Cybersecurity researchers have disclosed an unpatched flaw in Apple Pay out that attackers could abuse to make an unauthorized Visa payment with a locked iPhone by using gain of the Categorical Journey mode established up in the device’s wallet.
“An attacker only requirements a stolen, driven on iPhone. The transactions could also be relayed from an iPhone inside someone’s bag, without the need of their awareness,” a team of teachers from the University of Birmingham and College of Surrey mentioned. “The attacker needs no help from the service provider and backend fraud detection checks have not stopped any of our exam payments.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Categorical Journey is a aspect that permits end users of iPhone and Apple Check out to make swift contactless payments for public transit without having possessing to wake or unlock the gadget, open up an app, or even validate with Deal with ID, Touch ID or a passcode.
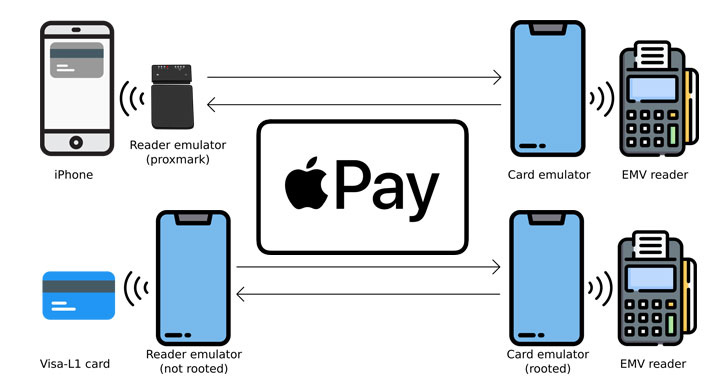
The guy-in-the-middle (MitM) replay and relay attack, which includes bypassing the lock display screen to make a payment to any EMV reader illicitly, is created feasible owing to a mix of flaws in both Apple Spend and Visa’s technique, and will not effect, say, Mastercard on Apple Pay or Visa cards on Samsung Pay.
The modus operandi hinges on mimicking a transit gate transaction by employing a Proxmark machine that functions as an EMV card reader communicating with a victim’s iPhone and an NFC-enabled Android app that capabilities as a card emulator to relay signals to a payment terminal.
Specifically, it usually takes edge of a distinctive code — aka Magic Bytes — broadcast by the transit gates to unlock Apple Shell out, resulting in a scenario whereby replaying the sequence of bytes, the Apple device is deceived into authorizing a rogue transaction as if it truly is originated from the ticket barrier, when, in reality, it’s been induced by means of a contactless payment terminal below the attacker’s manage.

At the similar time, the EMV reader is also tricked into believing that on-gadget user authentication has been executed, thus enabling payments of any sum to be made devoid of the iPhone user’s awareness.
Apple and Visa have been alerted to the vulnerability in October 2020 and Could 2021, respectively, the scientists mentioned, incorporating, “both functions accept the seriousness of the vulnerability, but have not come to an settlement on which party really should implement a correct.”
In a statement shared with the BBC, Visa reported this style of attack was “impractical,” adding, “Variants of contactless fraud strategies have been examined in laboratory settings for additional than a 10 years and have proven to be impractical to execute at scale in the actual environment.”
“This is a worry with a Visa technique but Visa does not feel this kind of fraud is possible to consider position in the real environment offered the several layers of security in location,” an Apple spokesperson was quoted as indicating to the U.K. nationwide broadcaster.
Uncovered this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to examine much more unique content material we publish.
Some areas of this report are sourced from:
thehackernews.com

 Malware pretending to be Amnesty International antivirus for Pegasus discovered
Malware pretending to be Amnesty International antivirus for Pegasus discovered