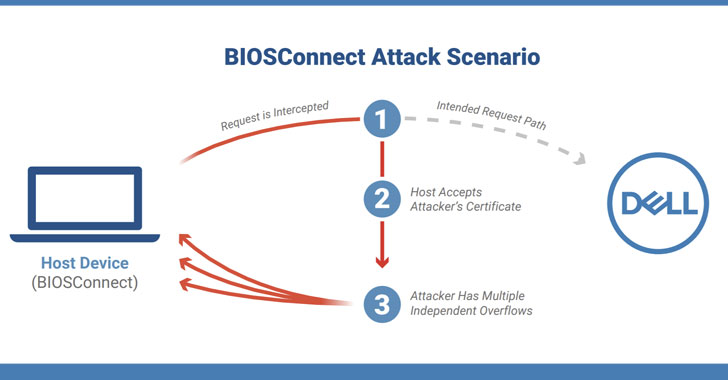
Cybersecurity scientists on Thursday disclosed a chain of vulnerabilities affecting the BIOSConnect element in Dell Shopper BIOS that could be abused by a privileged network adversary to obtain arbitrary code execution at the BIOS/UEFI stage of the impacted system.
“As the attacker has the skill to remotely execute code in the pre-boot surroundings, this can be employed to subvert the working technique and undermine elementary believe in in the gadget,” researchers from organization machine security company Eclypsium stated. “The nearly unrestricted command around a gadget that this attack can deliver will make the fruit of the labor nicely truly worth it for the attacker.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In all, the flaws affect 128 Dell products spanning throughout shopper and enterprise laptops, desktops, and tablets, totalling an believed 30 million unique units. Worse, the weaknesses also affect desktops that have Secure Boot enabled, a security function developed to avert rootkits from remaining put in at boot time in memory.
BIOSConnect gives network-based mostly boot recovery, letting the BIOS to hook up to Dell’s backend servers by means of HTTPS to obtain an functioning process impression, thus enabling buyers to get well their systems when the community disk image is corrupted, replaced, or absent.
Thriving exploitation of the flaws could signify reduction of gadget integrity, what with the attacker able of remotely executing malicious code in the pre-boot natural environment that could alter the original state of the functioning method and crack OS-level security protections.
The record of 4 flaws uncovered by Eclypsium is as follows —
- CVE-2021-21571 – Insecure TLS connection from BIOS to Dell, permitting a poor actor to stage a impersonate Dell.com and shipping and delivery malicious code again to the victim’s device
- CVE-2021-21572, CVE-2021-21573, and CVE-2021-21574 – Overflow vulnerabilities enabling arbitrary code execution
The blend of distant exploitation as nicely the ability to attain management in excess of the most privileged code on the unit could make these kinds of vulnerabilities a worthwhile goal for attackers, the researchers reported.

The issues had been reported to Dell by the Oregon-dependent firm on March 3, adhering to which server-aspect updates ended up rolled out on Could 28 to remediate CVE-2021-21573 and CVE-2021-21574. Dell has also unveiled shopper-side BIOS firmware updates to tackle the remaining two flaws.
In addition, the Pc maker has produced workarounds to disable equally the BIOSConnect and HTTPS Boot characteristics for prospects who are not able to implement the patches immediately.
“Efficiently compromising the BIOS of a product would give an attacker a high diploma of regulate in excess of a unit,” Eclypsium researchers reported. “The attacker could control the approach of loading the host running procedure and disable protections in order to continue to be undetected. This would let an attacker to establish ongoing persistence whilst controlling the optimum privileges on the device.”
Found this report intriguing? Comply with THN on Facebook, Twitter and LinkedIn to examine additional distinctive written content we post.
Some elements of this write-up are sourced from:
thehackernews.com

 Nuisance Call Company Fined £130,000 After Eight-Month Blitz
Nuisance Call Company Fined £130,000 After Eight-Month Blitz