Cybersecurity researchers on Tuesday uncovered a new espionage campaign focusing on media, construction, engineering, electronics, and finance sectors in Japan, Taiwan, the U.S., and China.
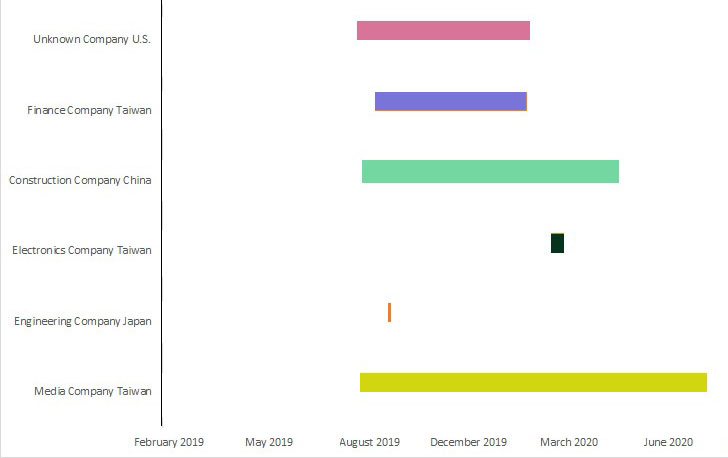
Linking the attacks to Palmerworm (aka BlackTech) — probably a China-based advanced persistent danger (APT) — Symantec’s Menace Hunter Team said the 1st wave of exercise related with this marketing campaign started last yr in August 2019, even though their final motivations however continue being unclear.
“Even though we are unable to see what Palmerworm is exfiltrating from these victims, the team is thought of an espionage group and its most likely inspiration is considered to be stealing info from targeted firms,” the cybersecurity organization reported.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Among the many victims infected by Palmerworm, the media, electronics, and finance businesses had been all dependent in Taiwan, even though an engineering corporation in Japan and a design business in China ended up also specific.
In addition to working with tailor made malware to compromise companies, the group is claimed to have remained active on the Taiwanese media firm’s network for a yr, with indicators of activity observed as recently as August 2020, likely implying China’s continued desire in Taiwan.
This is not the initially time the BlackTech gang has gone just after company in East Asia. A 2017 examination by Trend Micro found the team to have orchestrated three campaigns — PLEAD, Shrouded Crossbow, and Waterbear — with an intent to steal private paperwork and the target’s intellectual house.
Stating that some of the determined malware samples matched with PLEAD, the scientists explained they identified four beforehand undocumented backdoors (Backdoor.Consock, Backdoor.Waship, Backdoor.Dalwit, and Backdoor.Nomri), indicating “they may be newly developed tools, or the evolution of more mature Palmerworm resources.”
The brand name new tailor made malware toolset alone would have designed the attribution difficult if it were being not for the use of twin-use instruments (such as Putty, PSExec, SNScan, and WinRAR) and stolen code-signing certificates to digitally sign its destructive payloads and thwart detection, a tactic that it has been located to make use of right before.
An additional element which is significantly not also crystal clear is the infection vector by itself, the approach Palmerworm has utilized to attain initial entry to the victim networks. The team, nonetheless, has leveraged spear-phishing email messages in the previous to deliver and install their backdoor, both in the form of an attachment or by way of inbound links to cloud storage solutions.
“APT teams proceed to be remarkably active in 2020, with their use of twin-use equipment and residing-off-the-land ways generating their exercise at any time more durable to detect, and underlining the want for prospects to have a comprehensive security solution in spot that can detect this kind of exercise,” Symantec reported.
Observed this article interesting? Adhere to THN on Fb, Twitter and LinkedIn to read much more unique content we publish.
Some parts of this article is sourced from:
thehackernews.com

 As tech reaches end of life, hackers are watching
As tech reaches end of life, hackers are watching