A number of cybercriminal groups are leveraging a malware-as-a-assistance (MaaS) alternative to distribute a huge assortment of malicious program distribution campaigns that outcome in the deployment of payloads these types of as Campo Loader, Hancitor, IcedID, QBot, Buer Loader, and SocGholish in opposition to people today in Belgium as very well as govt companies, corporations, and corporations in the U.S.

Dubbed “Prometheus TDS” (limited for Traffic Path Program) and out there for sale on underground platforms for $250 a month because August 2020, the company is designed to distribute malware-laced Term and Excel documents and divert users to phishing and malicious internet sites, in accordance to a Group-IB report shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Much more than 3,000 email addresses are mentioned to have been singled out by way of destructive strategies in which Prometheus TDS was made use of to deliver destructive emails, with banking and finance, retail, energy and mining, cybersecurity, health care, IT, and coverage rising the well known verticals qualified by the attacks.
“Prometheus TDS is an underground support that distributes destructive information and redirects guests to phishing and destructive web sites,” Team-IB scientists said. “This service is produced up of the Prometheus TDS administrative panel, in which an attacker configures the essential parameters for a malicious campaign: downloading destructive files, and configuring constraints on users’ geolocation, browser model, and running method.”
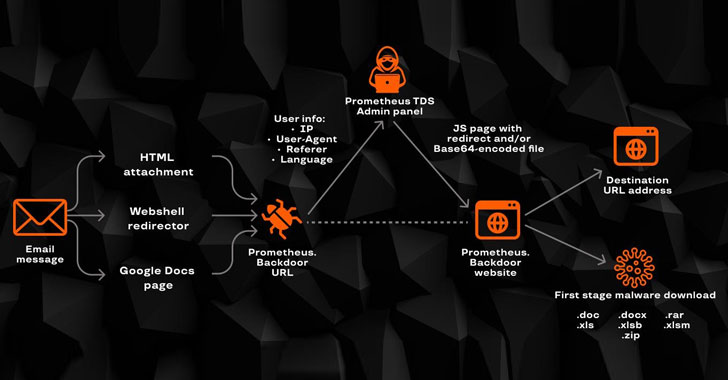
The provider is also regarded to use 3rd-party infected web sites that are manually extra by the campaign’s operators and act as a intermediary among the attacker’s administrative panel and the consumer. To realize this, a PHP file named “Prometheus.Backdoor” is uploaded to the compromised web site to obtain and mail again details about the target, based on which a selection is taken as to irrespective of whether to mail the payload to the person and/or to redirect them to the specified URL.
The attack scheme commences with an email containing a HTML file, a website link to a web shell that redirects buyers to a specified URL, or a url to a Google Doc which is embedded with an URL that redirects buyers to the malicious hyperlink that when both opened or clicked prospects the recipient to the contaminated website, which stealthily collects simple facts (IP address, Consumer-Agent, Referrer header, time zone, and language info) and then forwards this knowledge to the Prometheus admin panel.

In the last section, the administrative panel will take duty for sending a command to redirect the person to a particular URL, or to deliver a malware-ridden Microsoft Word or Excel doc, with the consumer redirected to a authentic website like DocuSign or USPS quickly right after downloading the file to mask the destructive exercise. Apart from distributing destructive documents, scientists located that Prometheus TDS is also used as a classic TDS to redirect end users to particular web-sites, such as phony VPN web-sites, dubious portals providing Viagra and Cialis, and banking phishing web-sites.
“Prometheus TDS also redirected people to web sites promoting pharmaceutical products,” the researchers mentioned. “Operators of these types of web pages frequently have affiliate and partnership plans. Companions, in change, often resort to intense SPAM campaigns in get to raise the earnings in just the affiliate plan. Assessment of the Prometheus infrastructure by Team-IB specialists unveiled back links that redirect users to web sites relating to a Canadian pharmaceutical firm.”
Found this write-up attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to examine far more distinctive material we submit.
Some pieces of this post are sourced from:
thehackernews.com

 Unpatched Security Flaws Expose Mitsubishi Safety PLCs to Remote Attacks
Unpatched Security Flaws Expose Mitsubishi Safety PLCs to Remote Attacks