Cybersecurity researchers nowadays unveiled a elaborate and specific espionage attack on possible government sector victims in South East Asia that they believe that was carried out by a innovative Chinese APT team at the very least considering the fact that 2018.
“The attack has a advanced and complete arsenal of droppers, backdoors and other applications involving Chinoxy backdoor, PcShare RAT and FunnyDream backdoor binaries, with forensic artefacts pointing toward a advanced Chinese actor,” Bitdefender stated in a new analysis shared with The Hacker News.
It truly is really worth noting that the FunnyDream campaign has been formerly joined to substantial-profile authorities entities in Malaysia, Taiwan, and the Philippines, with a greater part of victims positioned in Vietnam.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
According to the scientists, not only all around 200 machines exhibited attack indicators involved with the marketing campaign, proof points to the reality the menace actor might have compromised area controllers on the victim’s network, letting them to shift laterally and possibly get handle of other devices.
The analysis has yielded tiny to no clues as to how the infection occurred, whilst it is suspected that the attackers used social engineering lures to trick unwitting users into opening destructive information.
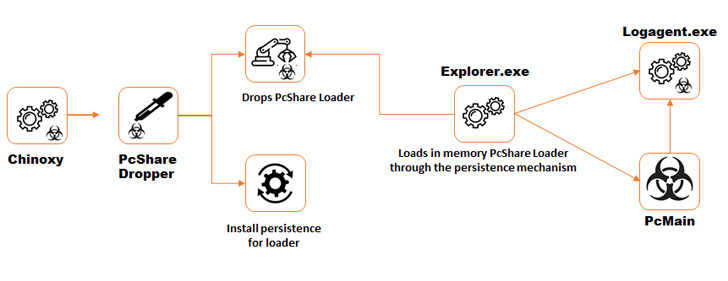
On gaining an original foothold, numerous resources were uncovered to be deployed on the infected method, which includes the Chinoxy backdoor to obtain persistence as well as a Chinese distant access Trojan (RAT) termed PcShare, a modified variant of the very same tool accessible on GitHub.
Aside from working with command-line utilities this sort of as tasklist.exe, ipconfig.exe, systeminfo.exe, and netstat to gather program facts, a selection of other folks — ccf32, FilePak, FilePakMonitor, ScreenCap, Keyrecord, and TcpBridge — had been set up to acquire data files, capture screenshots, logging keystrokes, and exfiltrate the gathered data to an attacker-controlled server.
The investigation also uncovered the use of the aforementioned FunnyDream backdoor starting up in May possibly 2019, which comes with various capabilities to amass user knowledge, thoroughly clean traces of malware deployment, thwart detection and execute destructive instructions, the effects of which were being transmitted back again to command-and-command (C&C) servers situated in Hong Kong, China, South Korea, and Vietnam.
“Attributing APT fashion attacks to a particular team or nation can be exceptionally challenging, mostly for the reason that forensic artefacts can occasionally be planted deliberately, C&C infrastructure can reside anywhere in the planet, and the tools made use of can be repurposed from other APT groups,” the researchers concluded.
“Through this investigation, some forensic artifacts feel to recommend a Chinese-speaking APT team, as some of the methods uncovered in numerous binaries had a language set to Chinese, and the Chinoxy backdoor employed all through the marketing campaign is a Trojan recognized to have been employed by Chinese-talking danger actors.”
Located this report fascinating? Stick to THN on Facebook, Twitter and LinkedIn to read more distinctive articles we post.
Some sections of this posting are sourced from:
thehackernews.com

 The top 12 password-cracking techniques used by hackers
The top 12 password-cracking techniques used by hackers