IT infrastructure management service provider SolarWinds on Thursday produced a new update to its Orion networking monitoring device with fixes for four security vulnerabilities, counting two weaknesses that could be exploited by an authenticated attacker to achieve distant code execution (RCE).
Chief among them is a JSON deserialization flaw that enables an authenticated user to execute arbitrary code by means of the test notify actions characteristic out there in the Orion Web Console, which allows people simulate network gatherings (e.g., an unresponsive server) that can be configured to bring about an inform throughout setup. It has been rated critical in severity.
A second issue worries a superior-risk vulnerability that could be leveraged by an adversary to reach RCE in the Orion Job Scheduler. “In buy to exploit this, an attacker initially needs to know the qualifications of an unprivileged area account on the Orion Server,” SolarWinds claimed in its release notes.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The advisory is light on complex particulars, but the two shortcomings are said to have been documented by means of Development Micro’s Zero Day Initiative.
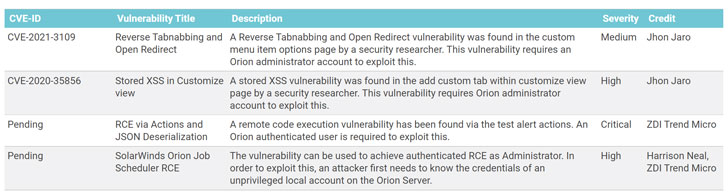
Apart from the aforementioned two flaws, the update squashes two other bugs, which include a large-severity saved cross-web page scripting (XSS) vulnerability in the “add custom tab” in just customize see site (CVE-2020-35856) and a reverse tabnabbing and open redirect vulnerability in the personalized menu merchandise choices page (CVE-2021-3109), both equally of which require an Orion administrator account for productive exploitation.
The new update also brings a amount of security improvements, with fixes for avoiding XSS attacks and enabling UAC protection for Orion databases supervisor, amid other folks.
The most recent round of fixes arrives almost two months just after the Texas-primarily based corporation tackled two critical security vulnerabilities impacting Orion System (CVE-2021-25274 and CVE-2021-25275), which could have been exploited to obtain remote code execution with elevated privileges.
Orion consumers are suggested to update to the newest release, “Orion System 2020.2.5,” to mitigate the risk related with the security issues.
Uncovered this article fascinating? Follow THN on Facebook, Twitter and LinkedIn to go through a lot more exclusive written content we put up.
Some areas of this post are sourced from:
thehackernews.com

 Fleeceware Apps Bank $400M in Revenue
Fleeceware Apps Bank $400M in Revenue