Aspects of an 8-12 months-previous security vulnerability in the Linux kernel have emerged that the researchers say is “as awful as Dirty Pipe.”
Dubbed DirtyCred by a group of academics from Northwestern College, the security weak point exploits a formerly unfamiliar flaw (CVE-2022-2588) to escalate privileges to the highest degree.
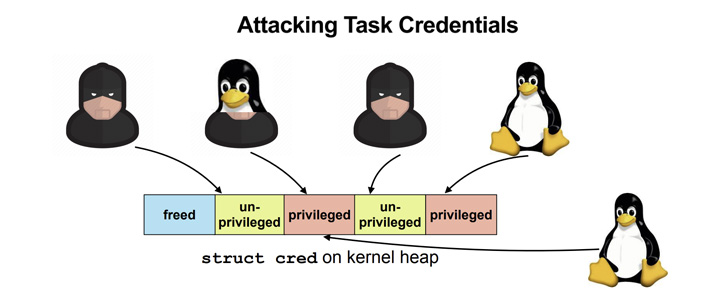
“DirtyCred is a kernel exploitation thought that swaps unprivileged kernel qualifications with privileged ones to escalate privilege,” researchers Zhenpeng Lin, Yuhang Wu, and Xinyu Xing noted. “As a substitute of overwriting any critical info fields on kernel heap, DirtyCred abuses the heap memory reuse system to get privileged.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

This involves three actions –
- Free of charge an in-use unprivileged credential with the vulnerability
- Allocate privileged credentials in the freed memory slot by triggering a privileged userspace approach these types of as su, mount, or sshd
- Work as a privileged user
The novel exploitation system, in accordance to the scientists, pushes the soiled pipe to the future level, earning it additional standard as properly as potent in a manner that could work on any edition of the influenced kernel.
“Initial, somewhat than tying to a specific vulnerability, this exploitation technique will allow any vulnerabilities with double-no cost ability to exhibit soiled-pipe-like potential,” the researchers stated.
“Next, while it is like the dirty pipe that could bypass all the kernel protections, our exploitation approach could even show the means to escape the container actively that Dirty Pipe is not capable of.”

Filthy Pipe, tracked as CVE-2022-0847 (CVSS score: 7.8) and impacting Linux kernel variations beginning from 5.8, refers to a security vulnerability in the pipe subsystem that permits underprivileged procedures to create to arbitrary readable documents, leading to privilege escalation.
The exploitable vulnerability was so referred to as following the Soiled Cow vulnerability identified in 2016 based on their similarities.
Specified that objects are isolated based mostly on their sort and not privileges, the researchers advocate isolating privileged credentials from unprivileged ones applying virtual memory to stop cross-cache attacks.
Identified this post exciting? Comply with THN on Facebook, Twitter and LinkedIn to examine additional distinctive content material we submit.
Some pieces of this short article are sourced from:
thehackernews.com

 Meet Borat RAT, a New Unique Triple Threat
Meet Borat RAT, a New Unique Triple Threat