Apple very last 12 months fastened a new set of macOS vulnerabilities that exposed Safari browser to attack, perhaps making it possible for destructive actors to entry users’ on-line accounts, microphone, and webcam.
Security researcher Ryan Pickren, who found out and noted the bugs to the iPhone maker, was compensated with a $100,500 bug bounty, underscoring the severity of the issues.
By exploiting a chain of security issues with iCloud Sharing and Safari 15, it permits the attacker to hijack the multimedia permission and get “comprehensive obtain to each web page ever visited by the victim” in Safari, including Gmail, iCloud, Facebook, and PayPal accounts.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

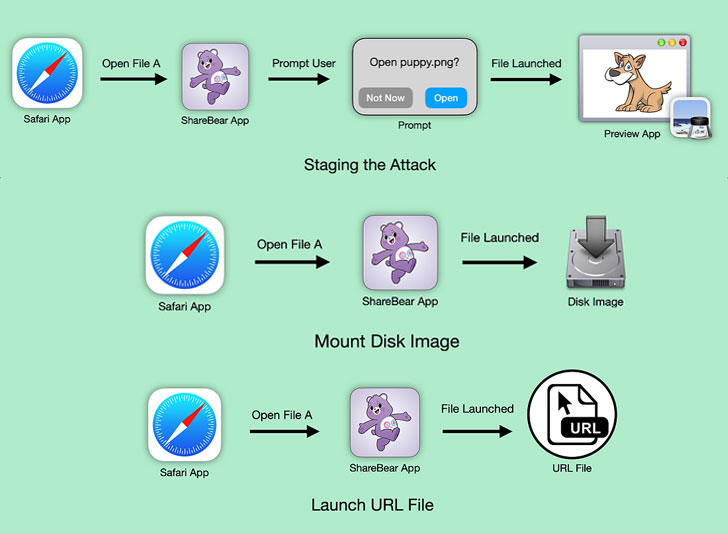
The issues exclusively problem ShareBear, an iCloud file-sharing mechanism that prompts users upon attempting to open a shared doc for the initially time. Getting benefit of the reality that users are never shown the prompt once again the moment they accept to open the file, Pickren found that it is doable to change the file’s material to anything at all by any person with obtain to the file.
“ShareBear will then down load and update the file on the victim’s machine devoid of any person conversation or notification,” Pickren described in a technical write-up. “In essence, the sufferer has given the attacker authorization to plant a polymorphic file onto their machine and the authorization to remotely start it at any minute.”
In other words, an impression file with a .PNG format could have its overall content and extension altered to an executable binary (“evil.dmg”) immediately after the consumer has agreed to open up it. The binary can then be launched, triggering an exploit chain that leverages added flaws found out in Safari to get more than the machine’s mic or webcam, or even steal community information —
- CVE-2021-30861 – A logic issue in WebKit that could allow for a destructive application to bypass Gatekeeper checks
- CVE-2021-30975 – An issue in Script Editor that could allow a destructive OSAX scripting addition to bypass Gatekeeper checks and circumvent sandbox limits
This is the second time Pickren has disclosed flaws in iOS and macOS that, if properly exploited, could be abused to entry the camera in an unauthorized fashion upon traveling to a specially crafted website.
“This task was an fascinating exploration of how a style flaw in 1 software can allow a wide range of other, unrelated, bugs to develop into a lot more unsafe,” Pickren reported. “It was also a terrific illustration of how even with macOS Gatekeeper enabled, an attacker can nevertheless accomplish a whole lot of mischief by tricking authorized apps into accomplishing malicious factors.”
Observed this short article interesting? Follow THN on Facebook, Twitter and LinkedIn to read a lot more exceptional material we put up.
Some areas of this posting are sourced from:
thehackernews.com


 DeepDotWeb News Site Operator Sentenced to 8 Years for Money Laundering
DeepDotWeb News Site Operator Sentenced to 8 Years for Money Laundering