive.” The Israeli enterprise claimed it truly is at this time investigating the scale and scope of the attacks.
To start with documented in November 2020, Jupyter (aka Solarmarker) is most likely Russian in origin and principally targets Chromium, Firefox, and Chrome browser facts, with more abilities that make it possible for for total backdoor performance, such as options to siphon facts and upload the specifics to a distant server and obtain and execute even more payloads. Forensic proof gathered by Morphisec shows that various versions of Jupyter began emerging setting up May well 2020.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In August 2021, Cisco Talos attributed the intrusions to a “quite refined actor mostly targeted on credential and residual facts theft.” Cybersecurity firm CrowdStrike, previously this February, explained the malware as packing a multi-stage, greatly obfuscated PowerShell loader, which qualified prospects to the execution of a .NET compiled backdoor.

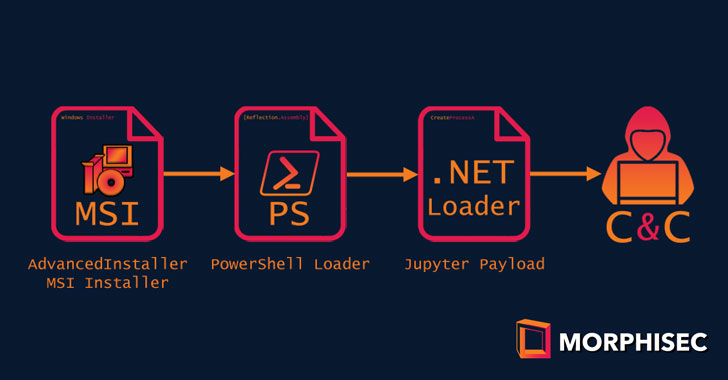
Although former attacks incorporated authentic binaries of perfectly-acknowledged program this kind of as Docx2Rtf and Expert PDF, the newest supply chain places to use an additional PDF application referred to as Nitro Pro. The attacks start out with a deployment of an MSI installer payload that is around 100MB in dimension, permitting them to bypass anti-malware engines, and obfuscated utilizing a third-party application packaging wizard identified as Sophisticated Installer.
Working the MSI payload sales opportunities to the execution of a PowerShell loader embedded in just a genuine binary of Nitro Pro 13, two variants of which have been observed signed with a legitimate certificate belonging to an real company in Poland, suggesting a possible certificate impersonation or theft. The loader, in the ultimate-phase, decodes and runs the in-memory Jupyter .NET module.
“The evolution of the Jupyter infostealer/backdoor from when we first identified it in 2020 proves the real truth of the assertion that threat actors are normally innovating,” Morphisec researcher Nadav Lorber explained. “That this attack proceeds to have low or no detections on VirusTotal even further signifies the facility with which threat actors evade detection-centered options.”
Observed this short article intriguing? Abide by THN on Fb, Twitter and LinkedIn to read more exceptional material we article.
Some areas of this report are sourced from:
thehackernews.com

 Urgent Chrome Update Released to Patch Actively Exploited Zero-Day Vulnerability
Urgent Chrome Update Released to Patch Actively Exploited Zero-Day Vulnerability