A beforehand undisclosed “zero-click” exploit in Apple’s iMessage was abused by Israeli surveillance vendor NSO Team to circumvent iOS security protections and concentrate on nine Bahraini activists.
“The hacked activists involved three associates of Waad (a secular Bahraini political society), a few customers of the Bahrain Centre for Human Legal rights, two exiled Bahraini dissidents, and just one member of Al Wefaq (a Shiite Bahraini political society),” researchers from College of Toronto’s Citizen Lab reported in a report published nowadays, with four of the targets hacked by an actor it tracks as LULU and believed to be the governing administration of Bahrain.
Citizen Lab called the new exploit chain “FORCEDENTRY.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The improvement will come a minor over a month after an considerable investigation undertaken by a consortium of 17 media businesses discovered the popular use of NSO Group’s Pegasus “army-quality spyware” by authoritarian regimes to aid human legal rights violations by surveilling heads of condition, activists, journalists, and lawyers all around the entire world.
The corporation has considering the fact that temporarily blocked many governing administration customers globally from utilizing its technology as the corporation probes its possible misuse, even though also acknowledging that it “shut off 5 clients’ entry in the earlier numerous a long time right after conducting a human rights audit, and experienced finished ties with two in the past yr by itself,” according to the Washington Post.
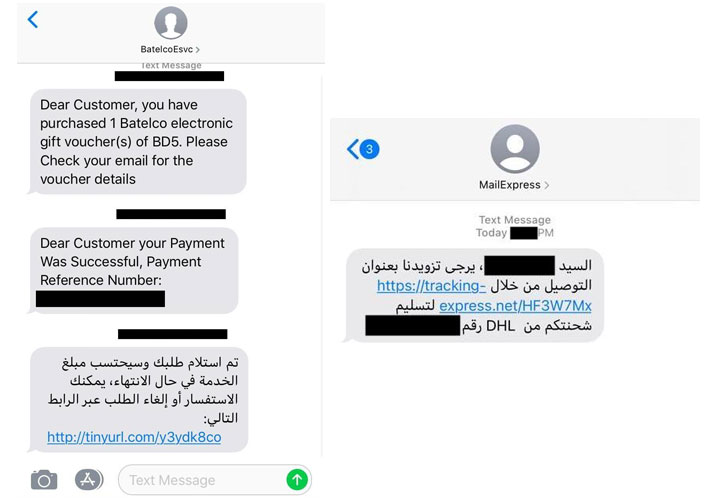
The newest disclosure is substantial, not least since the zero-click attack successfully works from the hottest versions of iOS, but also for the simple fact that it bypasses a new software program security aspect termed BlastDoor that Apple crafted into iOS 14 to prevent these kinds of intrusions by filtering untrusted information sent more than iMessage.
The tightly sandboxed provider was in-depth by Google Project Zero researcher Samuel Groß previously this January, noting that it is “written in Swift, a (typically) memory risk-free language which can make it substantially more durable to introduce traditional memory corruption vulnerabilities into the code foundation.” BlastDoor inspects inbound messages in a safe, sandboxed ecosystem, hence stopping any malicious code inside of a message from interacting with the rest of the running procedure or accessing person knowledge.

But the incredibly up coming month after its existence came to light, Citizen Lab reported it observed NSO Group deploying FORCEDENTRY — which Amnesty Worldwide dubbed “Megalodon” — in opposition to iOS versions 14.4 and 14.6 as a zero-day expressly engineered to get all-around the BlastDoor element by crashing IMTranscoderAgent, a provider responsible for transcoding and previewing photos in iMessage, to down load and render goods from the Pegasus infection server.
“Inspite of a 50 %-ten years of staying implicated in human rights abuses, NSO Group consistently statements that they are, in simple fact, committed to guarding human legal rights,” the researchers explained. “The corporation has even printed a ‘Human Rights Policy,’ a ‘Transparency and Responsibility Report,’ and claimed to subscribe to the United Nations Guiding Concepts on Business and Human Legal rights.
“The sale of Pegasus to Bahrain is especially egregious, looking at that there is major, longstanding, and documented evidence of Bahrain’s serial misuse of surveillance solutions including Trovicor, FinFisher, Cellebrite, and, now, NSO Group,” the Citizen Lab team extra.
Identified this report appealing? Abide by THN on Fb, Twitter and LinkedIn to study extra exceptional content material we write-up.
Some elements of this article are sourced from:
thehackernews.com

 Effective Threat-Hunting Queries in a Redacted World
Effective Threat-Hunting Queries in a Redacted World