A cyber attack that derailed internet websites of Iran’s transport ministry and its national railway procedure previously this thirty day period, producing common disruptions in prepare companies, was the consequence of a hardly ever-right before-found reusable wiper malware referred to as “Meteor.”
The marketing campaign — dubbed “MeteorExpress” — has not been connected to any previously determined danger group or to further attacks, building it the first incident involving the deployment of this malware, in accordance to scientists from Iranian antivirus business Amn Pardaz and SentinelOne. Meteor is thought to have been in the functions more than the earlier a few many years.
“Irrespective of a absence of specific indicators of compromise, we were capable to get better most of the attack elements,” SentinelOne’s Principal Threat Researcher, Juan Andres Guerrero-Saade, observed. “Guiding this outlandish tale of stopped trains and glib trolls, we found the fingerprints of an unfamiliar attacker,” incorporating the offensive is “designed to cripple the victim’s units, leaving no recourse to basic remediation by using domain administration or restoration of shadow copies.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

On July 9, the Iranian train technique was left paralyzed in the wake of a significant attack, with the hackers defacing electronic displays to instruct passengers to direct their complaints to the phone range of the Iranian Supreme Chief Ayatollah Ali Khamenei’s office. The incident is claimed to have reportedly brought on “unparalleled chaos” at stations with hundreds of trains delayed or canceled.
Now in accordance to SentinelOne, the an infection chain commenced with the abuse of Group Plan to deploy a toolkit that consisted of a mixture of batch information orchestrating distinctive elements, which are extracted from multiple RAR archives and are chained jointly to aid the encryption of the filesystem, corruption of the master boot report (MBR), and locking of the program in problem.
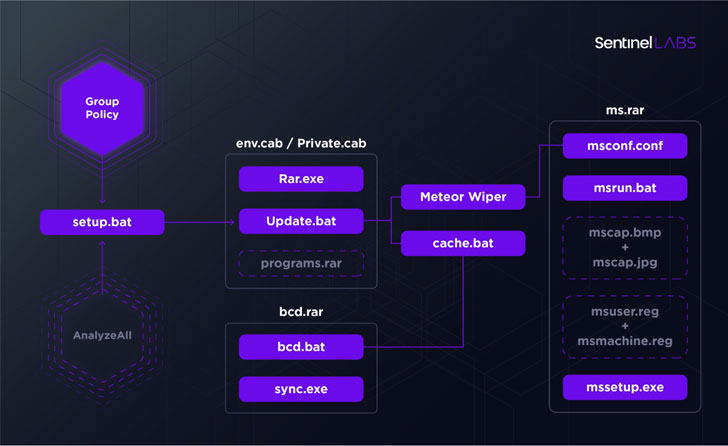
Other batch script files dropped throughout the attack were observed to consider cost of disconnecting the contaminated machine from the network and building Windows Defender exclusions for all of the factors, a tactic that’s turning out to be increasingly common amid risk actors to cover their destructive actions from antimalware solutions put in on the device.

Meteor, for its element, is an externally configurable wiper with an extensive set of features, together with the capability to delete shadow copies as well as a “prosperity of further performance” these kinds of as changing consumer passwords, terminating arbitrary processes, disabling recovery mode, and executing destructive instructions.
The wiper has been characterised as “a weird amalgam of tailor made code” that blends open up-resource components with historical software program that is “rife with sanity checks, error checking, and redundancy in accomplishing its goals,” suggesting a fragmented tactic and a deficiency of coordination throughout diverse teams associated in the progress.
“Conflict in cyberspace is overpopulated with progressively brazen danger actors. Behind the artistry of this epic troll lies an awkward truth where by a formerly unknown threat actor is willing to leverage wiper malware against community railways methods,” Guerrero-Saade stated. “The attacker is an intermediate level participant whose distinct operational components sharply oscillate from clunky and rudimentary to slick and well-made.”
“We should hold in mind that the attackers had been previously familiar with the basic set up of their target, attributes of the area controller, and the target’s choice of backup procedure (Veeam). That indicates a reconnaissance stage that flew solely less than the radar and a prosperity of espionage tooling that we’ve nonetheless to uncover.”
Observed this report interesting? Comply with THN on Fb, Twitter and LinkedIn to study a lot more exceptional written content we put up.
Some pieces of this short article are sourced from:
thehackernews.com


 Phony Call Centers Tricking Users Into Installing Ransomware and Data-Stealers
Phony Call Centers Tricking Users Into Installing Ransomware and Data-Stealers