Email phishing attacks have been on the increase all through the COVID-19 pandemic this year. Today’s columnist, Kevin O’Brien of GreatHorn, provides a 4-stage email security approach. (Credit history: GreatHorn)
Companies of all sizes experience the exact same extremely challenging obstacle: the poor guys will often check out to attack email.
Buyers functioning on any email system will have to communicate efficiently and securely though supporting their group battle towards phishing, account takeovers, details breaches, and enterprise email compromises. Corporations can do this by developing a multi-layered solution to security that everybody understands and understands like a second language.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
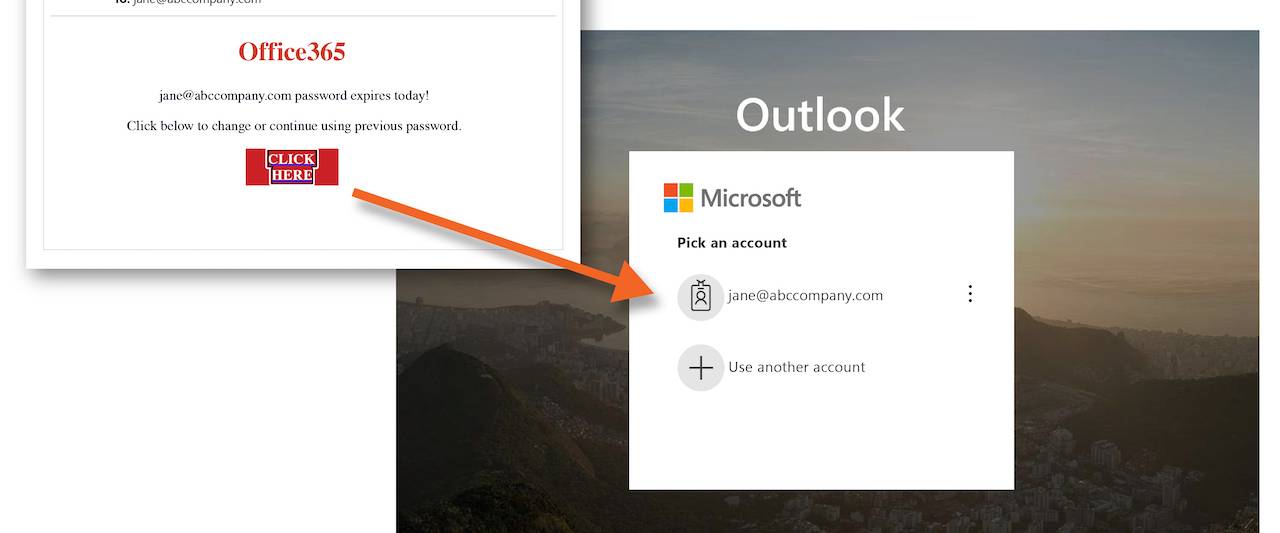
All those who don’t value email security are very likely missing out on alternatives to defend the corporation and educate employees on how to do the similar. Our 2020 Phishing Attack Landscape report uncovered that 38 per cent of organizations said within just the earlier calendar year, anyone inside their business experienced fallen victim to a phishing attack. And 53 p.c of organizations said they experienced noticed an uptick in email phishing attacks all through the COVID-19 pandemic.
When email compromise strategies continue to be the exact same – thieving qualifications, pretending to be an individual genuine, and impersonating domains/corporations – the charge at which they are happening increases. When a menace receives delivered through email, security teams must answer promptly to mitigate that attack prior to it leads to hurt that requires time and sources to incorporate and get under manage. Automating the response and making sure workforce know how to recognize and do this at a moment’s discover can help mitigate threats at scale.
But what tends to make an email security merchandise helpful? It revolves arounds four elementary tenets: analyze, detect, guard, and respond.
Review
Start by creating a deep comprehension of the organization’s environment. This contains end users, conversation styles, relationship power amongst senders and recipients, resources, unique consumer risk profiles, and information. Security groups have to acquire whole visibility of these factual things and how, the place and to whom they join.
Getting the most actuality-based facts available helps to evaluate and make educated choices all around comparable behaviors. Without having crystal clear visibility, it turns into a lot more hard to detect and identify what steps to just take. A lot of sellers produce a “black box” of their policies. This will make it even much more challenging for businesses to have total visibility. This deficiency of transparency removes the ability for businesses to refine insurance policies, dependent on granular risk factors, to produce the best detection for their business.
Detect
Security groups will have to detect an attack quickly and also analyze it to reduce other this sort of attacks and quarantine attacks promptly, blocking them just before they arrive at the end consumer. As an instance, adaptive menace analytics systems integrate device learning and knowledge science to learn the most repeated conversation designs one of a kind to each receiver and sender. When security groups do this, it’s significantly less difficult to detect email anomalies and suspicious articles. It is vital to capture and stop events in real-time and avert them from turning out to be worse.
Protect
Security teams also will need to develop and apply techniques and techniques to enable restrict accesses and mitigate possible incidents. This starts with in-the-instant coaching, and reducing attack engagement by warning people of potential threats throughout the attack. Assessment gets to be vital here and submit-shipping and delivery to aid end users have an understanding of what the attack, how to report phishing tries, and how to avoid it in the foreseeable future.
In the shield phase, security execs observe network obtain and set up procedures to guarantee the suitable email network configurations are in location for the total security of the firm. Consciousness training or user training performs a especially sizeable position listed here simply because when it arrives to a phishing attack and spoofing email, we do not know what we do not know. Staff are often the most vital asset to guarding the corporation if they are skilled properly.
Respond
In the occasion of an email attack, the organization ought to react quickly to mitigate these threats. Security professionals do this by automating incident reaction and remediation procedures. Obtaining this kind of plan in put places the group in a much better situation to act swiftly in the function of an attack and restrict the impact. Specified the form of attacks, attackers can launch in a make a difference of minutes, security teams don’t have much time to manually mitigate threats.
Develop a reaction plan that identifies the most useful details promptly and carry out all subsequent routines in a way that removes any negative outcomes and guarantees lessons are acquired and ideas implemented into the long term reaction plan.
This four-period system can assist security groups create an efficient email security approach. The means to assess, detect, secure and respond at the minute of risk assists security teams abide by a fact-based strategy to email security. Making sure the staff has a deep understanding of the company’s risk profile and understands the company’s total security posture can support the security team link to business enterprise processes that lessen risk.
Kevin O’Brien, co-founder and CEO, GreatHorn
Some sections of this write-up are sourced from:
www.scmagazine.com

 The pandemic brings new risk, even as nature of cyber threats remain pretty familiar
The pandemic brings new risk, even as nature of cyber threats remain pretty familiar