Cybersecurity researchers on Thursday disclosed two distinctive style and design and implementation flaws in Apple’s crowdsourced Bluetooth area monitoring process that can lead to a spot correlation attack and unauthorized entry to the area heritage of the previous 7 days, therefore by deanonymizing customers.
The results are a consequence of an exhaustive assessment carried out by the Open Wireless Website link (OWL) job, a staff of researchers from the Safe Mobile Networking Lab at the Technological College of Darmstadt, Germany, who have traditionally taken aside Apple’s wi-fi ecosystem with the intention of identifying security and privacy issues.
In reaction to the disclosures on July 2, 2020, Apple is explained to have partly addressed the issues, stated the scientists, who made use of their have knowledge for the study citing privacy implications of the examination.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
How Obtain My Will work?
Apple devices come with a feature named Locate My that can make it easy for consumers to identify other Apple equipment, which include iPhone, iPad, iPod contact, Apple Check out, Mac, or AirPods. With the forthcoming iOS 14.5, the firm is predicted to incorporate aid for Bluetooth tracking products — known as AirTags — that can be attached to merchandise like keys and wallets, which in switch can be utilised for monitoring uses proper from in the Come across My app.
What is a lot more appealing is the technology that undergirds Find My. Termed offline locating and introduced in 2019, the location tracking feature broadcasts Bluetooth Small Electricity (BLE) indicators from Apple units, permitting other Apple gadgets in shut proximity to relay their locale to Apple’s servers.
Place in another way, offline loading turns every mobile device into a broadcast beacon made explicitly to shadow its movements by leveraging a crowdsourced locale tracking mechanism which is equally end-to-conclude encrypted and nameless, so considerably so that no third-party, including Apple, can decrypt individuals locations and make a heritage of each and every user’s whereabouts.
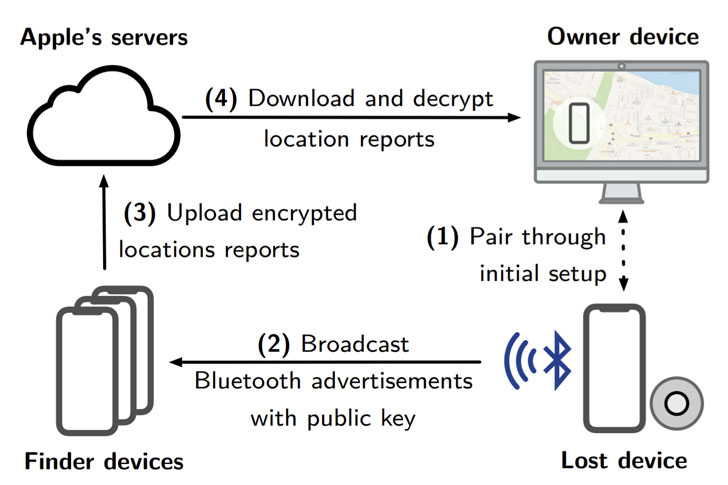
This is attained by way of a rotating critical scheme, precisely a pair of public-personal keys that are generated by every single gadget, which emits the Bluetooth signals by encoding the community crucial alongside with it. This key facts is subsequently synchronized by way of iCloud with all other Apple equipment connected to the similar consumer (i.e., Apple ID).
A close by iPhone or iPad (with no relationship to the authentic offline system) that picks up this concept checks its very own spot, then encrypts the data applying the aforementioned public crucial just before sending it to the cloud together with a hash of the community key.
In the remaining phase, Apple sends this encrypted place of the shed product to a 2nd Apple unit signed in with the same Apple ID, from where the operator can use the Discover My app to decrypt the reviews making use of the corresponding personal crucial and retrieve the previous known site, with the companion machine uploading the exact same hash of the public critical to discover a match in Apple’s servers.
Issues with Correlation and Monitoring
Because the strategy follows a general public vital encryption (PKE) setup, even Apple simply cannot decrypt the site as it’s not in possession of the private key. Whilst the business has not explicitly discovered how generally the key rotates, the rolling critical pair architecture can make it tough for malicious events to exploit the Bluetooth beacons to monitor users’ movements.
But OWL scientists mentioned the layout enables Apple — in lieu of becoming the company service provider — to correlate distinctive owners’ areas if their spots are described by the identical finder equipment, properly letting Apple to construct what they connect with a social graph.
“Regulation enforcement businesses could exploit this issue to deanonymize members of (political) demonstrations even when contributors place their telephones in flight mode,” the scientists explained, including “malicious macOS applications can retrieve and decrypt the [offline finding] spot reports of the last seven times for all its users and for all of their gadgets as cached rolling ad keys are stored on the file technique in cleartext.”
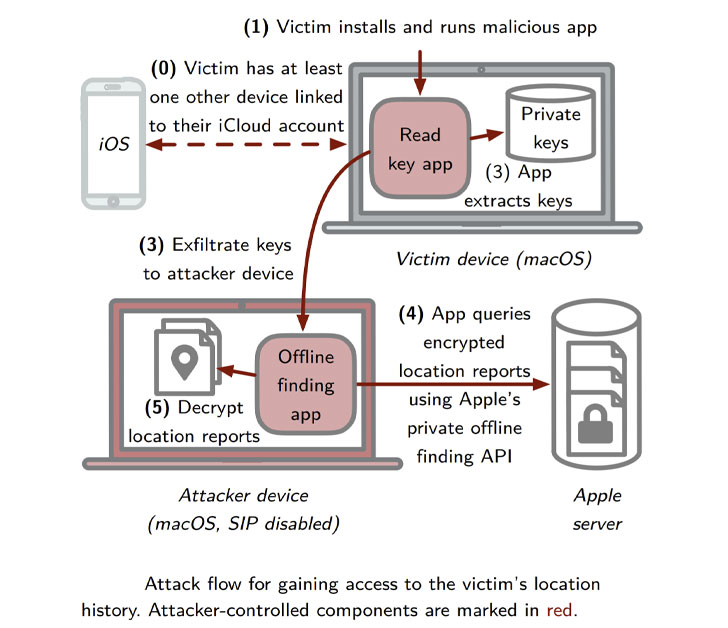
In other words and phrases, the macOS Catalina vulnerability (CVE-2020-9986) could allow an attacker to accessibility the decryption keys, employing them to obtain and decrypt location reports submitted by the Come across My network, and finally identify and recognize their victims with substantial accuracy. The weakness was patched by Apple in November 2020 (edition macOS 10.15.7) with “enhanced obtain limits.”
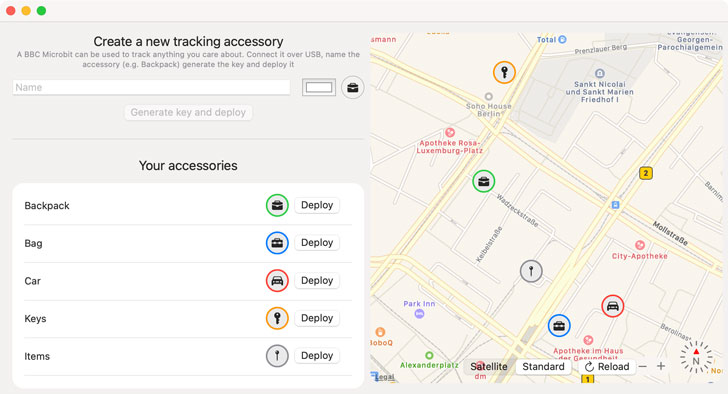
A 2nd final result of the investigation is an application which is intended to enable any person make an “AirTag.” Termed OpenHaystack, the framework will allow for tracking particular Bluetooth devices by way of Apple’s enormous Uncover My network, enabling buyers to make their individual monitoring tags that can be appended to actual physical objects or integrated into other Bluetooth-able equipment.
This is not the to start with time scientists from Open Wi-fi Connection (OWL) have uncovered flaws in Apple’s closed-supply protocols by indicates of reverse engineering.
In May perhaps 2019, the researchers disclosed vulnerabilities in Apple’s Wi-fi Immediate Website link (AWDL) proprietary mesh networking protocol that permitted attackers to monitor consumers, crash units, and even intercept data files transferred concerning units by way of man-in-the-center (MitM) attacks.
This was later adapted by Google Task Zero researcher Ian Beer to uncover a critical “wormable” iOS bug final year that could have created it possible for a remote adversary to obtain full control of any Apple system in the vicinity more than Wi-Fi.
Identified this report exciting? Comply with THN on Fb, Twitter and LinkedIn to read through extra distinctive articles we publish.
Some pieces of this report are sourced from:
thehackernews.com

 D-Link, IoT Devices Under Attack By Tor-Based Gafgyt Variant
D-Link, IoT Devices Under Attack By Tor-Based Gafgyt Variant