The maintainers of Exim have produced patches to remediate as a lot of as 21 security vulnerabilities in its software that could help unauthenticated attackers to realize full distant code execution and obtain root privileges.
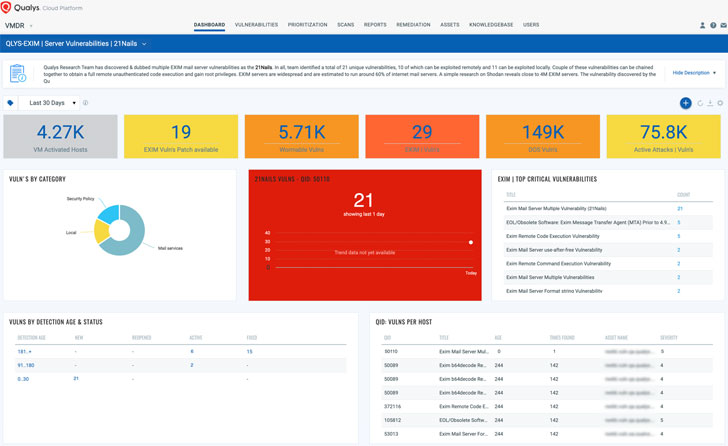
Collectively named ’21Nails,’ the flaws incorporate 11 vulnerabilities that need area obtain to the server and 10 other weaknesses that could be exploited remotely. The issues have been discovered by Qualys and described to Exim on Oct. 20, 2020.
“Some of the vulnerabilities can be chained jointly to acquire a complete remote unauthenticated code execution and attain root privileges on the Exim Server,” Bharat Jogi, senior manager at Qualys, said in public disclosure. “Most of the vulnerabilities found out by the Qualys Research Group for e.g. CVE-2020-28017 influences all variations of Exim likely back all the way to 2004.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Exim is a popular mail transfer agent (MTA) used on Unix-like running units, with in excess of 60% of the publicly reachable mail servers on the Internet managing the software program.
“In accordance to a modern survey, an approximated 60% of internet servers run on Exim. A Shodan research reveals nearly 4 million Exim servers are uncovered to the internet.”
Exim Mail Server Numerous Vulnerabilities (21Nails) from Qualys, Inc. on Vimeo.
A fast summary of the 21 bugs is listed under. If correctly exploited, they could be made use of to tweak email configurations and even increase new accounts on the compromised mail servers. Specialized specifics about the flaws can be accessed right here.
Nearby vulnerabilities:
- CVE-2020-28007: Link attack in Exim’s log directory
- CVE-2020-28008: Assorted attacks in Exim’s spool directory
- CVE-2020-28014: Arbitrary file creation and clobbering
- CVE-2021-27216: Arbitrary file deletion
- CVE-2020-28011: Heap buffer overflow in queue_operate()
- CVE-2020-28010: Heap out-of-bounds compose in key()
- CVE-2020-28013: Heap buffer overflow in parse_resolve_phrase()
- CVE-2020-28016: Heap out-of-bounds compose in parse_fix_phrase()
- CVE-2020-28015: New-line injection into spool header file (nearby)
- CVE-2020-28012: Lacking near-on-exec flag for privileged pipe
- CVE-2020-28009: Integer overflow in get_stdinput()
Distant vulnerabilities:
- CVE-2020-28017: Integer overflow in obtain_include_recipient()
- CVE-2020-28020: Integer overflow in obtain_msg()
- CVE-2020-28023: Out-of-bounds browse in smtp_setup_msg()
- CVE-2020-28021: New-line injection into spool header file (distant)
- CVE-2020-28022: Heap out-of-bounds read through and write in extract_solution()
- CVE-2020-28026: Line truncation and injection in spool_examine_header()
- CVE-2020-28019: Failure to reset function pointer immediately after BDAT mistake
- CVE-2020-28024: Heap buffer underflow in smtp_ungetc()
- CVE-2020-28018: Use-soon after-absolutely free in tls-openssl.c
- CVE-2020-28025: Heap out-of-bounds browse in pdkim_finish_bodyhash()
In light-weight of the modern Microsoft Trade server hacks, it is essential the patches are used quickly, as email servers have emerged as a profitable focus on for espionage campaigns. In the previous, flaws in Exim program have been actively exploited by negative actors to mount a wide variety of attacks, such as deploying a Linux worm to put in cryptocurrency miners on influenced servers.
Final May, the U.S. Nationwide Security Company (NSA) warned that Russian navy operatives, publicly regarded as Sandworm Team, have been having edge of a remote code execution vulnerability tracked as CVE-2019-10149 (aka The Return of the WIZard) to “add privileged users, disable network security settings, execute more scripts for more network exploitation” at the very least due to the fact August 2019.
The NSA termed it an “attacker’s aspiration accessibility.”
“Mail Transfer Agents are intriguing targets for attackers since they are commonly obtainable around the internet,” Jogi said. “When exploited, they could modify sensitive email configurations on the mail servers, allow adversaries to build new accounts on the concentrate on mail servers.”
Found this write-up appealing? Comply with THN on Facebook, Twitter and LinkedIn to read additional special articles we write-up.
Some parts of this post are sourced from:
thehackernews.com


 21 vulnerabilities in Exim mail server leave web, cloud operations exposed
21 vulnerabilities in Exim mail server leave web, cloud operations exposed