It is really just one issue for APT teams to conduct cyber espionage to meet up with their have economic aims. But it can be an entirely different make any difference when they are used as “hackers for employ” by competing private organizations to make absent with confidential details.
Bitdefender’s Cyber Danger Intelligence Lab uncovered nevertheless one more occasion of an espionage attack focusing on an unnamed intercontinental architectural and video clip manufacturing corporation that had all the hallmarks of a very carefully orchestrated campaign.
“The cybercriminal group infiltrated the corporation applying a tainted and specifically crafted plugin for Autodesk 3ds Max,” Bitdefender researchers said in a report introduced right now.
“The investigation also located that the Command and Control infrastructure used by the cybercriminal group to examination their malicious payload versus the organization’s security resolution, is positioned in South Korea.”
Although there have been former circumstances of APT mercenary groups these as Dark Basin and Deceptikons (aka DeathStalker) targeting the monetary and authorized sector, this is the to start with time a threat actor has employed the exact same modus operandi to the serious-estate marketplace.
Past month, a identical campaign — called StrongPity — was found working with tainted application installers as a dropper to introduce a backdoor for document exfiltration.
“This is very likely to become the new ordinary in terms of the commoditization of APT groups — not just state-sponsored actors, but by anyone trying to get their solutions for personalized get, across all industries,” the cybersecurity firm mentioned.
Utilizing a Tainted Autodesk 3ds Max Plugin
In an advisory printed earlier this month, Autodesk warned buyers about a variant of “PhysXPluginMfx” MAXScript exploit that can corrupt 3ds Max’s configurations, operate destructive code, and propagate to other MAX files on a Windows program upon loading the contaminated files into the software package.
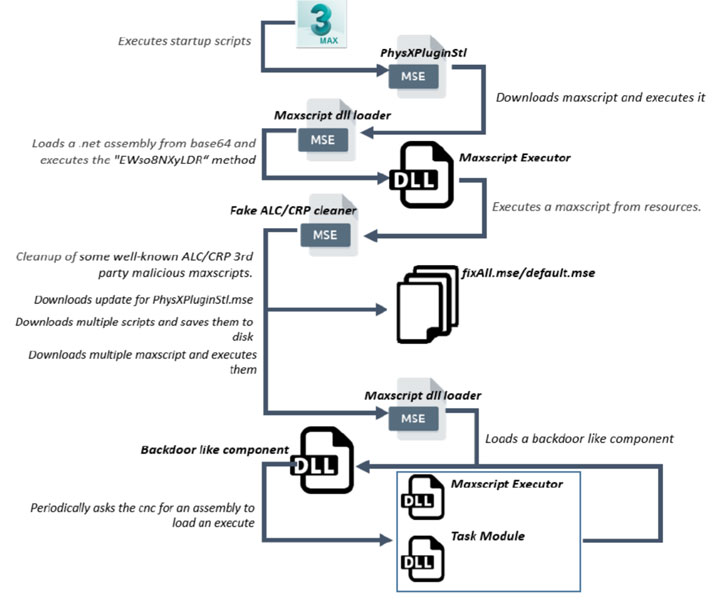
But according to Bitdefender’s forensic assessment, this sketchy MAXScript Encrypted sample (“PhysXPluginStl.mse”) contained an embedded DLL file, which subsequently went on to download further .Internet binaries from the C&C server with the greatest objective of stealing vital documents.
The binaries, in switch, are liable for downloading other malicious MAXScripts able of gathering facts about the compromised device and exfiltrating the details to the distant server, which transmits a remaining payload that can seize screenshots and acquire passwords from web browsers these kinds of as Firefox, Google Chrome, and Internet Explorer.
Aside from using a rest system to lie less than the radar and evade detection, Bitdefender researchers also found that the malware authors experienced an full toolset for spying upon its victims, which include a “HdCrawler” binary, whose work is to enumerate and add files with certain extensions (.webp, .jpg, .png, .zip, .obb, .uasset, and so on.) to the server, and an information-stealer with intensive capabilities.
The data amassed by the stealer ranges from the username, laptop identify, the IP addresses of network adapters, Windows ProductName, variation of the .Internet Framework, processors (quantity of cores, the speed, and other info), complete and no cost RAM out there, storage aspects to the names of procedures running on the process, the data files set to commence quickly adhering to a boot, and the list of current documents accessed.
Bitdefender’s telemetry data also uncovered other very similar malware samples speaking with the identical C&C server, courting back to just beneath a thirty day period in the past, suggesting that the team targets other victims.
It can be proposed that 3ds Max customers obtain the newest model of Security Applications for Autodesk 3ds Max 2021-2015SP1 to establish and get rid of the PhysXPluginMfx MAXScript malware.
“The sophistication of the attack reveals an APT-design and style team that experienced prior know-how of the firm’s security units and applied software program applications, meticulously organizing their attack to infiltrate the enterprise and exfiltrate data undetected,” the scientists claimed.
“Industrial espionage is very little new and, because the actual-estate market is remarkably competitive, with contracts valued at billions of dollars, the stakes are large for winning contracts for luxury projects and could justify turning to mercenary APT groups for gaining a negotiation advantage.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Identified this post exciting? Follow THN on Fb, Twitter and LinkedIn to go through extra exclusive information we put up.


 New Mercenary APT Team Focused Autodesk Program
New Mercenary APT Team Focused Autodesk Program