Cybersecurity scientists on Monday disclosed a new malspam campaign distributing a fresh new variant of a malware loader termed ‘Buer’ penned in Rust, illustrating how adversaries are frequently honing their malware toolsets to evade examination.
Dubbed “RustyBuer,” the malware is dispersed by means of email messages masquerading as shipping and delivery notices from DHL Assist, and is stated to have afflicted no fewer than 200 businesses across far more than 50 verticals due to the fact early April.
“The new Buer variant is penned in Rust, an economical and easy-to-use programming language that is becoming increasingly well known,” Proofpoint researchers said in a report shared with The Hacker Information. “Rewriting the malware in Rust permits the threat actor to greater evade existing Buer detection abilities.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Initially introduced in August of 2019, Buer is a modular malware-as-a-services supplying that is sold on underground discussion boards and made use of as a very first-stage downloader to deliver extra payloads, delivering preliminary compromise of targets’ Windows methods and allowing the attacker to set up a “digital beachhead” for further malicious activity. A Proofpoint analysis in December 2019 characterised Buer as a malware coded totally in C, using a regulate panel created in .NET Main.
In September 2020, the operators at the rear of the Ryuk ransomware were found applying the Buer malware dropper as an preliminary accessibility vector as component of a spam marketing campaign. Then a phishing attack uncovered in February 2021 utilized invoice-themed lures to entice users into opening Microsoft Excel paperwork that incorporate malicious macros, which obtain and execute the Buer dropper on the infected procedure.
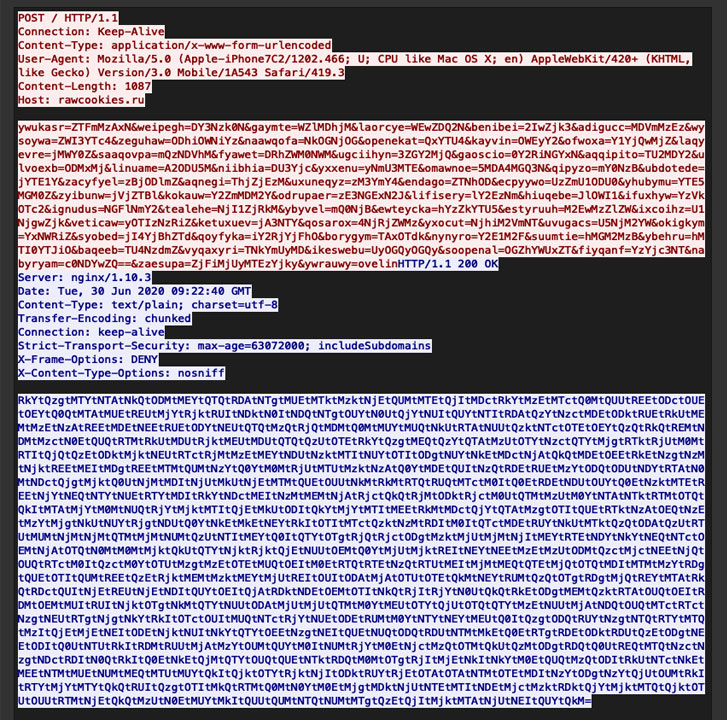 Buer Loader original Put up request
Buer Loader original Put up request
The new maldoc marketing campaign that sent the Buer malware loader follows a very similar modus operandi, utilizing DHL-themed phishing e-mails to distribute weaponized Term or Excel documents that drop the Rust variant of Buer loader. The “abnormal” departure from the C programming language signifies Buer is now able of circumventing detections that are based mostly on functions of the malware penned in C.
“The rewritten malware, and the use of more recent lures trying to show up a lot more legitimate, suggest risk actors leveraging RustyBuer are evolving techniques in many ways to both of those evade detection and try to enhance productive click fees,” the researchers said.
Supplied the point that Buer acts as a 1st-stage loader for other varieties of malware, like Cobalt Strike and ransomware strains, Proofpoint scientists estimate that cyber attackers may well be working with the loader to get a foothold into target networks and sell the entry to other actors in what is actually an “accessibility-as-a-services” scheme.
RustyBuer is the most recent in a collection of attempts aimed at adding an excess layer of opacity, as cybercriminals are paying improved focus to new programming languages in hopes that undertaking so will allow the attack code to slip past security defenses. Previously this calendar year, a malware termed “NimzaLoader” was discovered as published in Nim programming language, adopted by a macOS adware named “Convuster” that was primarily based on Rust.
“When paired with the makes an attempt by menace actors leveraging RustyBuer to additional legitimize their lures, it is achievable the attack chain may possibly be additional helpful in obtaining access and persistence,” the scientists concluded.
Uncovered this posting attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to go through more unique content material we publish.
Some sections of this posting are sourced from:
thehackernews.com


 After no ordinary year, congratulations to the 2021 SC Award winners
After no ordinary year, congratulations to the 2021 SC Award winners