In however a further scenario of bring your own vulnerable driver (BYOVD) attack, the operators of the BlackByte ransomware are leveraging a flaw in a reputable Windows driver to bypass security remedies.
“The evasion method supports disabling a whopping list of over 1,000 motorists on which security products and solutions rely to give security,” Sophos threat researcher Andreas Klopsch claimed in a new specialized write-up.
BYOVD is an attack strategy that will involve risk actors abusing vulnerabilities in reputable, signed drivers to reach thriving kernel-mode exploitation and seize manage of compromised machines.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Weaknesses in signed drivers have been increasingly co-opted by nation-state threat groups in recent yrs, which include Slingshot, InvisiMole, APT28, and most not long ago, the Lazarus Team.
BlackByte, considered to be an offshoot of the now-discontinued Conti group, is part of the major recreation cybercrime crews, which zeroes in on big, large-profile targets as portion of its ransomware-as-a-assistance (RaaS) scheme.
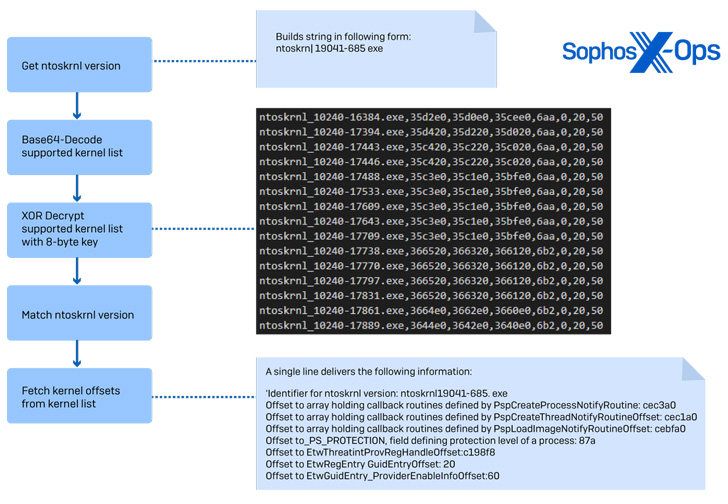
According to the cybersecurity agency, modern attacks mounted by the group have taken advantage of a privilege escalation and code execution flaw (CVE-2019-16098, CVSS score: 7.8) impacting the Micro-Star MSI Afterburner RTCore64.sys driver to disable security goods.

What is actually additional, an analysis of the ransomware sample has uncovered a number of similarities amongst the EDR bypass implementation and that of a C-based mostly open source device identified as EDRSandblast, which is designed to abuse vulnerable signed drivers to evade detection.
BlackByte is the latest ransomware relatives to embrace the BYOVD process to accomplish its objectives, right after RobbinHood and AvosLocker, the two of which have weaponized bugs in gdrv.sys (CVE-2018-19320) and asWarPot.sys to terminate processes involved with endpoint protection software.
To protect towards BYOVD attacks, it really is advised to maintain observe of the motorists put in on the methods and ensure they are up-to-day, or opt to blocklist drivers acknowledged to be exploitable.
Identified this report appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through additional exclusive content material we submit.
Some sections of this report are sourced from:
thehackernews.com


 FBI and CISA Publish Advisory on Malicious Cyber Activity Against Election Infrastructure
FBI and CISA Publish Advisory on Malicious Cyber Activity Against Election Infrastructure