A new Android trojan has been discovered to compromise Facebook accounts of more than 10,000 end users in at the very least 144 international locations because March 2021 by using fraudulent applications distributed via Google Play Keep and other 3rd-party app marketplaces.
Dubbed “FlyTrap,” the beforehand undocumented malware is thought to be part of a family members of trojans that employ social engineering tricks to breach Fb accounts as part of a session hijacking marketing campaign orchestrated by destructive actors operating out of Vietnam, in accordance to a report revealed by Zimperium’s zLabs today and shared with The Hacker Information.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Whilst the offending nine programs have since been pulled from Google Participate in, they keep on to be readily available in third-party application shops, “highlighting the risk of sideloaded programs to cellular endpoints and user facts,” Zimperium malware researcher Aazim Yaswant reported. The checklist of apps is as follows –
- GG Voucher (com.luxcarad.cardid)
- Vote European Football (com.gardenguides.plantingfree)
- GG Coupon Ads (com.free_coupon.gg_free_coupon)
- GG Voucher Adverts (com.m_application.app_moi_6)
- GG Voucher (com.totally free.voucher)
- Chatfuel (com.ynsuper.chatfuel)
- Net Coupon (com.absolutely free_coupon.net_coupon)
- Net Coupon (com.movie.net_coupon)
- EURO 2021 Official (com.euro2021)
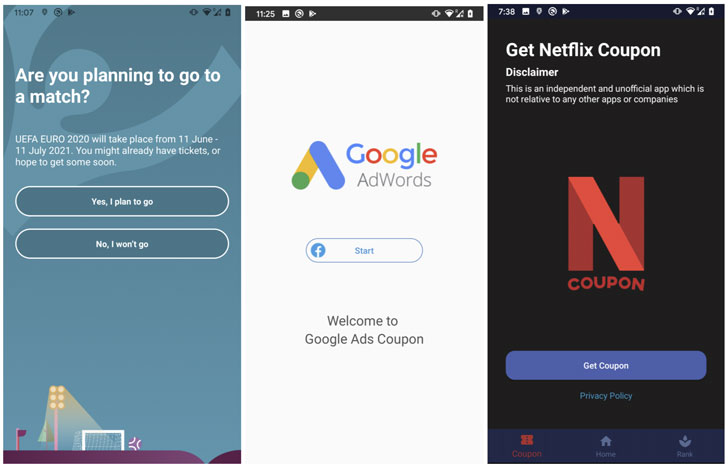
The destructive applications declare to provide Netflix and Google AdWords coupon codes and let end users vote for their favorite groups and players at UEFA EURO 2020, which took area among 11 June and 11 July 2021, only beneath the affliction that they log in with their Fb accounts to solid their vote, or acquire the coupon code or credits.
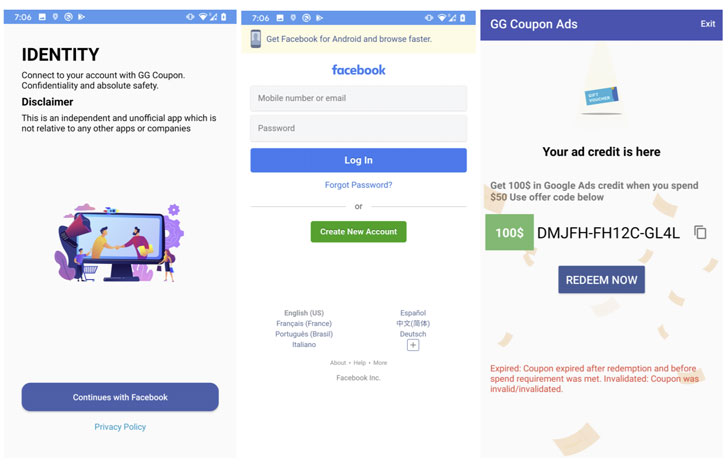
Once a person signs into the account, the malware is equipped to steal the victim’s Facebook ID, site, email deal with, IP tackle, and the cookies and tokens affiliated with the Facebook account, hence enabling the danger actor to have out disinformation strategies using the victim’s geolocation aspects or propagate the malware further more through social engineering approaches by sending own messages that contains back links to the trojan.

This is realized applying a method identified as JavaScript injection, in which “the application opens the legit URL inside a WebView configured with the ability to inject JavaScript code and extracts all the essential facts such as cookies, person account specifics, area, and IP handle by injecting destructive [JavaScript] code,” Yaswant explained.

Though the exfiltrated information is hosted on a command-and-regulate (C2) infrastructure, security flaws located in the C2 server could be exploited to expose the whole database of stolen session cookies to anyone on the internet, thereby placing the victims at even more risk.
“Malicious threat actors are leveraging frequent user misconceptions that logging into the correct area is always safe irrespective of the application applied to log in,” Yashwant stated. “The focused domains are well-liked social media platforms and this campaign has been extremely productive in harvesting social media session info of end users from 144 nations. These accounts can be made use of as a botnet for diverse applications: from boosting the acceptance of internet pages/web sites/items to spreading misinformation or political propaganda.”
Located this posting fascinating? Stick to THN on Fb, Twitter and LinkedIn to study more exclusive content we publish.
Some parts of this report are sourced from:
thehackernews.com

 May 2021 saw a 440% increase in phishing, the single largest phishing spike on record
May 2021 saw a 440% increase in phishing, the single largest phishing spike on record