A danger actor acknowledged for striking targets in the Middle East has advanced its Android spyware however all over again with increased capabilities that enable it to be stealthier and additional persistent though passing off as seemingly innocuous application updates to continue to be under the radar.
The new variants have “incorporated new attributes into their malicious applications that make them far more resilient to steps by consumers, who may possibly test to clear away them manually, and to security and web hosting companies that endeavor to block access to, or shut down, their command-and-regulate server domains,” Sophos risk researcher Pankaj Kohli reported in a report released Tuesday.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Also identified by the monikers VAMP, FrozenCell, GnatSpy, and Desert Scorpion, the mobile adware has been a most popular software of option for the APT-C-23 risk team due to the fact at least 2017, with successive iterations featuring extended surveillance features to vacuum files, photos, contacts and contact logs, read through notifications from messaging applications, report calls (together with WhatsApp), and dismiss notifications from created-in Android security apps.
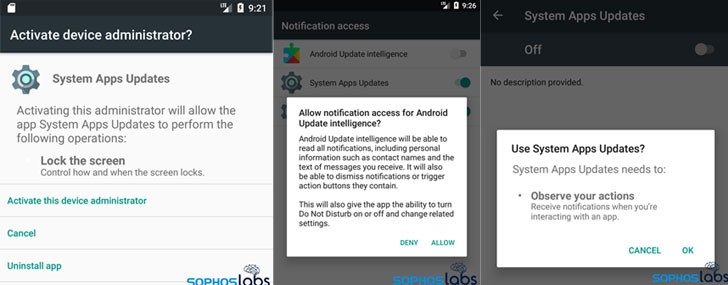
In the earlier, the malware has been distributed by using pretend Android app suppliers under the guise of AndroidUpdate, Threema, and Telegram. The hottest marketing campaign is no distinct in that they consider the sort of applications that purport to install updates on the target’s phone with names these kinds of as Application Updates, Method Applications Updates, and Android Update Intelligence. It is really believed that the attackers produce the spy ware application by sending a down load website link to the targets by smishing messages.

At the time mounted, the application commences requesting for invasive permissions to execute a string of destructive pursuits that are built to slip earlier any tries to manually remove the malware. The application not only adjustments its icon to hide driving popular applications these as Chrome, Google, Google Participate in, and YouTube, in the function the user have been to click the fraudulent icon, the authentic edition of the app is launched, whilst running surveillance tasks in the track record.
“Spyware is a growing risk in an progressively related globe,” Kohli claimed. “The Android spyware linked to APT-C-23 has been about for at the very least 4 decades, and attackers carry on to acquire it with new tactics that evade detection and removing.”
Located this short article appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through more exclusive articles we write-up.
Some areas of this posting are sourced from:
thehackernews.com


 Over 9 Million Android Phones Running Malware Apps from Huawei’s AppGallery
Over 9 Million Android Phones Running Malware Apps from Huawei’s AppGallery