Tainted VPN installers are being utilized to deliver a piece of surveillanceware dubbed EyeSpy as element of a malware marketing campaign that commenced in May well 2022.
It utilizes “components of SecondEye – a legitimate checking software – to spy on end users of 20Pace VPN, an Iranian-based mostly VPN services, by means of trojanized installers,” Bitdefender explained in an analysis.
A majority of the infections are stated to originate in Iran, with scaled-down detections in Germany and the U.S., the Romanian cybersecurity organization extra.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
SecondEye, in accordance to snapshots captured through the Internet Archive, statements to be a industrial monitoring software that can get the job done as a “parental command procedure or as an online watchdog.” As of November 2021, it really is supplied for sale everywhere involving $99 to $200.
It will come with a huge array of attributes that enables it to get screenshots, report microphone, log keystrokes, assemble documents and saved passwords from web browsers, and remotely control the equipment to run arbitrary commands.
SecondEye previously arrived beneath the radar in August 2022, when Blackpoint Cyber uncovered the danger actors’ use of its spyware modules and infrastructure for data and payload storage.
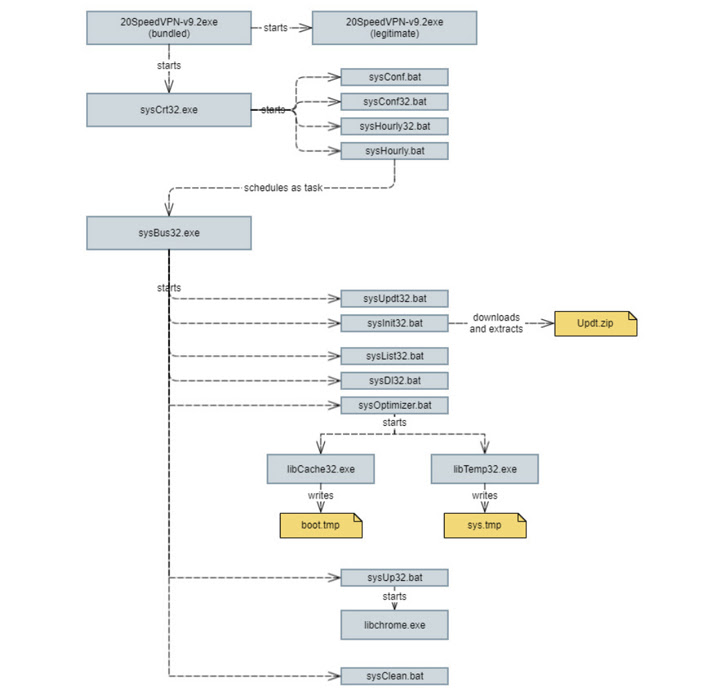
The latest attack chain starts when an unsuspecting user downloads a destructive executable from 20Pace VPN’s internet site, indicating two plausible situations: Either that the its servers have been breached to host the spyware or it is really a deliberate endeavor to spy on men and women who could download VPN apps to bypass internet blackouts in the state.
At the time installed, the legitimate VPN provider is introduced, even though also stealthily kicking off a prepare of nefarious actions in the track record so as to create persistence and down load future-stage payloads for harvesting own facts from the host.
“EyeSpy has the means to totally compromise on line privacy by way of keylogging and thieving of sensitive information and facts, this kind of as files, photographs, crypto wallets, and passwords,” Bitdefender researcher Janos Gergo Szeles stated. “This can lead to comprehensive account takeovers, identification theft and economical reduction.”
Found this post intriguing? Comply with us on Twitter and LinkedIn to study far more unique content material we put up.
Some components of this article are sourced from:
thehackernews.com


 Cisco Warns of Critical Vulnerability in End-of-Life Routers
Cisco Warns of Critical Vulnerability in End-of-Life Routers