Cybersecurity scientists have disclosed five earlier unreported security vulnerabilities influencing B. Braun’s Infusomat Place Significant Volume Pump and SpaceStation that could be abused by destructive get-togethers to tamper with treatment doses without the need of any prior authentication.
McAfee, which identified and reported the flaws to the German health-related and pharmaceutical product corporation on January 11, 2021, explained the “modification could seem as a unit malfunction and be seen only soon after a significant quantity of drug has been dispensed to a affected individual, due to the fact the infusion pump shows exactly what was prescribed, all while dispensing potentially deadly doses of medicine.”
The issues have been tackled by B. Braun in SpaceCom L82 or later on, Battery Pack SP with WiFi:L82 or later, and DataModule compactplus version A12 or later.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Infusion pumps are medical gadgets used to supply intravenous fluids, this kind of as vitamins and minerals and prescription drugs, into a patient’s body in controlled quantities, though SpaceStation is a configurable docking and interaction technique developed to accommodate up to four infusion pumps for use in a medical facility. The products run on a computer software ingredient referred to as SpaceCom, an embedded Linux process that runs either on the pump from in its smart battery pack or from within the SpaceStation.
In a nutshell, the flaws identified by McAfee permits an attacker to escalate privileges, see sensitive facts, upload arbitrary documents, and execute distant code execution —
- CVE-2021-33885 – Inadequate Verification of Facts Authenticity (CVSS 9.7)
- CVE-2021-33882 – Missing Authentication for Critical Function (CVSS 8.2)
- CVE-2021-33886 – Use of Externally-Controlled Format String (CVSS 7.7)
- CVE-2021-33883 – Cleartext Transmission of Sensitive Details (CVSS 7.1)
- CVE-2021-33884 – Unrestricted Add of File with Hazardous Sort (CVSS 5.8)
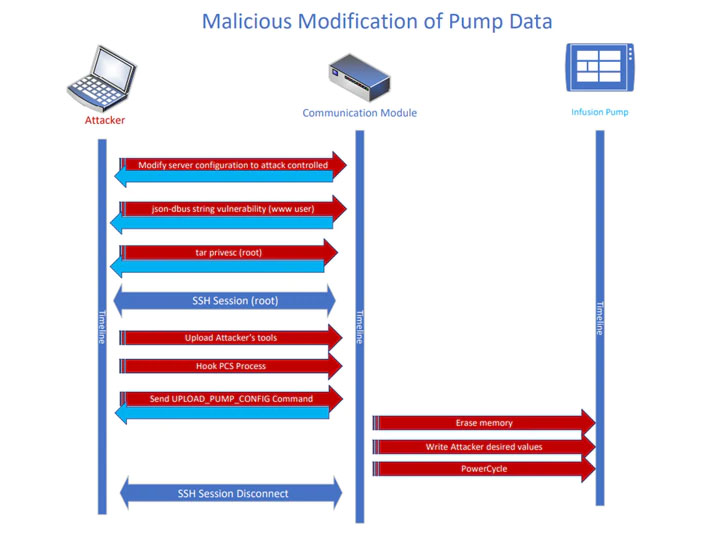
By chaining together the vulnerabilities, an adversary could “modify a pump’s configuration while the pump is in standby method, ensuing in an unanticipated dose of treatment becoming delivered to a patient on its up coming use – all with zero authentication,” McAfee Innovative Threat Study crew famous in a specialized deep-dive.
Put in another way, the weaknesses, which arise due to a absence of verification in the pump’s running process, could make it possible for any attacker to ship commands or information to it, therefore facilitating distant attacks that not only go undetected but also weaponize the device by altering the volume of medicine a patient is expected to get by infusion.

A single caveat of be aware is that the attacks can only be profitable when a pump is idle or in standby manner in involving infusions, not to mention this kind of unauthorized modifications to critical pump data necessitate that the menace actor 1st achieve an original foothold to the regional network, or perhaps carry out the intrusions over the internet in the occasion the pumps are specifically exposed — a scenario that is unlikely.
“All services utilizing SpaceCom, Battery Pack SP with WiFi, and DataModule compactplus ought to evaluate their IT infrastructure to be certain that a network zone principle has been carried out whereby critical systems, these kinds of as infusion pumps, are housed in separate (e.g., by firewalls or VLAN) environments which are not available immediately from the internet or by unauthorized buyers,” B. Braun stated in an advisory released on Might 14, 2021.
“Wireless networks really should be executed employing multi-factor authentication and marketplace common encryption and really should be geared up with Intrusion Detection Devices (IDS) and/or Intrusion Avoidance Programs (IPS),” the enterprise included.
Observed this write-up attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to go through much more exceptional written content we publish.
Some pieces of this short article are sourced from:
thehackernews.com


 Drug Dealers Get 27 Years After Police Crack EncroChat Comms
Drug Dealers Get 27 Years After Police Crack EncroChat Comms