Apple on Monday released a security update for iOS and iPad to deal with a critical vulnerability that it suggests is remaining exploited in the wild, generating it the 17th zero-working day flaw the enterprise has addressed in its products due to the fact the begin of the year.’
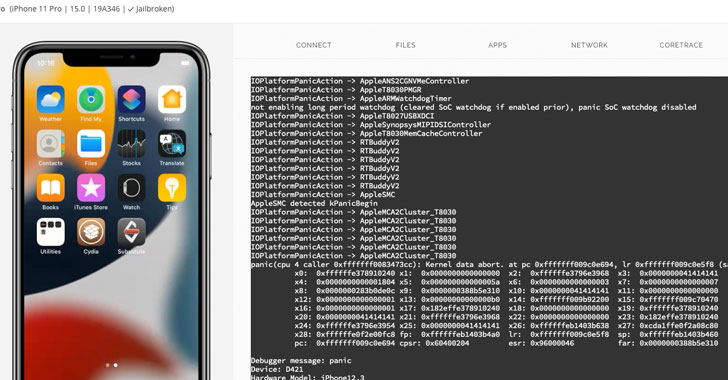
The weak point, assigned the identifier CVE-2021-30883, worries a memory corruption issue in the “IOMobileFrameBuffer” part that could allow for an application to execute arbitrary code with kernel privileges. Crediting an anonymous researcher for reporting the vulnerability, Apple claimed it truly is “informed of a report that this issue may well have been actively exploited.”
Technical specifics about the flaw and the nature of the attacks continue to be unavailable as nonetheless, as is the identification of the menace actor, so as to enable a greater part of the consumers to utilize the patch and reduce other adversaries from weaponizing the vulnerability. The iPhone maker said it resolved the issue with enhanced memory handling.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Security researcher Saar Amar shared further specifics, and a proof-of-strategy (PoC) exploit, noting that “this attack surface is extremely appealing because it really is available from the app sandbox (so it really is wonderful for jailbreaks) and lots of other procedures, generating it a superior prospect for LPEs exploits in chains.”
CVE-2021-30883 is also the 2nd zero-day impacting IOMobileFrameBuffer soon after Apple addressed a equivalent, anonymously reported memory corruption issue (CVE-2021-30807) in July 2021, boosting the possibility that the two flaws could be relevant. With the most recent repair, the firm has settled a record 17 zero-times to date in 2021 alone —
- CVE-2021-1782 (Kernel) – A malicious software could be ready to elevate privileges
- CVE-2021-1870 (WebKit) – A distant attacker might be able to cause arbitrary code execution
- CVE-2021-1871 (WebKit) – A distant attacker may possibly be able to bring about arbitrary code execution
- CVE-2021-1879 (WebKit) – Processing maliciously crafted web content may possibly lead to common cross-web-site scripting
- CVE-2021-30657 (System Tastes) – A malicious application could bypass Gatekeeper checks
- CVE-2021-30661 (WebKit Storage) – Processing maliciously crafted web written content may possibly guide to arbitrary code execution
- CVE-2021-30663 (WebKit) – Processing maliciously crafted web written content may guide to arbitrary code execution
- CVE-2021-30665 (WebKit) – Processing maliciously crafted web written content could guide to arbitrary code execution
- CVE-2021-30666 (WebKit) – Processing maliciously crafted web content material may possibly lead to arbitrary code execution
- CVE-2021-30713 (TCC framework) – A malicious application may be equipped to bypass Privacy choices
- CVE-2021-30761 (WebKit) – Processing maliciously crafted web material may perhaps lead to arbitrary code execution
- CVE-2021-30762 (WebKit) – Processing maliciously crafted web content material may perhaps direct to arbitrary code execution
- CVE-2021-30807 (IOMobileFrameBuffer) – An software may be capable to execute arbitrary code with kernel privileges
- CVE-2021-30858 (WebKit) – Processing maliciously crafted web information may well lead to arbitrary code execution
- CVE-2021-30860 (CoreGraphics) – Processing a maliciously crafted PDF could direct to arbitrary code execution
- CVE-2021-30869 (XNU) – A destructive application may be ready to execute arbitrary code with kernel privileges
Apple iPhone and iPad consumers are highly advised to update to the hottest edition (iOS 15..2 and iPad 15..2) to mitigate the security vulnerability.
Observed this article interesting? Adhere to THN on Fb, Twitter and LinkedIn to examine a lot more distinctive articles we post.
Some parts of this article are sourced from:
thehackernews.com

 Couple Arrested Over Sale of Nuclear Secrets
Couple Arrested Over Sale of Nuclear Secrets