As the probe into the SolarWinds source chain attack continues, new electronic forensic evidence has introduced to mild that a individual threat actor may perhaps have been abusing the IT infrastructure provider’s Orion software to drop a comparable persistent backdoor on concentrate on methods.
“The investigation of the full SolarWinds compromise led to the discovery of an supplemental malware that also influences the SolarWinds Orion item but has been decided to be likely unrelated to this compromise and utilised by a different danger actor,” Microsoft 365 exploration crew said on Friday in a put up detailing the Sunburst malware.
What makes the recently exposed malware, dubbed “Supernova,” different is that in contrast to the Sunburst DLL, Supernova (“application_web_logoimagehandler.ashx.b6031896.dll”) is not signed with a legit SolarWinds electronic certification, signaling that the compromise may possibly be unrelated to the formerly disclosed source chain attack.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In a standalone produce-up, scientists from Palo Alto Networks claimed the Supernova malware is compiled and executed in-memory, allowing the attacker to bypass endpoint detection and response (EDR) methods and “deploy total-showcased – and presumably refined – .NET systems in reconnaissance, lateral movement and other attack phases.”
How the Sunburst Backdoor Operates
The discovery is nonetheless a further sign that in addition to getting a worthwhile infection vector for danger actors, the supply chain attack of SolarWinds — which forged a extensive net of 18,000 providers and authorities companies — had been executed with a considerably broader scope and extraordinary sophistication.
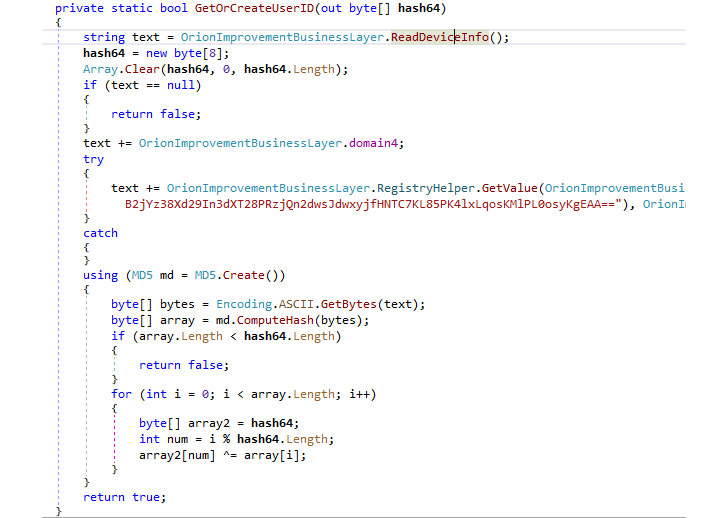
The adversaries applied what is actually known as a source chain attack, exploiting SolarWinds Orion network management software program updates the organization distributed in between March and June of this calendar year to plant destructive code in a DLL file (aka Sunburst or Solorigate) on the targets’ servers that’s able of stealthily collecting critical details, managing remote instructions, and exfiltrating the success to an attacker-managed server.
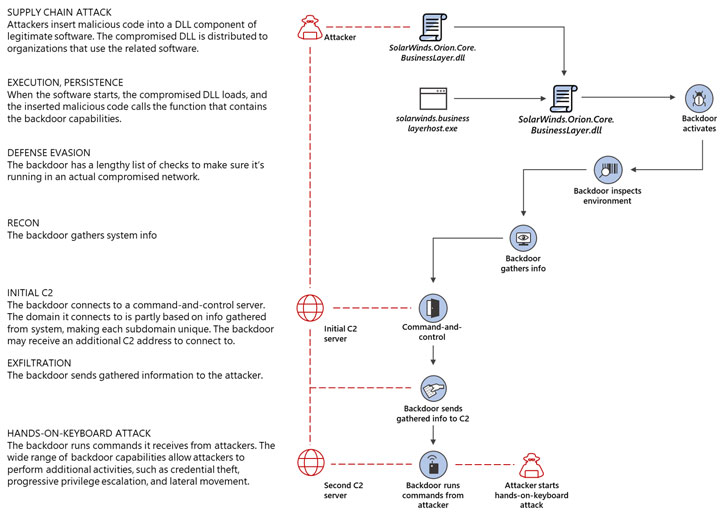
Assessment of the Solorigate modus operandi has also unveiled that the campaign chose to steal details only from a select number of of hundreds of victims, opting to escalate their attacks based mostly on intel amassed through an preliminary reconnaissance of the concentrate on atmosphere for substantial-benefit accounts and assets.
The escalation entails the predefined command-and-management (C2) server — a now-sinkholed domain identified as “avsvmcloud[.]com” — responding to the infected system with a next C2 server that permits the Sunburst backdoor to operate particular commands for privilege escalation exploration, credential theft, and lateral movement.
The simple fact that the compromised DLL file is digitally signed indicates a compromise of the firm’s software package improvement or distribution pipeline, with proof suggesting that the attackers have been conducting a dry operate of the marketing campaign as early as October 2019.
The Oct information did not have a backdoor embedded in them in the way that subsequent program updates SolarWinds Orion consumers downloaded in the spring of 2020 did — fairly, it was primarily employed to take a look at if the modifications showed up in the freshly launched updates as anticipated.
The US Cybersecurity and Infrastructure Security Agency (CISA), in an warn previous week, stated it identified evidence of first infection vectors employing flaws other than the SolarWinds software package.
Cisco, VMware, and Deloitte Verify Destructive Orion Installations
Cybersecurity companies Kaspersky and Symantec have explained they each determined 100 buyers who downloaded the trojanized package deal that contains the Sunburst backdoor, with the latter locating traces of a 2nd-phase payload termed Teardrop in a compact amount of businesses.
The distinct variety of contaminated victims stays mysterious at this time but has steadily amplified given that cybersecurity agency FireEye unveiled it experienced been breached through SolarWinds’s software early this month. A selection of US governing administration companies and private businesses, including Microsoft, Cisco, Equifax, General Electrical, Intel, NVIDIA, Deloitte, and VMware, have documented obtaining the malware on its servers.
“Subsequent the SolarWinds attack announcement, Cisco Security instantly commenced our recognized incident response procedures,” Cisco stated in a statement to The Hacker News via email.
“We have isolated and taken off Orion installations from a compact quantity of lab environments and employee endpoints. At this time, there is no recognized impression to Cisco products and solutions, providers, or to any buyer details. We proceed to investigate all features of this evolving circumstance with the maximum precedence.”
FireEye was the 1st to expose the huge-ranging espionage marketing campaign on December 8 right after exploring that the menace actor experienced stolen its arsenal of Red Team penetration screening resources, making it so much the only instance where by the attackers escalated accessibility as a result far. No overseas governments have announced compromises of their own units.
Despite the fact that media reviews have cited it to be the do the job of APT29, Russia has denied involvement in the hacking campaign. Neither have cybersecurity companies and scientists from FireEye, Microsoft, and Volexity attributed these attacks to the threat actor.
Located this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to browse a lot more exceptional written content we put up.
Some parts of this post are sourced from:
thehackernews.com


 Breach alerts dismissed as junk? New guide for sending vital emails may help
Breach alerts dismissed as junk? New guide for sending vital emails may help