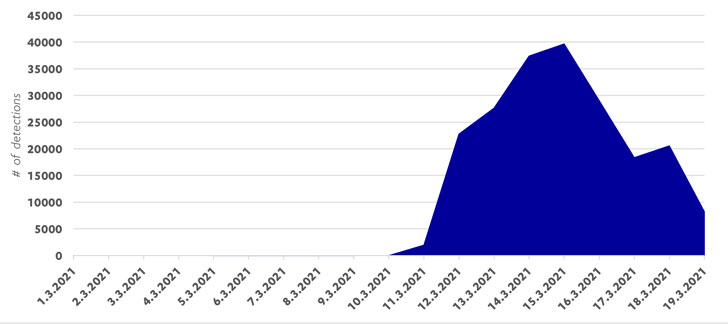
Far more than a 7 days right after Microsoft launched a 1-simply click mitigation device to mitigate cyberattacks concentrating on on-premises Trade servers, the corporation disclosed that patches have been used to 92% of all internet-dealing with servers influenced by the ProxyLogon vulnerabilities.
The growth, a 43% enhancement from the prior 7 days, caps off a whirlwind of espionage and malware strategies that strike 1000’s of corporations throughout the world, with as quite a few as 10 sophisticated persistent risk (APT) groups opportunistically going immediately to exploit the bugs.
In accordance to telemetry data from RiskIQ, there are around 29,966 cases of Microsoft Trade servers however exposed to attacks, down from 92,072 on March 10.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Even though Exchange servers had been less than assault by a number of Chinese-joined state-sponsored hacking groups prior to Microsoft’s patch on March 2, the release of community proof-of-idea exploits fanned a feeding frenzy of bacterial infections, opening the doorway for escalating attacks like ransomware and hijacking web shells planted on unpatched Microsoft Trade servers to supply cryptominers and other malware.
“To make issues even worse, evidence-of-idea automated attack scripts are staying made publicly obtainable, creating it possible for even unskilled attackers to rapidly attain remote manage of a vulnerable Microsoft Trade Server,” cybersecurity organization F-Protected noted in a create-up very last 7 days.
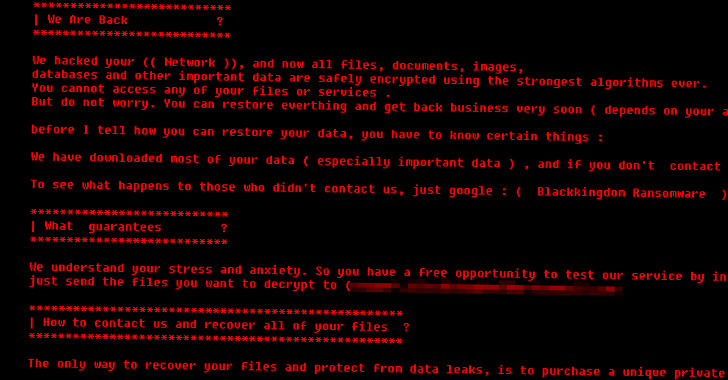
In the months given that Microsoft very first unveiled its patches, at least two different strains of ransomware have been uncovered as leveraging the flaws to put in “DearCry” and “Black Kingdom.”
Cybersecurity company Sophos’ evaluation of Black Kingdom paints the ransomware as “to some degree rudimentary and amateurish in its composition,” with the attackers abusing the ProxyLogon flaw to deploy a web shell, using it to issue a PowerShell command that downloads the ransomware payload, which encrypts the documents and requires a bitcoin ransom in exchange for the non-public critical.
“The Black Kingdom ransomware concentrating on unpatched Trade servers has all the hallmarks of remaining produced by a inspired script-kiddie,” Mark Loman, director of engineering at Sophos, reported. “The encryption equipment and procedures are imperfect but the ransom of $10,000 in bitcoin is small plenty of to be profitable. Each individual menace really should be taken severely, even seemingly low-high quality types.”
The volume of attacks even in advance of the community disclosure of ProxyLogon has prompted specialists to investigate if the exploit was shared or marketed on the Dark Web, or a Microsoft associate, with whom the business shared data about the vulnerabilities by means of its Microsoft Lively Protections System (MAPP), possibly unintentionally or purposefully leaked it to other groups.
Observed this write-up fascinating? Abide by THN on Facebook, Twitter and LinkedIn to go through additional exceptional information we article.
Some areas of this article are sourced from:
thehackernews.com

 Forcing Self-Service Password Reset (SSPR) Registration to Increase ROI
Forcing Self-Service Password Reset (SSPR) Registration to Increase ROI