Most current investigation has demonstrated a new exploit that enables arbitrary facts to be uploaded from units that are not connected to the Internet by basically sending “Uncover My Bluetooth” broadcasts to nearby Apple equipment.
“It’s achievable to upload arbitrary info from non-internet-related devices by sending Find My [Bluetooth Low Energy] broadcasts to close by Apple gadgets that then upload the information for you,” Beneficial Security researcher Fabian Bräunlein said in a complex write-up disclosed last 7 days.
“Becoming inherent to the privacy and security-focused style of the Locate My Offline Locating program, it appears to be unlikely that this misuse can be prevented completely.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The review builds on a prior study by TU Darmstadt posted in March 2021, which disclosed two unique style and design and implementation flaws in Apple’s crowdsourced Bluetooth location tracking procedure that could lead to a area correlation attack and unauthorized obtain to a user’s site background of the earlier 7 days.
The investigation was augmented by the release of a framework called OpenHaystack that’s developed to permit any user develop an “AirTag,” enabling people to monitor own Bluetooth gadgets by means of Apple’s huge Locate My network.
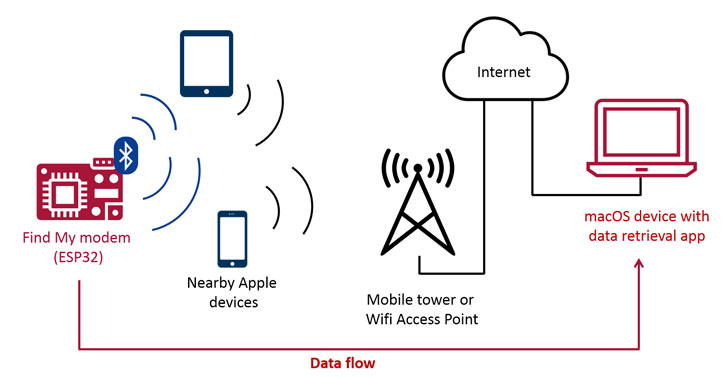
But the reverse engineering of Apple’s Obtain My offline discovering program also still left the doorway open up to the probability that the protocol could be emulated to upload arbitrary data to the Internet by broadcasting the info by using Bluetooth beacons that would get picked up by Apple equipment in near physical proximity, and then subsequently relay the encrypted data to Apple’s servers, from wherever a macOS application can retrieve, decode, and show the uploaded facts.
A single of the core factors of Find My is its rotating crucial plan consisting of a pair of community-non-public keys that are deterministically improved each 15 minutes, with the general public essential sent inside of the Bluetooth Low Electricity advertisement packet.
Therefore when nearby Apple units such as MacBooks, iPhones, and iPads get the broadcast, they fetch their individual location, then encrypt the place making use of the aforementioned public vital in advance of sending the encrypted place report to iCloud along with a hash of the public essential. In the remaining phase, the operator of the lost machine can use a next Apple machine signed in with the exact Apple ID to accessibility the approximate area.
The encryption protections imply that not only does Apple not know which public keys belong to a particular misplaced system or AirTag, it also does not have any knowledge of which locale studies are meant for a particular person — hence the above Apple ID prerequisite. “The security only lies in the encryption of the site experiences: The site can only be decrypted with the correct private crucial, which is infeasible to brute pressure and only stored on the paired Owner Machine,” Bräunlein mentioned.
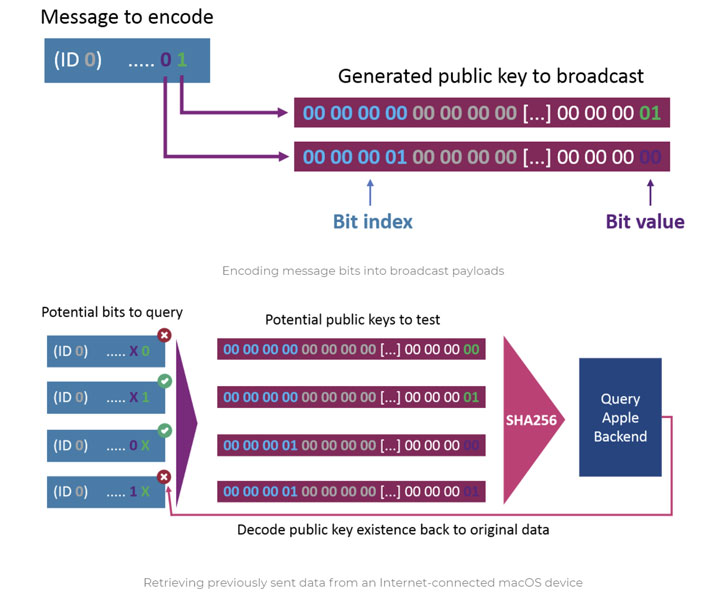
The notion, for that reason, is to exploit this hole by encoding a concept into the broadcast payloads and then getting them on the other stop making use of a information fetcher part based on OpenHaystack that decrypts and extracts the information transmitted from the sender device, say, a microcontroller.
“When sending, the information is encoded in the public keys that are broadcasted by the microcontroller. Close by Apple units will pick up individuals broadcasts and forward the details to an Apple backend as element of their area reporting. Individuals experiences can afterwards be retrieved by any Mac device to decode the despatched info,” Bräunlein spelled out.
When destructive actual-earth implications of these types of an exploit may possibly seem to be moot, it can be also hard for Apple to protect towards an attack of this variety due to the finish-to-conclusion encrypted nature of the Uncover My network. To counter this sort of unintended employs, the researcher suggests hardening the program in two attainable strategies, which include authenticating the BLE advertisement and implementing rate restrictions on-location report retrievals by caching the hashes and guaranteeing that the only “16 new key ids are queried for every 15 minutes and Apple ID.” It can be value noting that there is a restrict of 16 AirTags for every Apple ID.
“In the planet of substantial-security networks, where combining lasers and scanners appears to be a noteworthy procedure to bridge the air gap, the visitor’s Apple equipment may possibly also become possible intermediaries to exfiltrate data from specified air gapped devices or Faraday caged rooms,” Bräunlein reported.
Identified this article exciting? Observe THN on Fb, Twitter and LinkedIn to read through far more distinctive material we article.
Some components of this short article are sourced from:
thehackernews.com

 Cisco Snaps Up Kenna Security for Vulnerability Management
Cisco Snaps Up Kenna Security for Vulnerability Management