A sweeping and “highly lively marketing campaign” that originally established its sights on Myanmar has broadened its target to strike a variety of targets positioned in the Philippines, in accordance to new research.
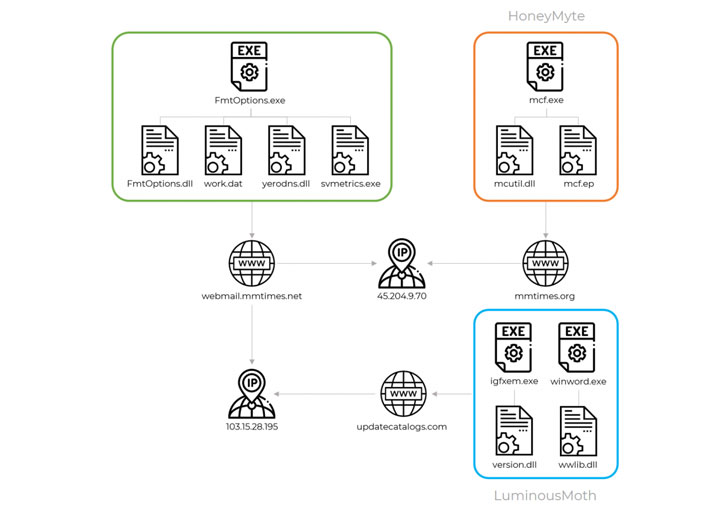
Russian cybersecurity agency Kaspersky, which initial noticed the bacterial infections in Oct 2020, attributed them to a menace actor it tracks as “LuminousMoth,” which it connected with medium to significant self esteem to a Chinese point out-sponsored hacking group called HoneyMyte or Mustang Panda, offered its noticed victimology, tactics, and techniques.
About 100 affected victims have been identified in Myanmar, although the range of victims jumped to practically 1,400 in the Philippines, while the scientists noted that the genuine targets had been only a fraction of the initial figures, like governing administration entities located the two inside of the two nations around the world and abroad.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The goal of the attacks is to have an effect on a wide perimeter of targets with the goal of hitting a decide on couple of that are of strategic desire, researchers Mark Lechtik, Paul Rascagneres, and Aseel Kayal reported. Set otherwise, the intrusions are simultaneously huge-ranging and narrow-targeted, enabling the menace acor to siphon intelligence from substantial-profile targets.
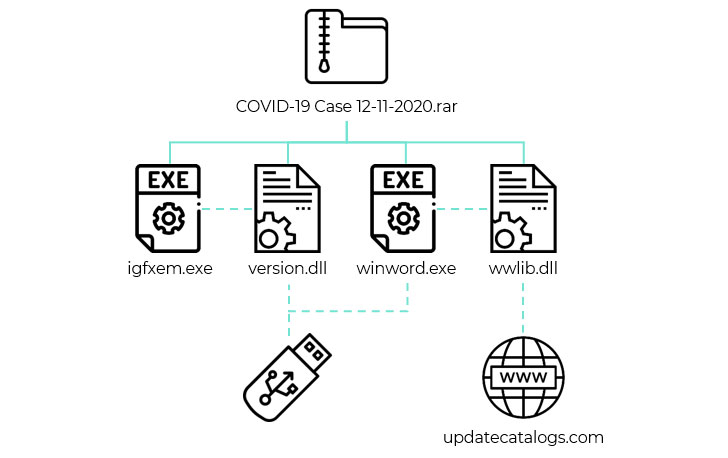
The infection vector used in the campaign will involve sending a spear-phishing email to the target containing a Dropbox down load url that, when clicked, leads to a RAR archive that is made to mimic a Phrase document. The archive file, for its section, will come with two malicious DLL libraries (“version.dll” and “wwlib.dll”) and two corresponding executable documents that operate the malware.
On successfully getting a foothold, an choice an infection chain noticed by Kaspersky leverages detachable USB drives to propagate the malware to other hosts with the enable of “version.dll”. On the other hand, the intent of “wwlib.dll” is to obtain a Cobalt Strike beacon on the compromised Windows program from a remote attacker-controlled area.
In some circumstances, the attacks included an more step wherein the danger actor deployed a publish-exploitation tool in the type of a signed-but-rogue version of Zoom online video conferencing app, making use of it to hoover sensitive information to a command-and-control server. A valid electronic certificate was used to signal the software program in an work to move off the software as benign. Also spotted on some contaminated equipment was a next submit-exploitation utility that steals cookies from Google Chrome browser.

LuminousMoth’s malicious cyber operations and its attainable ties to Mustang Panda APT may perhaps also be an attempt to change methods and update their defensive measures by re-tooling and developing new and mysterious malware implants, Kaspersky famous, as a result possibly obscuring any ties to their previous actions and blurring their attribution to identified teams.
“APT actors are regarded for the commonly qualified character of their attacks. Normally, they will handpick a established of targets that in convert are managed with almost surgical precision, with infection vectors, destructive implants and payloads staying tailor-made to the victims’ identities or environment,” Kaspersky scientists reported.
“It really is not usually we notice a huge-scale attack done by actors fitting this profile, commonly due to these types of attacks currently being noisy, and consequently putting the underlying operation at risk of staying compromised by security solutions or scientists.”
Located this report interesting? Comply with THN on Fb, Twitter and LinkedIn to examine additional distinctive written content we put up.
Some sections of this post are sourced from:
thehackernews.com


 New ransomware group is attacking US firms and educational establishments
New ransomware group is attacking US firms and educational establishments