Researchers from Qihoo 360’s Netlab security workforce have released details of a new evolving botnet termed “Abcbot” that has been noticed in the wild with worm-like propagation features to infect Linux methods and start dispersed denial-of-company (DDoS) attacks from targets.
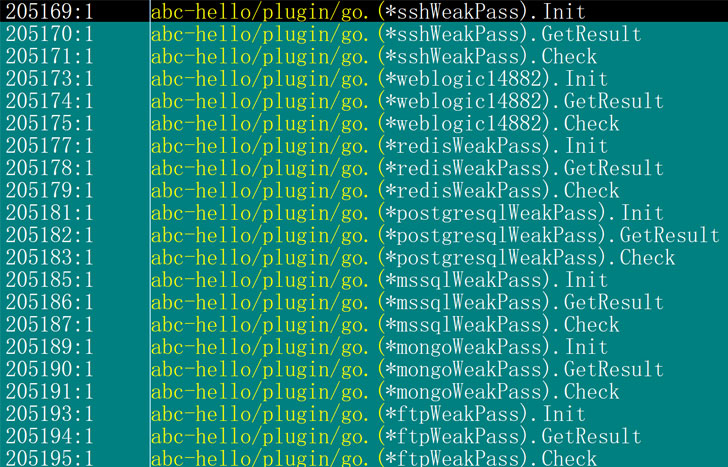
Although the earliest variation of the botnet dates again to July 2021, new variants observed as lately as Oct 30 have been outfitted with more updates to strike Linux web servers with weak passwords and are prone to N-working day vulnerabilities, including a custom implementation of DDoS functionality, indicating that the malware is under steady development.
Netlab’s results also construct on a report from Pattern Micro early final thirty day period, which publicized attacks concentrating on Huawei Cloud with cryptocurrency-mining and cryptojacking malware. The intrusions had been also noteworthy for the actuality that the malicious shell scripts specifically disabled a course of action made to observe and scan the servers for security issues as nicely as reset users’ passwords to the Elastic cloud services.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Now in accordance to the Chinese internet security company, these shell scripts are being utilized to unfold Abcbot. A complete of six variations of the botnet have been observed to day.
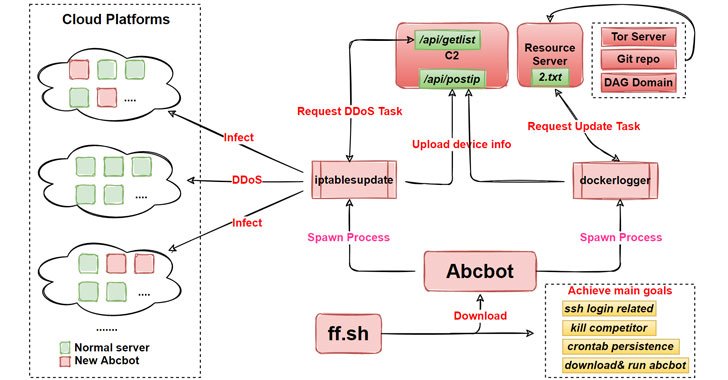
Once mounted on a compromised host, the malware triggers the execution of a series of steps that outcomes in the contaminated system staying repurposed as a web server, in addition to reporting the program information and facts to a command-and-manage (C2) server, spreading the malware to new equipment by scanning for open ports, and self-updating alone as and when new options are designed out there by its operators.
“Attention-grabbing factor is that the sample [updated] on Oct 21 employs the open-source ATK Rootkit to apply the DDoS function,” a system which the scientists stated “demands Abcbot to down load the supply code, compile, and load the rootkit module right before doing [a] DDoS attack.”
“This course of action calls for as well many methods, and any step that is faulty will final result in the failure of the DDoS operate,” the researchers noted, foremost the adversary to replace the off-the-shelf code with a personalized attack module in a subsequent edition produced on October 30 that wholly abandons the ATK rootkit.

The conclusions occur a tiny above a week following the Netlab security group disclosed particulars of a “Pink” botnet that’s believed to have infected over 1.6 million units mostly positioned in China with the aim of launching DDoS attacks and inserting advertisements into HTTP web sites visited by unsuspecting end users. In a similar enhancement, AT&T Alien Labs took the wraps off a new Golang malware dubbed “BotenaGo” that has been found out making use of about 30 exploits to attack millions of routers and IoT devices possibly.
“The update method in these six months is not so substantially a constant upgrade of functions as a trade-off in between diverse systems,” the scientists concluded. “Abcbot is slowly but surely going from infancy to maturity. We do not think about this phase to be the ultimate type, there are definitely lots of places of advancement or capabilities to be formulated at this phase.”
Uncovered this report appealing? Abide by THN on Fb, Twitter and LinkedIn to examine a lot more distinctive content we write-up.
Some parts of this report are sourced from:
thehackernews.com

 Hackers Exploit macOS Zero-Day to Hack Hong Kong Users with new Implant
Hackers Exploit macOS Zero-Day to Hack Hong Kong Users with new Implant